Abstract
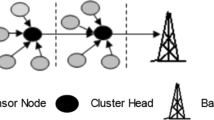
Wireless Sensor Network is a wide area monitoring tools supporting for Scientific Research, Low-power microscopic sensors. WSN uses limited resource memory, computation power, bandwidth, and energy. The Cluster Routing protocol is the best methodologies for energy efficiency in the wireless sensor network. Cluster Routing Protocols are used to form a cluster creation on the selection of cluster head (CH). Then the data packets are sending from one CH to another CH and finally data packets are send to the base station. CHs are selected by using the setup phase. This system proposed a multi hop transmission, where the data packets are send from one hop to another hop. Finally these data packets are transmitted to the base station. To transmit the packets from source sensor to wireless sensor network base station via the cluster head, using the fuzzy logic type 1with three parameters such as trust factor and distance. The fuzzy logic predicts the nodes, which is having high trust factor, and near to the base station CH will be selected as best forwarder by using Type 1 fuzzy logic. It will direct to increase the life time of network plus reduce the overhead of network.
Similar content being viewed by others
Avoid common mistakes on your manuscript.
1 Introduction
Wireless Sensor Networks consist of diminutive contemptible, decreased power of sensor nodes which are organized in observation neighborhood with extensive transmission range [1]. It consists of battery with restricted energy and not easy to exchange or recharge. Therefore, the main challenge of Wireless Sensor Network [2] is to create stability of the network load, to diminish entire energy consumption and to extend the lifetime of the network. The extended algorithm will improve the existence of Wireless Sensor Networks [3]. Cluster routing protocol is commonly used for improving network life time. The Cluster Head (CH) is randomly formed in LEACH [4]. Dominant Set Formation [5] is used to form the best Cluster Head using Tree Based Network Formation [6]. To get the solution with the problem of random formation, many researches focus on improvement in various kinds of algorithm for efficient distribution of the CHs, among network using Memory based Broadcast Model [7]. MR_LEACH [8] the extension of LEACH protocol proposed to improve the lifetime based on multi-hop communication for packet broadcasting to the sink. A Lot of algorithms are proposed for cluster formation such as Threshold Sensitive Energy Efficient Network (TEEN) [9], Energy-efficient Multi-sink Clustering Algorithm (EMCA) [10], Bandwidth and Delay Aware Routing [11], Fuzzy logic based energy efficient hierarchical clustering [12], Fuzzy logic [13], CHEF [14], SIPTAN [15], EEUC [16], EAUCF [17], IFUC [18] and EUDIS [19], PEGASIS [20], PEGASIS-ACO [21], type-1 fuzzy set [22], type-2 fuzzy set [23], HEED [24], A-SMART [25], TBOR [26], ECBK [27], SCSBE [28], EET2FL [29].
The fuzzy logic predicts the nodes, which is having high Trust Factor, energy and minimum distance to sink [30]. The predicted node select by cluster head to route the packets from cluster head to base using Type 1 fuzzy logic. It will lead to increase the life time of network and reduce the overhead of network [31]. Fuzzy logic systems (FLSs), [32, 33] and Type 2 Fuzzy logic systems [34, 35] can be used to create the best energy efficient routing model. Fuzzy based clustering routing protocol [36] is employed to discover the Cluster Heads and kernal optimization [37] is used for multihop routing. Moreover, two issues called residual energy [38] number of adjoining nodes are the contributions to compute the possibility [39]. The Fuzzy Logic based algorithm is used to generate a connection link to all the Cluster Heads [40]. The fuzzy set is differentiated with different membership functions [41].
2 Related works
In the current years numerous cluster based routing protocols are used in the WSN. In this LEACH is the first and fashionable protocol for increase the lifespan of the network it consist of two phases for all round. Every formation begins with a set-up phase wherein contain cluster head election and cluster formation take place [42].
A node n finds the random values between 0 and 1 and calculate Threshold T(n), where, PCH is the Cluster Head probability, r is the number of the current head formation state from the set of sensor nodes. In this single –hop [43] communication is not suitable for large scale network. The algorithms proposed such as [44, 45], where Cluster Heads cooperated with the neighborhood for transmitting packets. EEUC [46] is formed from various parameters like energy distance, etc. In multi hop [47, 48] routing selection for best forwarded node is major issue for designing cluster protocol, in this chain topology architecture is another important protocol for elect best CH for transmitting the data in this each node transmit the data packet [49, 50].
3 EET2FL cluster routing protocol
In the initial state, all CHs are selected by the sink node in EET2FL clustering algorithm. In the literature, many of the cluster head formation are included on energy, range, distance, probability and some other factors. Beyond that, EET2FL clustering algorithm considers three factors such as energy, weight and the distance to the sink of every node for CH election.
The residual energy is calculated from the balance energy of a sensor node, and initially all the nodes are having the same energy and the node which is having highest energy will be selected as CHs. Second, the node weight is assigned based on thenumber of packets in the node with hop count of node from the sink. After the deployment, the sink node broadcast the message to all the nodes to identify the position, energy, distance. Due to this transmission of Message, the sink node losses some energy at the same time each sensor node losses some energy for receiving the data. This message broadcast is called as Path Discovery. After that, each sensor node’s energy will vary. That’s why based on the packet and hop count will assign the weight to all sensor nodes. Eventually, the nodes far left from the sink will need additional energy for data diffusion to the sink, and after that expires quickly. Taking into consideration the residual energy, weight and the space to the sink of each node for CHs selection, the sink broadcasts a control signal to all the sensor nodes. The sensor nodes start collecting the data from the environment, every sensor node sends the distance to the sink along with residual energy information to the sink based on the signal strength. In the same way, for each round, every node reports its residual energy to the sink. Fuzzy Logic System is described in Fig. 2.
Figure 1 describes the transition state for hidden and functional state model. The sensor generates the channel allocation using probabilistic approach.
Hn denotes the Hidden state with available clusters with time period of t.
Fn denotes the Functional state with available clusters with time period of t.
The Available Cluster (AC) is calculated using the parameters such as the total number of frame slots Sd , Total sub slots in frame St, Time duration Ft, number of broadcast slots ω.
The fuzzy logic system has three input variables including the residual energy, weight and the distance to the sink of each node, and the two output variables are the probability chance of node becoming tentative CH and the competition radius of each candidate CH. The role of fuzzifier is mapping each crisp input value on to fuzzy set. The FIS used in this work is Mamdani fuzzy inference system.This model produces the output based on the input parameters used in the control system. The input linguist control rule is based on rules formed by an experienced operation.
Fuzzy type 2 Fuzzifier takes three types of input parameters for every sensor nodes as residual energy, weight and distance. The interference engine analyzes the input with fuzzy rules and membership functions using type 2.
The neighbor node, nearer to sink can be elected by the best forwarding node. The distance can be calculated by using the formula,
Where (k, Sink) denotes the distance from node k to the sink and Neighbor (i) demonstrates the list of source node i.
On the assumption that node k is selected as the next hop and the data is transmitted to it, ETR is Energy used to broadcast data, d is the distance, the expected Residual Energy (RE) of sensor node i is
Using the expected residual energy from (6) and (7), sensor i can calculate the expected RE for each decision k.
In order to reduce packet drop in sensor node, node weight is calculated based on the number of packets in the node with hop count of node from the sink.
The following equation is used to calculate the weight of each sensor node
where.
- Wi:
-
is the weight of node i,
- NPN (i):
-
is the number of packets that the node i will forward
- H (i, S):
-
is the hop distance of node i from the closest to the sink.
This fuzzy Inference system has 27 rules which are provided based on the three factors these three factors are used to select the Cluster Head. Fuzzy has three input and two output are provided, then the fuzzy rule gets three input and provide the two output they are probability and radius. Figures 3, 4 and 5 demonstrates the types of Membership functions.
4 Cluster head selection
Cluster head selection process has been carried out in many rounds.
4.1 Algorithm for cluster head selection
First sink node broadcast the message.
Based on the flooding each node update their information into sink.
Check if sink node receives the nodes information then
Generate probability chance of tentative CH and competition radius using T2MFLS

Whenever all data has been successfully transmitted, the Cluster Head will perform success function by eliminating unused data and regenerate the data into main packet. This main packet data is transmitted to the sensor node base station with the use of multi-hop transmission. After a limited period, the next rounds start with the selection of new CH.
4.2 Multi-hop routing protocol
The major difference between the types of fuzzy function is membership function of input values. In type 1, fuzzy logic need not permit for any suspicions nodes about membership value. For multi-hop communication, this fuzzy type 1 is useful in terms of membership function to select the best forwarder node among many CHs.
Cluster head uses multi-hop transmission to accomplish the base station using fuzzy logic. Fuzzy logic takes 3 parameters (trust factor, Residual energy, and distance) to choose other finest cluster head as forwarder node to send the packet to the base station.
In Fig. 6 the fuzzifier takes three types of input parameters for every sensor node as energy, distance and trust factor. The interference engine analyzes the input with fuzzy rules and membership functions. Fuzzy rules provide the conditions to choose the probability sensor nodes that befall the most excellent cluster head that acts as intermediate node. Membership functions present the sets of each participation limitation as high, medium and low.
4.2.1 Distance to sink
In order to save lots of energy in CH this is close to sink, should be elected as generating node. The definition of distance is
Where (CH, Sink) demonstrates the fuzzy distance from Cluster Head to sink node, and NCH(i) demonstrates the list of neighbor nodes.
4.2.2 Trust factor (Tf)
Initially, trust factor is 100 for every CH node. A counter value is incremented for every packet drop in the CH node. Initially, the value for each CH node of the counter is 0 and is incremented by 1 with every successive packet dropped.
Trust factor is calculated based on the number of consecutive packet drops by the CH
where.
- N:
-
Number of repeated packet drop by the CH
4.3 Algorithm for multi-hop routing

Figure 7 describes Cluster management using multi hop communication in Wireless Sensor Network. The Cluster management can be done by using the probability of the forwarding node through the neighbor node with the help of sink node. The Cluster head can send the data to the sink node directly if the probability value will reach the threshold value, which will be calculated by using the fuzzy inference rule.
In the above algorithm, the current energy, trust factor and distance from base station are calculated to the selected cluster. If the cluster head has more number of cluster heads between sink and itself, it employs the fuzzy logic to choose the preferred cluster head to reach the data. Figures 8, 9 and 10 show the membership function of three parameters. The cluster head selects an additional cluster head to reach the base station with respect to the fuzzy logic results
.
Figures 8, 9 and 10 blue line represents the low range, green line represents the medium range and red line represents the high range membership functions of three parameters energy, trust factor and distance.
To create the cluster, we use the fuzzy logic control system (FLCS) is used. The FLS consists of three phases. First phase is fuzzifier, second phase is interference engine and the last phase is defuzzifier. Here, fuzzy logic control system is implemented to choose the probability candidates for best CH for forwarding the collected data. Fuzzy logic control system (FLCS) computes the probability using three input parameters as distance, energy and trust factor. The FLCS output contains a set of nodes which is having high probability of their three parameters.
4.4 Algorithm for cluster management

5 Result analysis
To improve the performance of the WSN, the data packets are sent from one cluster head to another cluster head, and finally the data packets are sent to the base station.
5.1 Cluster head selection
This method is used to the select the cluster head, among many sensor nodes available in the wireless sensor network. In this WSN, one cluster will select the CH and then each cluster will select the CH. Figure 11 demonstrates the cluster head selection
.
5.2 Multi hop broadcast
In multi-hop broadcast method, all the cluster heads are connected in a single link by using the fuzzy type 1 inference rule in a chain format. Data packet is sent from the base cluster head to an additional cluster head and then finally to the base station (Figure 12)
.
5.3 Identify the shortest path node
This method is used to discover the shortest path commencing CH to base station, using the shortest path with enough signal strength. After that, the data packet can be sent to the sink. Figure 13 demonstrates the shortest path finding process
.
5.4 Comparison graph for alive sensor nodes vs different rounds
Figure 14 shows the quantity of alive nodes subsequent to the simulation ends. The simulation ends after 200 s. The four protocols are compared. LEACH, EEUC, PEGASIS have fewer number of alive nodes owing to the elevated energy expenditure. But the proposed EET2FL protocol has high amount of alive nodes
.
5.5 Comparison graph for number of neighbours vs different rounds
Figure 15 demonstrates the comparison analysis for number of neighbours versus the different rounds in multi-hop broadcasting with respect to the energy. If the number of rounds has been increased automatically the energy consumed is also increased. The neighbour node can also transmit the data packet from the base station to the sink node by the way of energy consumption
.
5.6 Comparison graph for energy consumption vs different rounds
Figures 16 and 17 shows the performance analysis of utilized energy by the four protocols. Energy utilization by EET2FL is minor compared to LEACH, PEGSIS and EEUC because it discovers cluster head based on fuzzy logic type 2 for uncertainties in the input value that leads to select best node as CH and it takes trust factor as input for selecting best intermediate CH and this leads to reduce packet drop that increases high data delivery. High residual energy CH will be linked to forward data to the sink that leads low energy consumption
.
5.7 Comparison chart for Energy and Rounds
Figure 18 shows the performance analysis for network lifetime by the four protocols. Network lifetime is measured based on the quantity of alive nodes in the network and first node death, half node death and last node death.Network lifetime is maximum for EET2FL which is less compared to LEACH, PEGSIS and EEUC. The node will die soon compared with EET2FL because it discovers cluster head based on fuzzy logic type 2 for uncertainties in the input value leads to select best node as CH and multi-hop communication based on fuzzy logic type 1 used to select best intermediate CH to reach sink.
6 Conclusion
The aim is to provide load balance to the network and prolong lifetime of the network. Each cluster selects the CH using the three factors such as energy, weight and distance to the base station. In this cluster, any node that can act as source and another node can act as destination. Then, from the source, data packets are sent to the base station by using the CH. Using fuzzy logic type 1 algorithm, all the nodes are connected to the chain format and then data packet can be sent to the sink. Thus, network lifetime is increased and energy is saved. However, the drawback of this approach is the rules in EET2FL are fixed and defined by experience. To solve this rule fixation problem for selecting cluster head, it is planned to use optimization algorithm to segregate the productions and parameters using neuro fuzzy for further improvement.
References
Akyildiz IF, Su W, Sankarasubramaniam Y et al (2002) A survey on sensor networks. IEEE Commun Mag 40(8):102–114
S. Lindsey and C. S. Raghavendra, “PEGASIS: Power-efficient Gathering in Sensor Information Systems”, Parallel and Distributed Systems, vol. 9, no. 924, (2002)
Liu X (2012) A survey on clustering routing protocols in wireless sensor networks. Sensors 12(8):11113–11153
Ali MS, Dey T, and Biswas R (2008) ALEACH: Advanced LEACH routing protocol for wireless microsensor networks. Int Conf Electr Comput Eng ICECE 909–914
Harold RY, Rajaram M, Golden JE, Balaji S (2016) Dominating set algorithm and trust evaluation scheme for secured cluster formation and data transferring. World Acad Sci Eng Technol Int J Comput Electr Autom Control Inf Eng 10:388–393
Harold Robinson Y, Rajaram M, Golden Julie E, Balaji S (2016) “Tree based data fusion clustering routing algorithm for illimitable network administration in wireless sensor network”, world academy of science, engineering and technology. Int J Comput Electr Autom Control Inf Eng 10(6):1123–1130
Harold Robinson Y, Rajaram M (2016) A memory aided broadcast mechanism with fuzzy classification on a device-to-device mobile ad hoc network. Wirel Pers Commun:1–23. https://doi.org/10.1007/s11277-016-3213-0
Arbab E, Aghazarian V, Hedayati A, Ghazanfari Motlagh N (2012) A LEACH-based clustering algorithm for optimizing energy consumption in wireless sensor networks” 2nd international Conference on computer science and information technology (ICCSIT'2012) Singapore
Manjeshwar DP, Agrawal E (2001) TEEN: A routing protocol for enhanced efficiency in wireless sensor networks, In Proceedings of the 15th International Parallel and Distributed Processing Symposium (IPDPS). San Francisco,CA, USA, pp 2009–2015
Karnik, N. N., & Mendel, J. M. (1998). An introduction to type-2 fuzzy logic systems. In proceeding of IEEE international Conference on fuzzy systems (FUZZ) (Vol. 2, pp. 915–920)
Harold RY, Golden JE, Balaji S (2016) Bandwidth and delay aware routing protocol with scheduling algorithm for multi hop mobile ad hoc networks. World Acad Sci Eng Technol Int J Comput Electr Autom Control Inf Eng 10(8):1512–1521
Kumar SS, Kumar MN, Sheeba VS (2011) Fuzzy logic based energy efficient hierarchical clustering in wireless sensor networks. Int J Res Rev Wirel Sens Netw (IJRRWSN) 1(4):53–57
Liang QL, Mendel JM (2000) Equalization of nonlinear time-varying channels using type-2fuzzy adaptive filters. IEEE Trans Fuzzy Syst 8(5):551–563
Kulkarni RV, Forster A, Venayagamoorthy GK (2011) Computational intelligence in wireless sensor networks: a survey. IEEE Commun Surv Tutorials 13(1):68–96
Balaji S, Rajaram M (2016) SIPTAN: securing inimitable and plundering track for ad hoc network. Springer, Wireless Personal Communications, pp 1–21. https://doi.org/10.1007/s11277-016-3187-y
Baranidharan B, Srividhya S, Santhi B (2014) Energy efficient hierarchical unequal clustering in wireless sensor networks. Indian J Sci Technol 7(3):301–305
Heizelman W, Chandrakasan A, Balakrishnan H (2000) Energy-efficient communication protocol for wireless microsensor networks. In Proceeding of the 33rd annual Hawaii international Conference on system sciences (HICSS) (pp. 3005–3014). Maui, HI
Ye M, Li C, Chen G, Wu J (2005) EECS: an energy efficient cluster scheme in wireless sensor networks. Proceedings of IEEE international workshop on strategies for energy efficiency in ad hoc and sensor networks. Phoenix, Arizona
Balaji S, Rajaram M (2014) “EUDIS-An Encryption Scheme for User-Data Security in Public Networks”, World Academy of Science, Engineering and Technology. Int J Comput Inf Syst Control Eng 8(11):1825–1830
Shen B, Zhang SY, Zhong YP (2006) Wireless sensor network clustering routing protocol. J Softw 17(7):1588–1600
Shurman MM, Alomari ZA, and Mhaidat KM (2014) An Efficient Billing Scheme for Trusted Nodes Using Fuzzy Logic in Wireless Sensor Netw Wireless Eng Technol 5:62-73
Castillo O, Melin P (2008) Type-2 fuzzy logic: theory and applications. Springer, Berlin, Heidelberg
Singh AK, Goutele S, Verma S, Purohit N (2012) An energy efficient approach for clustering in WSN using fuzzy logic. Int J Comput Appl 44(18):8–12
O. Younis and S. Fahmy, “HEED: A Hybrid, Energy-efficient”, Distributed Clustering Approach for Ad Hoc Sensor Networks. Mobile Compu, vol. 3, no. 366, (2004)
ArunSamPaul Thomas G, Karthik Ganesh R, Kandasamy A, Balaji S, Harold Robinson Y (2011) An advanced controlled-flooding routing with Group Organization for Delay Tolerant Networks using A-SMART. Emerging trends in electrical and computer technology (ICETECT), 978-1-4244-7926-9/11, IEEE
Harold Robinson Y, Rajaram M, Golden Julie E, Balaji S (2016) “TBOR: tree based opportunistic routing for mobile ad hoc networks”, World Academy of Science, Engineering and Technology. Int J Comput Electr Autom Control Inf Eng 10(6):1115–1122
Robinson YH, Balaji S, Rajaram M (2016) ECBK: enhanced cluster based key management scheme for achieving quality of service. Circuits Syst 7:2014–2024. https://doi.org/10.4236/cs.2016.78175
Balaji S, Harold Robinson Y, Rajaram M (2016) SCSBE: secured cluster and sleep based energy-efficient sensory data collection with mobile sinks. Circuits Syst 7:1992–2001. https://doi.org/10.4236/cs.2016.78173
Harold Robinson Y, Golden Julie E, Balaji S, Ayyasamy A (2016) Energy aware clustering scheme in wireless sensor network using neuro-fuzzy approach, wireless personal communications. Spring:1–19. https://doi.org/10.1007/s11277-016-3793-8
Mendel JM (2001) Uncertain rule-based fuzzy logic system: introduction and new directions. Prentice Hall PTR, UpperSaddle River
Balaji S, Julie EG, Rajaram M, Robinson YH (2016) Fuzzy based particle swarm optimization routing technique for load balancing in wireless sensor networks, World Academy of Science, Engineering and Technology. Int J Comput Electr Autom Control Inf Eng 10(7):1384–1393
Indranil G, Denis R, Srinivas SS (2005) Cluster-head election using fuzzy logic for wireless sensor networks. In Proceedings of the 3rd annual communication networks and services research Conference (CNSR) (pp. 255–260)
Jiang H, Sun Y, Sun R, Hindawi HX Fuzzy-Logic-Based Energy Optimized Routing for Wireless Sensor Networks. Pub Corp Int J Distrib Sens Netw 2013(216561):8. https://doi.org/10.1155/2013/216561
Karnik NN, Mendel JM, Liang QL (1999) Type-2 fuzzy logic systems. IEEE Trans Fuzzy Syst 7(6):643–658
Kim JM, Park SH, Han YJ, Chung TM (2008) CHEF: cluster-head election mechanism using fuzzy logic in wireless sensor networks. In proceedings of the international Conference on advanced communication technology (ICACT) (pp. 654–659)
Yang K (2014) Wireless sensor networks." Principles, design and applications (2014).Zhang, Degan, et al. "An energy-balanced routing method based on forward-aware factor for wireless sensor networks. IEEE Trans Ind Inf 10(1):766–773
Wang, H, Wang J (2014) An effective image representation method using kernel classification." Tools with Artificial Intelligence (ICTAI), 2014 I.E. 26th international Conference on. IEEE (pp. 853-858)
Tuia D, Camps-Valls G, Matasci G, Kanevski M (2010) Learning relevant image features with multiple-kernel classification. IEEE Trans Geosci Remote Sens 48(10):3780–3791
Wang H, Wang J (2014) An effective image representation method using kernel classification. In tools with artificial intelligence (ICTAI), 2014 I.E. 26th international Conference on (pp. 853-858). IEEE
Qi C, Zhou Z, Sun Y, Song H, Hu L, Wang Q (2017) Feature selection and multiple kernel boosting framework based on pso with mutation mechanism for hyperspectral classification. Neurocomputing 220:181–190
Pardo A, Real E, Krishnaswamy V, López-Higuera JM, Pogue BW, Conde OM (2017) Directional kernel density estimation for classification of breast tissue spectra. IEEE Trans Med Imaging 36(1):64–73
Zhao F, Guibas L (2004) Wireless sensor networks:an information processing approach. Publishers –San Francisco, Morgan Kaufmann
Fan.C.-S. (2013) Rich: region-based intelligent cluster-head selection and node deployment strategy in concentric-based WSNs. Adv Electr Ana Maria Popescu Comput Eng 13(4):3–8. https://doi.org/10.4316/AECE.2013.04001
Chattwejee M, Das SK, Turgut D (2002) WCA: a weighted clustering algorithm for mobile ad hoc networks. Clust Comput 5:193–204
Lee C, Jeong T FRCA: A Fuzzy Relevance-Based Cluster Head Selection Algorithm for Wireless Mobile Ad-Hoc Sensor Networks. Division of Electronic Engineering, Chonbuk National University, Jeonbuk, Korea
Aslam M, Rasheed MB, Shah T, Rahim A, Khan ZA, Qasim U, Qasim MW, Hassan A, Khan A, Javaid N Energy optimization and Performance Analysis of Cluster Based Routing Protocols Extended from LEACH for WSNs
Klir G–J, Yuan B (1995) Fuzzy Sets and Fuzzy Logic: Theory and Applications. Prentice Hall, New Jersey
Mahmoud MM, Lin X, Shen X et al (2015) Secure and reliable routing protocols for heterogeneous multihop wireless networks. IEEE Trans Parallel Distrib Syst 26(4):1140–1153
Ayyasamy A, Venkatachalapathy K (2012) Increased throughput for load based channel aware routing in MANETs with reusable paths. Int J Comput Appl 40(2):20–23
Ayyasamy A, Venkatachalapathy K (2015) Context aware adaptive fuzzy based QoS routing scheme for streaming services over MANETs. Wirel Netw 21(2):421–430
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Balaji, S., Golden Julie, E. & Harold Robinson, Y. Development of Fuzzy based Energy Efficient Cluster Routing Protocol to Increase the Lifetime of Wireless Sensor Networks. Mobile Netw Appl 24, 394–406 (2019). https://doi.org/10.1007/s11036-017-0913-y
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11036-017-0913-y