Abstract
Big data has been discussed extensively in existing scholarly works but scant consideration is given to customers’ willingness to generate and leave big data digital footprints on social media, especially in the light of the profusely debated issue of privacy and security. The current paper endeavours to address this gap in the literature by developing a conceptual framework. In doing so, this paper conducts a systematic review of extant literature from 2002 to 2017 to identify and analyse the underlying factors that influence customers’ willingness to leave digital footprints on social media. The findings of this review reveal that personal behaviour (intrinsic psychological dispositions), technological factors (relative advantage and convenience), social influence (social interaction, social ties and social support) and privacy and security (risk, control and trust) are the key factors that influence customers’ willingness to generate and leave big data digital footprints on social media. The conceptual framework presented in this paper advances the scholarship of technology adoption and use and provides useful direction for future empirical research for both academics and practitioners.
Similar content being viewed by others
Explore related subjects
Discover the latest articles, news and stories from top researchers in related subjects.Avoid common mistakes on your manuscript.
1 Introduction
Big data digital footprints are digital DNA that customers generate and leave on digital platforms when they interact with and use various media channels, including social media. The ever-increasing use of and interaction with social media has intensified researchers’ and practitioners’ interest in customers’ social media led digital footprints (Rauniar et al. 2013; Tuton and Solomon 2015). However, research on customers’ perceptions of and attitude towards generating big social data digital footprints is still in its infancy.
Digital footprints are described as social data created by customers when they interact with media channels. Such digital footprints are not just identities but also memories, moments and behaviour. Social media providers who collect these huge digital chronicles can determine how and why users behave and purchase on digital platforms (Fish 2009). Social media use has grown exponentially and has become an integral part of consumer life. With the advent of Web 2.0, digital footprint generation has increased significantly. It is estimated that 44 times more data generation would take place, from 2009 to 44 zettabytes of data by 2020 (CSC 2017). In addition, the exponential growth of mobile telephony (Sharma 2017), cloud computing and 4G networks have created many more social media touchpoints. As a result, customers are found to be connected to smart devices (smartphones, tablets, smartwatches, Cortana, Siri and Alexa etc.) 24/7, generating and leaving behind huge digital trails for service providers. Furthermore, user-generated content on social media will be the main channel for the enrichment of information base for public administrative bodies and commercial firms (Baur 2017).
Tuton and Solomon (2015) divided the use of social media into four zones based on different social media channels and vehicles: i.e. social community interaction, social commerce, social publishing and social entertainment. Customers create their digital DNA on channels in each of these zones by sharing comments, photos, videos, blogs, bookmarks, reviews, ratings and social shopping, linking with government applications etc. (Malhotra et al. 2012; Rosenberger et al. 2017). These digital trails exhibit their interests, social and cultural identities, and occupational and geographical attachments, which are essentially required by firms (Charlesworth 2014; Michael et al. 2014). Moreover, these digital traces help firms to analyse customers’ sentiments and contents by using advanced analytics to gain deeper insight into their behaviour and develop their profiles (Charlesworth 2014; DWork and Mulligan 2013).
Customers use social media excessively, but they may or may not be aware of the digital footprints that they leave for companies such as Google, Yahoo, Amazon and Facebook. The services of social media platforms (Facebook, Twitter and Instagram etc.) have redefined the ways in which business value can be generated, as these providers and tech giants use personal data to track customers and their behaviour through invasive and ubiquitous crawling. They use algorithms to generate powerful insight through data connections, inferences and data interpretations (DWork and Mulligan 2013). Furthermore, as the competition amongst firms is increasing to seek innovative capabilities to mine digital trails and gain a competitive edge over rivals. Hence, the managerial implications for big data digital footprints are immense, as they can create value and promote development (Pulse 2012).
On the other hand, the pervasive use of digital footprints has raised privacy and security concerns amongst social media users. This area is of huge interest for individuals, public and governments as to where to draw the line for privacy and security of unauthorised access to individual digital footprints. This has even led many countries to initiate measures to protect individual privacy and security as social media platforms and web technologies have become more pervasive and vulnerable to abuse and exploitation. Recently in the USA, privacy advocates allege that large Internet service providers can potentially encroach to consumers’ privacy as they have access to large volume of personal data (Waters and Bond 2017). Even everyday objects, connected to the Internet, are collecting personal digital footprints (Kuchler 2017).
Although consumers’ engagement with social media has received significant research attention (Al-Jabri et al. 2015; Charlesworth 2014; Hajli 2014; Hsu and Wu 2011; Akar and Topçu 2011; Hau and Kim 2011), there is paucity of research that identifies and analyses the factors that influence customers’ intention to generate and leave big data digital footprints on social media. Hence, further investigation will not only contribute to big data and social media literature, but also advance privacy and security scholarship. Our study addresses this research gap by identifying and analysing the factors that determine customers’ willingness to generate and leave digital DNAs on social media and how privacy and security deter or facilitate digital footprint generation on social media.
Moreover, the current literature provides the theoretical framework on customers use and adoption of social media (Hsu and Wu 2011; Lin and Anol 2008; Lu et al. 2010; Venkatesh et al. 2012), for instance, Technology Acceptance Model (TAM), Theory of Reasoned Action (TRA), Theory of Planned Behaviour (TPB), Uses and Gratifications (U&G) and the Unified Theory of Acceptance and Use of Technology (UTAUT1 and UTAUT2) etc. are widely cited theories and frameworks for assessing customers’ use of social media. These theories take into account factors that influence users’ acceptance and use of social media such as usefulness, relative advantage, ease of use, innovation, social and compatibility issues (Al-Gahtani et al. 2007; Davis 1989; Davis et al. 1989; Hsu and Wu 2011; Lin and Anol 2008; Lu et al. 2010; Venkatesh et al. 2003; Venkatesh et al. 2012). However they do not fully capture the dynamics and kinetics of customers’ willingness to generate and leave big data digital footprints on social media and provide limited scope for generalisation. Furthermore, they do not address how privacy and security affect customers’ willingness to generate digital footprint on social media. The current paper aims to develop appropriate conceptual scaffoldings for customers’ willingness to generate and leave big data digital footprints on social media by critically examining and synthesising the above mentioned theories and concepts that have been extensively cited and applied in information systems, management and marketing literature.
Therefore, we feel there is a need for a conceptual paper to develop a theoretical framework through a rigorous and systematic review of existing academic literature (Cropanzano 2009). A conceptual paper will offer theoretical impetus for future scholarly works and a theoretical framework for empirical investigation. Hence, the current paper aims to present a conceptual framework that defines the nascent and potential inter-relationships amongst various constructs.
The paper is structured as follows: The first section describes the methodology of the study. The next section delineates the findings and analysis. The final section discusses the results and their theoretical and practical implications, along with limitations and future research direction.
2 Methodology of the systematic review
In order to study customers’ willingness to generate and leave digital footprints on social media, a desk-based study was carried out based on the approach of Ngai et al. (2009) and Ngai and Wat (2002) as follows.
2.1 Classification process
The following steps were carried out in the systematic review.
-
1.
Database search
-
2.
First classification
-
3.
Verification of first classification
-
4.
Final verification
The literature around the use of social media and big data digital footprint was found in a number of different journals belonging to a wide range of disciplinary origins. The following online journal databases were used to identify published peer reviewed articles: EBSCO Host, Emerald, IEEE/IET, Brunel Electronic Library, ProQuest, Sage, Science Direct and Scopus.
The following criteria were used to screen and classify the articles. Only peer reviewed articles were chosen to represent advanced research output as suggested by Ngai et al. (2009). Articles that have main themes around the use of social media, big data digital footprint, customers’ digital footprint, factors influencing the use of social media were chosen. In order to carry out a thorough desk based systematic review, the following appropriate search terms were identified after detailed discussions amongst the authors based on the literature review, following Nill and Schibrowsky (2007). Furthermore, they were searched individually through the search algorithm on the chosen databases. They were rephrased and cross checked to ensure articles fall into the area of the research as the extent literature suggests. “Customers’ digital footprint on social media”, “Why customers leave digital footprint on social media”, “Big data digital footprint of customers on social media”, “Customers’ use of social media”, “Why customers generate digital footprint on social media”. Based on the chosen approach, only peer-reviewed journal articles were selected. The period from January 2002 to May 2017 was selected considering the topicality of the issue.
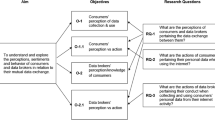
The literature review resulted initially in the identification of 506 articles. The full text of each article was reviewed by the first and second authors, confirmed through discussion and verified by the third author. Feedback from two other independent academics was collected to ensure the validity and reliability of the process. A classification framework, shown in Fig. 1, was developed based on the key emerging factors from the systematic review along with their sub-factors. These four key emerging themes were found to be the leading factors determining customers’ use of social media and their digital footprint generation. As a result, based on these four key factors, 58 articles were selected from the initial sample of 506 articles, although this selection was not exhaustive.
2.1.1 Data reporting
A six-column table (Table 1) was designed to report data captured from the final 58 articles. It was used to examine the constructs used by the previous studies to determine customers’ use and willingness to generate and leave big data digital footprints on social media. The following table delineates the details of constructs identified in each study, along with the choice of theories, research approach, design and findings respectively.
3 Findings and analysis
The systematic review of scholarly works led to the development of the above classification framework (Fig. 1) and identification of the key factors. These factors were found to be the leading determinants of the use of social media and customers’ digital footprint generation. Further analyses of each of the factor along with some sub-factors are provided below.
3.1 Personal behaviour
Personal behaviour consists of personal intrinsic and extrinsic motivation (sub-factors of personal behaviour are listed in Fig. 2). It has been found that the use of social media is mostly influenced by intrinsic motivation such as intrinsic perceived functional and emotional benefits; self-enhancement, self-esteem and ego (Diffley et al. 2011; Hau and Kim 2011). Users are driven by their perceived intrinsic experiential benefits, sensory pleasure (hedonic and emotional: Park and Kim 2014) and self-enhancement, which satisfy their hedonic needs and extrinsic benefits. Similar findings are noted by Whiting and Williams (2013), who report that users tend to engage with social media to fulfil their intrinsic psychological needs of entertainment, relaxation and expression of opinions. The extant literature suggests that psychological intrinsic emotional factors of enjoyment, pleasure, and self-enhancement affect social media user behaviour (Al-Jabri et al. 2015; Campbell et al. 2014; Chen et al. 2014; Grace et al. 2015; Kim et al. 2011; Pereira et al. 2014).
Enjoyment comprises pleasure and flow (optimal psychological experience) and pleasure in the form of playfulness, fun and an intrinsic acceptance of social media (Hsu and Wu 2011; Kim et al. 2011; Wu and Chang 2005; Zolkepli and Kamarulzaman 2015). Self-enhancement consists of self-esteem (self-status and image), which enables users to gratify their outcome expectations of personal influences on social media. High self-enhancers have high self-esteem, due to which they overwhelmingly update and present their self-image/status on social media and attract attention (Chen et al. 2014; Hennig-Thurau et al. 2004; Hepper et al. 2011; Hsu et al. 2007; Presi et al. 2014).
As such, it is found that users’ engagement with social media is based primarily on personal intrinsic motivational factors that affect their behaviour in the use of social media.
3.2 Technology
Technological factors are found to comprise performance expectancy (usefulness, utility), ease of use and relative advantage of the use of social media. Technological sub-factors are given in Fig. 3. Performance expectancy is found to comprise perceived usefulness and utility of technology, which influences users’ behavioural intentions. Similarly, ease of use includes convenience of the use of technology and relative advantage involves the innovative compatibility of social media over other technologies (Al-Gahtani et al. 2007; Lin and Anol 2008; Venkatesh et al. 2003) and the prevailing adoption of technology (Carter and Weerakkody 2008). It can be summarised that perceived usefulness, ease of use, relative advantage and innovation significantly influence social media users’ behavioural intentions (Chiang 2013; Hajli 2014; Milewicz and Saxby 2013; Pillai and Mukherjee 2011; Zhang et al. 2014). Hence, technological factors which constitute social media usefulness, ease of use and compatibility, influence the intention to use of social media (Idemudia et al. 2016; Gironda and Korgaonkar 2014; Lu et al. 2010; Wang et al. 2012; Zolkepli and Kamarulzaman 2015).
3.3 Social factors
Social factors include social interaction, social ties and social support (Bharati et al. 2014; Chiasson and Lovato 2001; Grace et al. 2015; Talukder and Quazi 2011; Venkatesh et al. 2003). These factors drive social interaction, which is a desire to connect, collaborate and communicate with others on social media (Chang and Chuang 2011; De Valck et al. 2009; Hussain 2012; Trivedi et al. 2016). Social Sub-factors are given in Fig. 4.
Social interaction can be described as the desire to communicate, interact with others and build relationships on social media (Al-Jabri et al. 2015; Ko et al. 2005). Similarly, social media are perceived to enhance social interaction, connect people almost anywhere, give control over interaction and maintain social relations with others (family, friends etc.). It is a platform to release anxiety and depression, and to increase companionship and interpersonal utility, as suggested by the extant literature (Ellison et al. 2007; Grieve et al. 2013; Oldmeadow et al. 2013; Park et al. 2009; Whiting and Williams 2013). Moreover, it is found that customers’ pleasurable experience and peer pressure enhance social interaction on social media (Grace et al. 2015; Junglas et al. 2013).
Social ties denote building and maintaining relationships with other social media users (Rishika et al. 2013; Wang et al. 2012). They are psychological goals of users to develop and maintain social relations with others, release anxiety and enhance interpersonal utility (Ellison et al. 2007; Grieve et al. 2013; Whiting and Williams 2013), as it is human nature to socialise and interact with others (Dyson 1998).
Similarly, social support includes willingness to help others and share anything that would assist others on social media (Liang et al. 2011; Zhang et al. 2014). It is a social aspect of exchange to share information with others (Ali 2011; Crocker and Canevello 2008) and also a major social value for social media users from other community members that use and interact with social media (Obst and Stafurik 2010). As such, it can be summarised from the above findings that social factors (social interaction, social ties and social support) enhance the use of social media (Dalla Pozza 2014; Foster et al. 2011; Gironda and Korgaonkar 2014; Hsiao et al. 2010; Hsu and Wu 2011).
3.4 Privacy and security
Privacy and Security are found to comprise perceived risk, control and trust. Privacy involves users’ willingness to share information online and the ability to control and choose to divulge personal information, whereas security relates to protection against the threat from the unauthorised access to personal information on social media (Belanger et al. 2002; Eastlick et al. 2006). Moreover, privacy also includes individuals’ location, communication and information privacy (accumulation, treating and sharing information: Dinev et al. 2013). Sub-factors of privacy and security are given in Fig. 5.
Privacy is described as users’ perceived sense of risk regarding information about oneself and security is perceived as protection against the threat from unauthorised access to information about someone (Boyd 2008; Lee et al. 2013). By joining and interacting with social media, users create their profiles, connect and share interests and personal information with others, which may potentially lead to personal privacy and security risks (Cheung et al. 2015; Tan et al. 2012).
Likewise, in existing literature trust has also emerged as one of the leading factors for privacy and security, and comprises users’ confidence in the ability of a service provider to protect and monitor their personal information or reduce their uncertainty about the use of the service, as they also pay considerable heed to providers’ (vendor and social media) integrity and benevolence (Cao et al. 2015; Cheung et al. 2015; Cheung and Lee 2006; Krasnova et al. 2010). Trust is also noted to have a key relevance to social media users’ perceived risk and it is developed through quality and source credibility (Burgess et al. 2011; Chen and Sharma 2013; Gamboa and Gonçalves 2014; Pentina et al. 2013; Shin 2010; Zhou et al. 2016). From the above discussion, it is found that privacy and security can affect the use of social media and digital footprint generation.
4 Theoretical foundation
A diverse theoretical constructs have been used and applied in the existing literature to conceptualise the above issue. TAM, TRA, TPB and U and G theories have been most frequently used in examining customers’ use and adoption of social media applications. More information has been provided in the Table-1.
5 Research approaches
Positivist methods involving quantitative approaches and statistical testing appear to be more popular and common compared to interpretivist approach and/or qualitative methods. Quantitative research being a dominant method in this scholarship has used closed ended surveys. For model testing and data analysis, Structural Equation Modelling using AMOS and LISREL is a popular tool. For qualitative research, focus groups and semi-structured interviews were found to be the most widely used methods. Table 2 shows that 43 of the 58 studies chose quantitative approaches, whereas 10 studies used qualitative approaches and only 5 studies chose mixed methods respectively.
Table 3 shows the distribution of journals, the number of articles from each journal and the percentage breakdown.
6 Conceptual framework
The current paper presents a conceptual framework (Fig. 6) based on the relevant constructs for the antecedents of customers’ willingness to generate and leave big data digital footprints on social media. The model is based on the Unified Theory of Acceptance and Use of Technology (UTAUT 2). UTAUT 2 is used because it takes into account various aspects of consumers’ use of technology, such as motivation, innovation, technology utilisation and social aspects, as highlighted by the findings of this research. UTAUT 2 integrates elements on the use of technology from UTAUT 1 with similar themes (Venkatesh et al. 2012; Dwivedi et al. 2017). Hence, the proposed conceptual framework is developed by expanding on the UTAUT 2 model to examine the underlying factors that lead customers to generate and leave big data digital footprints on social media. The proposed framework has three antecedents of customers’ behavioural intention (technological factors, social influence and personal behaviour), with privacy and security as moderator. From the findings delineated above, privacy and security are hypothesised to have moderating influence (facilitate or deter) on the relationship between customers’ behavioural intention and its antecedents. Figure 6 presents the proposed framework and the following section explicates each component of the research model.
6.1 Antecedent of customers’ behavioural intention
UTAUT 2 adopted from UTAUT 1 which unified the constructs for technology adoption in order to develop a more holistic understanding. The model suggests performance expectancy by combining similar themes such perceived usefulness, utility and relative advantage. Likewise, perceived ease of use and complexity are brought within effort expectancy; social norms, social factors and social image are combined for social influence; perceived behavioural control and compatibility are termed as facilitating conditions. UTAUT2 extends the model by integrating enjoyment within hedonic motivation, cost within price value and habit as determinants of customers’ behavioural intention (Venkatesh et al. 2012). Some of the earlier works, such as Dwivedi et al. (2008) also ascertained some of these factors in their study of technology adoption, acceptance and diffusion indicating the validity of the model. The current paper has taken a similar stance and identified the following three antecedents of customers’ behavioural intention in terms of their willingness to generate and leave digital footprints on social media. Details of each factor are given below. These factors, as delineated above, affect customers’ digital footprint generation.
Technological factors
The systematic review of literature reveals that the technological factors in the form of usefulness, ease of use (convenience) and relative advantage can influence customers’ interaction with social media and subsequent generation of digital footprints. Moreover, relative advantage comprises perceived technological innovation, which embodies convenience and compatibility, affecting customers’ intention to use social media. Likewise, perceived usefulness was found to enhance job performance and to be instrumental in achieving valued outcomes, as suggested by the extant literature, such as Chen et al. (2009), Chiang (2013), Ho and Wu (2011), Lee et al. (2011) and Lin (2011). Hence, this study makes contribution by explicating the key technological factors of convenience and relative advantage that have a major influence on customers’ big data digital footprint generation.
Social influence
This study has found that social influence is based on customers’ perceived psychological social pressure, comprising social interaction, social ties and social support. This study contributes by unearthing the key social factors of social interaction, social ties and social support that hypothesised and tested to have influence on customers’ psychological needs (Liang et al. 2011; Zhang et al. 2014), which result in big social data digital footprint generation on social media.
Personal behaviour
This study reveals two key personal behaviour factors of self-enhancement (self-efficacy and self-esteem) and perceived experiential and sensory pleasure benefits (hedonic and emotional; joy and enjoyment) that satisfy customers’ hedonic needs (Hau and Kim 2011; Park and Kim 2014). Hence the paper makes a key contribution to the current scholarship by highlighting the key personal behavioural factors that determine customers’ behavioural intention in generating big data digital footprints on social media.
Privacy and security
This study reveals that privacy and security comprise of perceived risks, control and trust. It has found that customers’ self-perceived sense of risks in leaving personal information on social media and their sense of trust in social media providers (privacy) have a huge impact on their use of social media and their digital footprint generation. Equally, their perceived control and trust in service providers’ ability and giving unauthorised access to others (security) affects their digital footprint generation on social media. This study, therefore, makes a contribution by revealing that customers’ sense of privacy is enhanced when their perceived sense of risk increase and their perceived information control and perceived trust in social media decrease, which accordingly facilitates or deters digital footprint generation on social media.
7 Theoretical contributions
First of all, this research advances the literature on the factors that lead to customers’ willingness to generate and leave big data digital footprints on social media. In doing so, it has extracted and analysed the key antecedents influencing customers’ behavioural intentions in the form of technological factors, social influence and personal behaviour. It has also developed a model which exhibits the apposite and significant association among factors, providing valuable insights in determining customers’ underlying behaviour in depositing big data digital footprints on social media, which can have practical implications for managers and practitioners. Furthermore, this study provides significant implications for the role of privacy and security for service providers (social media and vendors). Hence, the paper offers strong conceptual underpinning for assessing the dynamic and dichotomous nature of users’ social media engagement. While, the model is suggested for social media based interaction, the privacy and security issue can also be applied for other technological applications such as cloud computing and smartphones.
8 Conclusion
This desk-based study has applied a systematic literature review of 506peer-reviewed articles. The articles were scattered across 38 different journals, which substantiates that the area of research is of interest in many disciplines. However, marketing, international business and information systems are more in the limelight. This study has found that personal behaviour, technology, social influence and privacy and security are the key factors that influence customers’ willingness to generate and leave big data digital footprints on social media. It has also developed a conceptual framework that offers deeper insights into the dynamics and kinetics of customers’ social media use and their willingness to deposit digital DNA on these media. In addition, this study highlights the theories used profusely in previous scholarly works and articulates the research gap. Addressing the research gap not only advances and enriches the widely used technology adoption theories but can also facilitate future empirical works. A more holistic and robust understanding of consumers’ ambivalence regarding the use of social media and their willingness (or a lack of it) of leaving digital footprints would enlighten future researchers and pave the way to more scholarly works in this field.
Moreover, the paper provides useful insights to the practitioners who can use the model to ascertain their target customers’ motivation for and perceptions of using social media and other related interfaces. Businesses should realise that customers do not want to be chased; rather they would like to be wooed. Not all customers would have same motivation and/or similar level of desire to engage with social media. Hence, the social media providers such as Facebook and Instagram and the businesses who promote their products and services through these platforms and collect customer information should be aware of the sensitivities and intricacies pertaining to customers’ privacy and security.
8.1 Limitations and future research directions
There are some notable limitations of this study. Firstly, it has focused mainly on peer-reviewed academic articles; future research could include monographs and industry reports. Secondly, the articles were clustered around the chosen four dimensions; future research could combine and choose the articles which have common factors. Thirdly, this study includes some articles around online social commerce; future research could focus just on social media customers. Last but not the very least, the conceptual framework offers a more generic model for assessing customers’ willingness to leave digital footprints. Future research could include cultural factors to posit the model in specific socio-cultural contexts.
References
Akar, E., & Topçu, B. (2011). An examination of the factors influencing consumers’ attitudes toward social media marketing. Journal of Internet Commerce, 10(1), 35–67.
Al-Gahtani, S. S., Hubona, G. S., & Wang, J. (2007). Information technology (IT) in Saudi Arabia: culture and the acceptance and use of IT. Information Management, 44(8), 681–691.
Ali, H. (2011). Exchanging value within individuals’ networks: social support implications for health marketers. Journal of Marketing Management, 27(3/4), 316–335.
Al-Jabri, I. M., Sohail, M. S., & Ndubisi, N. O. (2015). Understanding the usage of global social networking sites by Arabs through the lens of uses and gratifications theory. Journal of Service Management, 26(4), 662–680.
Baur, A. W. (2017). Harnessing the social web to enhance insights into people’s opinions in business, government and public administration. Information Systems Frontiers, 19(2), 231–251.
Belanger, F., Hiller, J. S., & Smith, W. J. (2002). Trustworthiness in electronic commerce: the role of privacy, security, and site attributes. The Journal of Strategic Information Systems, 11(3), 245–270.
Bharati, P., Zhang, C., & Chaudhury, A. (2014). Social media assimilation in firms: Investigating the roles of absorptive capacity and institutional pressures. Information Systems Frontiers, 16(2), 257–272.
Boyd, D. (2008). Facebook’s Privacy Trainwreck: Exposure, Invasion, and Social Convergence. Convergence. The International Journal of Research into new Media Technologies, 14(1), 13–20.
Burgess, S., Sellitto, C., Cox, C., & Buultjens, J. (2011). Trust perceptions of online travel information by different content creators: Some social and legal implications. Information Systems Frontiers, 13(2), 221–235.
Campbell, C., Ferraro, C., & Sands, S. (2014). Segmenting consumer reactions to social network marketing. European Journal of Marketing, 48(3/4), 432–452.
Cao, X., Guo, X., Liu, H., & Gu, J. (2015). The role of social media in supporting knowledge integration: A social capital analysis. Information Systems Frontiers, 17(2), 351–362.
Carter, L., & Weerakkody, V. (2008). E-government adoption: A cultural comparison. Information Systems Frontiers, 10(4), 473–482.
Chang, H. H., & Chuang, S. S. (2011). Social capital and individual motivations on knowledge sharing: Participant involvement as a moderator. Information Management, 48(1), 9–18.
Charlesworth, A. (2014). An Introduction to social media marketing. Oxon: Routledge.
Chen, R., & Sharma, S. K. (2013). Self-disclosure at social networking sites: An exploration through relational capitals. Information Systems Frontiers, 15(2), 269–278.
Chen, J. V., Yen, D. C., & Chen, K. (2009). The acceptance and diffusion of the innovative smartphone use: a case study of a delivery service company in logistics. Information Management, 46(4), 241–248.
Chen, A., Lu, Y., Chau, P. Y., & Gupta, S. (2014). Classifying, Measuring, and Predicting Users’ Overall Active Behavior on Social Networking Sites. Journal of Management Information Systems, 31(3), 213–253.
Cheung, C. M., & Lee, M. K. (2006). Understanding consumer trust in Internet shopping: A multidisciplinary approach. Journal of the American Society for Information Science and Technology, 57(4), 479–492.
Cheung, C., Lee, Z. W., & Chan, T. K. (2015). Self-disclosure in social networking sites: the role of perceived cost, perceived benefits and social influence. Internet Research, 25(2), 279–299.
Chiang, H. S. (2013). Continuous usage of social networking sites: The effect of innovation and gratification attributes. Online Information Review, 37(6), 851–871.
Chiasson, M. W., & Lovato, C. Y. (2001). Factors influencing the formation of a user’s perception and use of a DSS software innovation. Database for Advances in Information Systems, 32(3), 16–35.
Chow, W. S., & Shi, S. (2015). Investigating customers’ satisfaction with brand pages in social networking sites. The Journal of Computer Information Systems, 55(2), 48.
Crocker, J., & Canevello, A. (2008). Creating and undermining social support in communal relationships: The role of compassionate and self-image goals. Journal of Personality and Social Psychology, 95(3), 555–575.
Cropanzano, R. (2009). “Writing nonempirical articles for Journal of Management: general thoughts and suggestions.” Journal of Management, 35(6), 1304–13011.
CSC (2017). Big data Universe beginning to explode. [Web log comment].Retrieved from http://www.csc.com/insights/flxwd/78931big_data_universe_beginning_to_explode.
Dalla Pozza, I. (2014). Multichannel management gets “social”. European Journal of Marketing, 48(7/8), 1274–1295.
Davis, F. D. (1989). Perceived Usefulness, Perceived Ease of Use, and User Acceptance of Information Technology. M IS Quarterly, 13(3), 319–339.
Davis, F. D., Bagozzi, R. P., & Warshaw, P. R. (1989). “User acceptance of computer technology: a comparison of two theoretical models.” Management science, 35(8), 982–1003.
De Valck, K., van Bruggen, G. H., & Wierenga, B. (2009). Virtual communities: a marketing perspective. Decision Support Systems, 47(3), 185–203.
Dennis, C., Merrilees, B., Jayawardhena, C., & Tiu Wright, L. (2009). E-consumer behaviour. European Journal of Marketing, 43(9/10), 1121–1139.
Diffley, S., Kearns, J., Bennett, W., & Kawalek, P. (2011). Consumer behaviour in social networking sites: implications for marketers. Irish Journal of Management, pp., 47–66 Available at: http://iamireland.ie/wp-content/uploads/2012/05/IJM_30_2_Final_crop.pdf#page=57.
Dinev, T., Xu, H., Smith, J. H., & Hart, P. (2013). Information privacy and correlates: an empirical attempt to bridge and distinguish privacy-related concepts. European Journal of Information Systems, 22(3), 295–316.
Domina, T., Lee, S.-E., & MacGillivray, M. (2012). Understanding factors affecting consumer intention to shop in a virtual world. Journal of Retailing and Consumer Services, 19(6), 613–620 Available at: http://linkinghub.elsevier.com/retrieve/pii/S0969698912000975.
Dwivedi, Y. K., Williams, M. D., & Venkatesh, V. (2008). Guest Editorial: A profile of adoption of Information and Communication Technologies (ICT) research in the household context. Information Systems Frontiers, 10(4), 385–390.
Dwivedi, Y. K., Rana, N. P., Jeyaraj, A., Clement, M., & Williams, M. D. (2017). “Re-examining the Unified Theory of Acceptance and Use of Technology (UTAUT): Towards a Revised Theoretical Model.” Information Systems Frontiers. https://doi.org/10.1007/s10796-017-9774-y.
DWork, C., & Mulligan, D. K. (2013). It's Not Privacy, and It's Not Fair. [Online] Available at: http://www.stanfordlawreview.org/online/privacy-and-big-data/its-not-privacy-and-itsnot-fair. Accessed 28 June 2014.
Dyson, E. (1998). A design for living in the digital age. New York: Broadway Books.
Eastlick, M. A., Lotz, S. L., & Warrington, P. (2006). Understanding online B-to-C relationships: an integrated model of privacy concerns, trust, and commitment. Journal of Business Research, 59(8), 877–886.
Ellison, N. B., Steinfield, C., & Lampe, C. (2007). The benefits of Facebook “friends:” Social capital and college students’ use of online social network sites. Journal of Computer-Mediated Communication, 12(4), 1143–1168.
Fish, T. (2009). My Digital Footprint A two-sided digital business model where your privacy will be someone else's business. 1st ed. Kindle ebook: futuretext.
Foster, M., West, B., & Francescucci, A. (2011). Exploring social media user segmentation and online brand profiles. Journal of Brand Management, 19(1), 4–17.
Gamboa, A. M., & Gonçalves, H. M. (2014). Customer loyalty through social networks: lessons from Zara on Facebook. Business Horizons, 57(6), 709–717.
Ghosh, A., Varshney, S., & Venugopal, P. (2014). Social Media WOM: Definition, Consequences and Inter-relationships. Management and Labour Studies, 39(3), 293–308.
Gironda, J. T., & Korgaonkar, P. K. (2014). Understanding consumers’ social networking site usage. Journal of Marketing Management, 30(5–6), 571–605.
Grace, D., Ross, M., & Shao, W. (2015). Examining the relationship between social media characteristics and psychological dispositions. European Journal of Marketing, 49(9/10), 1366–1390.
Grieve, R., Indian, M., Witteveen, K., Anne Tolan, G., & Marrington, J. (2013). Face-to-face or Facebook: can social connectedness be derived online? Computers in Human Behaviour, 29(3), 604–609.
Hajli, M. N. (2014). A study of the impact of social media on consumers. International Journal of Market Research, 56(3), 388–404.
Hau, Y. S., & Kim, Y. G. (2011). Why would online gamers share their innovation-conducive knowledge in the online game user community? Integrating individual motivations and social capital perspectives. Computers in Human Behavior, 27(2), 956–970.
Hennig-Thurau, T., Gwinner, K. P., Walsh, G., & Gremler, D. D. (2004). Electronic word-of-mouth via consumer-opinion platforms: what motivates consumers to articulate themselves on the Internet? Journal of Interactive Marketing, 18(1), 38–52.
Hepper, E. G., Hart, C. M., Gregg, A. P., & Sedikides, C. (2011). Motivated expectations of positive feedback in social interactions. Journal of Social Psychology, 151(4), 455–477.
Ho, C., & Wu, W. (2011). The role of innovativeness of consumer in relationship between perceived attributes of new products and intention to adopt. International Journal of Electronic Business Management, 9(3), 258–266.
Hsiao, K. L., Lin, J. C. C., Wang, X. Y., Lu, H. P., & Yu, H. (2010). Antecedents and consequences of trust in online product recommendations. Online Information Review, 34(6), 935–953.
Hsu, C., & Wu, C. (2011). Understanding users’ continuance of Facebook: an integrated model with the unified theory of acceptance and use of technology, expectation disconfirmation model, and flow theory. International Journal of Virtual Communities and Social Networking, 3(2), 1–16.
Hsu, C., Ju, T. L., Yen, C. H., & Chang, C. M. (2007). Knowledge sharing behavior in virtual communities: The relationship between trust, self-efficacy, and outcome expectations. International Journal of Human-Computer Studies, 65(2), 153–169 Available at: http://linkinghub.elsevier.com/retrieve/pii/S1071581906001431.
Hudson, S., & Hudson, R. (2013). Engaging with consumers using social media: a case study of music festivals. International Journal of Event and Festival Management, 4(3), 206–223 Available at: http://www.emeraldinsight.com/journals.htm?issn=1758-2954andvolume=4andissue=3andarticleid=17096678andshow=html.
Hussain, I. (2012). A study to evaluate the social media trends among university students. Procedia – Social and Behavioral Sciences, 64, 639–645.
Idemudia, E. C., Raisinghani, M. S., & Samuel-Ojo, O. (2016). ”The contributing factors of continuance usage of social media: An empirical analysis.” Information Systems Frontiers. https://doi.org/10.1007/s10796-016-9721-3.
Jansen, B. J., Zhang, M., Sobel, K., & Chowdury, A. (2009). Twitter power: Tweets as electronic word of mouth. Journal of the American Society for Information Science and Technology, 60(11), 2169–2188.
Jiang, Z., Heng, C. S., & Choi, B. C. (2013). Research Note—Privacy Concerns and Privacy-Protective Behavior in Synchronous Online Social Interactions. Information Systems Research, 24(3), 579–595.
Junglas, I., Goel, L., Abraham, C., & Ives, B. (2013). The social component of information systems – how sociability contributes to technology acceptance. Journal of the Association for Information Systems, 14(10), 585–616.
Kennedy, H., Elgesem, D., & Miguel, C. (2017). “On fairness: User perspectives on social media data mining.” Convergence, 23(3), 270–288.
Kim, H. W., Gupta, S., & Koh, J. (2011). Investigating the intention to purchase digital items in social networking communities: A customer value perspective. Information Management, 48(6), 228–234.
Ko, H., Cho, C. H., & Roberts, M. S. (2005). Internet uses and gratifications: a structural equation model of interactive advertising. Journal of Advertising, 34(2), 57–70.
Krasnova, H., Spiekermann, S., Koroleva, K., & Hildebrand, T. (2010). Online social networks: why we disclose. Journal of Information Technology, 25(2), 109–125.
Krasonikolakis, I., Vrechopoulos, A., & Pouloudi, A. (2014). Store selection criteria and sales prediction in virtual worlds. Information Management, 51(6), 641–652.
Kuchler, H. (2017). The Internet of things: Home is where the hackers are. Financial Times. Retrieved from https://www.ft.com/content/cb880bc2-057c-11e7-ace0-1ce02ef0def9.
Lambiotte, R., & Kosinski, M. (2014). Tracking the Digital Footprints of Personality. Proceedings of the IEEE, 102(12), 1934–1939.
Lee, D., Park, J. Y., Kim, J., & Moon, J. (2011). Understanding music sharing behaviour on social network services. Online Information Review, 35(5), 716–733.
Lee, H., Park, H., & Kim, J. (2013). Why do people share their context information on Social Network Services? A qualitative study and an experimental study on users' behavior of balancing perceived benefit and risk. International Journal of Human-Computer Studies, 71(9), 862–877.
Leung, X. Y., Bai, B., & Stahura, K. A. (2015). The Marketing Effectiveness of Social Media in the Hotel Industry A Comparison of Facebook and Twitter. Journal of Hospitality and Tourism Research, 39(2), 147–169.
Liang, T.-P., Ho, Y.-T., Li, Y.-W., & ScTurban, E. (2011). What drives social commerce: the role of social support and relationship quality. International Journal of Electronic Commerce, 16(2), 69–90.
Lin, H. F. (2011). An empirical investigation of mobile banking adoption: the effect of innovation attributes and knowledge-based trust. International Journal of Information Management, 31(3), 252–260.
Lin, C. P., & Anol, B. (2008). Learning online social support: an investigation of network information technology based on UTAUT. Cyberpsychology and Behavior, 11(3), 268–272.
Lu, Y., Zhao, L., & ScWang, B. (2010). From virtual community members to c2c e-commerce buyers: trust in virtual communities and its effect on consumers’ purchase intention. Electronic Commerce Research and Applications, 9(4), 346–360.
Malhotra, A., Totti, L., Meira Jr, W., Kumaraguru, P., & Almeida, V. (2012). Studying user footprints in different online social networks. In Proceedings of the 2012 International Conference on Advances in Social Networks Analysis and Mining (ASONAM 2012) (pp. 1065–1070). IEEE Computer Society.
Mathwick, C. (2002). Understanding the online consumer: a typology of online relational norms and behavior. Journal of Interactive Marketing, 16(1), 40–55.
Michael, M. G., Michael, K., & Perakslis, C. (2014). “Uberveillance and the Internet of Things and people. In Contemporary Computing and Informatics (IC3I),” 2014 International Conference on (pp. 1381–1386). IEEE.
Milewicz, & Saxby. (2013). Leaders’ social media usage intentions for in-bound customer communications. Management Research Review, 36(9), 849–867.
Ngai, E. W. T., & Wat, F. K. T. (2002). A literature review and classification of electronic commerce research. Information Management, 39(5), 415–429.
Ngai, E. W. T., Xiu, L., & Chau, D. C. K. (2009). Application of data mining techniques in customer relationship management: a literature review and classification. Expert Systems with Applications: An International Journal, 36(2), 2592–2602.
Ngai, E. W. T., Moon, K. K., Lam, S. S., Chin, E. S. K., & Tao, S. S. C. (2015). Social media models, technologies, and applications An academic review and case study. Industrial Management and Data Systems, 115(5), 769–802.
Nill, A., & Schibrowsky, J. A. (2007). Research on marketing ethics: A systematic review of the literature. Journal of Macromarketing, 27(3), 256–273.
Nissenbaum, H., (2004). “Privacy as contextual integrity.” Washington Law Review Association, 79(1), 119–158.
Obst, P., & Stafurik, J. (2010). Online we are all able bodied: Online psychological sense of community and social support found through membership of disability-specific Websites promotes well-being for people living with a physical disability. Journal of Community and Applied Social Psychology, 20(6), 525–531.
Oldmeadow, J. A., Quinn, S., & Kowert, R. (2013). Attachment style, social skills, and Facebook use amongst adults. Computers in Human Behaviour, 29(3), 1142–1149.
Park, H., & Kim, Y.-K. (2014). The role of social network websites in the consumer–brand relationship. Journal of Retailing and Consumer Services, 21(4), 460–467.
Park, N., Kee, K., & Valenzuela, S. (2009). Being immersed in social networking environment: Facebook groups, uses and gratifications, and social outcomes. CyberPsychology and Behavior, 12(6), 729–733.
Pentina, I., Zhang, L., & Basmanova, O. (2013). Antecedents and consequences of trust in a social media brand: a cross-cultural study of Twitter. Computers in Human Behavior, 29(4), 1546–1555.
Pereira, H.G., de Fátima Salgueiro, M. and Mateus, I. (2014). “Say yes to Facebook and get your customers involved! Relationships in a world of social networks.” Business Horizons, 57(6), pp.695–702. Available at: http://www.sciencedirect.com/science/article/pii/S0007681314000937.
Pillai, A., & Mukherjee, J. (2011). User acceptance of hedonic versus utilitarian social networking web sites. Journal of Indian Business Research, 3(3), 180–191.
Presi, C., Saridakis, C., & Hartmans, S. (2014). User-generated content behaviour of the dissatisfied service customer. European Journal of Marketing, 48(9/10), 1600–1625.
Pulse, G., (2012). Big Data for Development: Opportunities and Challenges: A Global Pulse White Paper. [Online]. Available at: http://www.unglobalpulse.org/BigDataforDevWhitePaper [Accessed 1 May 2017].
Rauniar, R., Rawski, G., Yang, J., & Johnson, B. (2013). Technology acceptance model (TAM) and social media usage: an empirical study on Facebook. Journal of Enterprise Information Management, 27(1), 6–30.
Rishika, R., Kumar, A., Janakiraman, R., & Bezawada, R. (2013). The effect of customers' social media participation on customer visit frequency and profitability: an empirical investigation. Information Systems Research, 24(1), 108–127.
Rosenberger, M., Lehrer, C., & Jung, R. (2017). Integrating data from user activities of social networks into public administrations. Information Systems Frontiers, 19(2), 253–266.
Schroeder, R.(2014). “Big Data and the brave new world of social media research”, Big Data and Society, 1(2), 2053951714563194.
Sharma, S. K. (2017). Integrating cognitive antecedents into TAM to explain mobile banking behavioral intention: A SEM-neural network modeling. Information Systems Frontiers, 1–13. https://doi.org/10.1007/s10796-017-9775-x.
Shin, D. H. (2010). The effects of trust, security and privacy in social networking: A security-based approach to understand the pattern of adoption. Interacting with Computers, 22(5), 428–438.
Talukder, M., & Quazi, A. (2011). The impact of social influence on individuals’ adoption of innovation. Journal of Organizational Computing and Electronic Commerce, 21(2), 111–135.
Tan, X., Qin, L., Kim, Y., & Hsu, J. (2012). Impact of privacy concern in social networking web sites. Internet Research, 22(2), 211–233.
Trivedi, N., Asamoah, D. A., and Doran, D. (2016). Keep the conversations going: engagement-based customer segmentation on online social service platforms. Information Systems Frontiers, 1–19. Available at: https://doi.org/10.1007/s10796-016-9719-x.
Tucker, C. E. (2014). Social networks, personalized advertising, and privacy controls. Journal of Marketing Research, 51(5), 546–562.
Tuton, T. L. and Solomon, M. R. (2015) Social Media Marketing, 2nd Edition, London: Sage Publication Ltd.
Venkatesh, V., Morris, M. G., Davis, G. B., & Davis, F. D. (2003). User acceptance of information technology: toward a unified view. Management Information Systems Quarterly, 27(3), 425–478.
Venkatesh, V., Thong, J. Y., and Xu, X. (2012). Consumer acceptance and use of information technology: extending the unified theory of acceptance and use of technology.
Wang, X., Yu, C., & Wei, Y. (2012). Social media peer communication and impacts on purchase intentions: a consumer socialization framework. Journal of Interactive Marketing, 26(4), 198–208.
Waters, R. and Bond, S. (2017). US moves step closer to overturning broadband privacy regulations. Financial Times. Retrieved from https://www.ft.com/content/fbb144fa-1411-11e7-80f4-13e067d5072c.
Whiting, A., & Williams, D. (2013). Why people use social media: a uses and gratifications approach. Qualitative Market Research: An International Journal, 16(4), 362–369.
Wu, J. J., & Chang, Y. S. (2005). Towards understanding members’ interactivity, trust, and flow in online travel community. Industrial Management and Data Systems, 105(7), 937–954.
Wu, J.-J., Chen, Y.-H., & Chung, Y.-S. (2010). Trust factors influencing virtual community members: a study of transaction communities. Journal of Business Research, 63(9–10), 1025–1032.
Yulihasri, Islam, M. A., & Daud, K. A. K. (2011). Factors that influence customers’ buying intention on shopping online. International Journal of marketing studies, 3(1), 128.
Zhang, H., Lu, Y., Gupta, S., & Zhao, L. (2014). What motivates customers to participate in social commerce? The impact of technological environments and virtual customer experiences. Information Management, 51(8), 1017–1030.
Zhou, T., Lu, Y., & Wang, B. (2016). Examining online consumers’ initial trust building from an elaboration likelihood model perspective. Information Systems Frontiers, 18(2), 265–275.
Zolkepli, I. A., & Kamarulzaman, Y. (2015). Social media adoption: The role of media needs and innovation characteristics. Computers in Human Behavior, 43, 189–209.
Author information
Authors and Affiliations
Corresponding author
Additional information
Unified Theory of Acceptance and Use of Technology model (UTAUT2), which takes into account various aspects of customers’ use of technology to offer deep insights into the dynamics and kinetics of customers’ willingness to deposit digital DNA on social media
Rights and permissions
About this article
Cite this article
Muhammad, S.S., Dey, B.L. & Weerakkody, V. Analysis of Factors that Influence Customers’ Willingness to Leave Big Data Digital Footprints on Social Media: A Systematic Review of Literature. Inf Syst Front 20, 559–576 (2018). https://doi.org/10.1007/s10796-017-9802-y
Published:
Issue Date:
DOI: https://doi.org/10.1007/s10796-017-9802-y