Abstract
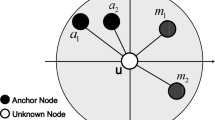
Rapid technological advances have enabled the development of low-cost sensor networks for various monitoring tasks, where it is important to estimate the positions of a number of regular sensor nodes whose locations cannot be known apriori. We address the problem of localizing the regular nodes with range-based location references obtained from certain anchor nodes referred to as beacons, particularly in an adverse environment where some of the beacons may be compromised. We propose an innovative modular solution featuring two lightweight modules that are for dedicated functionalities, respectively, but can also be closely integrated. First, we harness simple geometric triangular rules and an efficient voting technique to enable the attack detection module, which identifies and filters out malicious location references. We then develop a secure localization module that computes and clusters certain reference points, and the position of the concerned regular node is estimated with the centroid of the most valuable reference points identified. Extensive simulations show that our attack detection module can detect compromised beacons effectively, and the secure localization module can subsequently provide a dependable localization service in terms of bounded estimation error. The integrated system turns out to be tolerant of malicious attacks even in highly challenging scenarios.
Article PDF
Similar content being viewed by others
Avoid common mistakes on your manuscript.
References
Akyildiz I.F., Su W., Sankarasubramaniam Y., Cayirci E.: A survey on sensor networks. IEEE Commun. Mag. 40, 102–114 (2002)
Perrig A., Szewczyk R., Tygar J.D., Wen V., Culler D.E.: SPINS: Security protocols for sensor networks. Wirel. Netw. 8, 521–534 (2002)
Boukerche A., Oliveira H.A.B.F., Nakamura E.F., Loureiro A.A.F.: Localization systems for wireless sensor networks. IEEE Wirel. Commun. 14, 6–12 (2007)
Savvides, A., Han, C.-C., Strivastava, M.B.: Dynamic fine-grained localization in ad-hoc networks of sensors. In: Proceedings of the 7th International Conference on Mobile Computing and Networking (MobiCom’01), pp. 166–179 (2001)
Misra, S., Xue, G.: CluRoL: Clustering based robust localization in wireless sensor networks. In: Proceedings of the IEEE Military Communications Conference 2007 (MILCOM’07), pp. 1–7 (2007)
Karlof C., Wagner D.: Secure routing in wireless sensor networks: attacks and countermeasures. Ad hoc Netw. 1, 293–315 (2003)
Nagpal, R., Shrobe, H., Bachrach, J.: Organizing a global coordinate system from local information on an ad hoc sensor network. In: Proceedings of the 2nd International Workshop on Information Processing in Sensor Network (IPSN’03) Lecture Notes in Computer Science, vol. 2634, pp. 333–348 (2003)
Niculescu, D., Nath, B.: Ad hoc positioning system (APS) using AoA. In: Proceedings of the 22nd Joint Conference of the IEEE Computer and Communications Societies (INFOCOM’03), vol. 3, pp. 1734–1743 (2003)
Thaeler A., Ding M., Cheng X.: iTPS: an improved location discovery scheme for sensor networks with long-range beaconsc. J. Parallel Distrib. Comput. 65, 98–106 (2005)
Du W., Fang L., Ning P.: LAD: Localization anomaly detection for wireless sensor networks. J. Parallel Distrib. Comput. 66, 874–886 (2006)
Liu D., Ning P., Liu A., Wang C., Du W.K.: Attack-resistant location estimation in sensor networks. ACM Trans Inf Syst Secur 11, 22:1–22:39 (2008)
Boukerche A., Oliveira H.A.B.F., Nakamura E.F., Loureiro A.A.F.: Secure localization algorithms for wireless sensor networks. IEEE Commun. Mag. 46, 96–101 (2008)
Lazos L., Poovendran R.: HiRLoc: high-resolution robust localization for wireless sensor networks. IEEE J. Sel. Areas Commun. 24, 233–246 (2006)
Lazos L., Poovendran R.: SeRLoc: robust localization for wireless sensor networks. ACM Trans. Sens. Netw. 1, 73–100 (2005)
Čapkun, S., Hubaux, J.-P.: Secure positioning of wireless devices with application to sensor networks. In: Proceedings of the 24nd Joint Conference of the IEEE Computer and Communications Societies (INFOCOM’05), vol. 3, pp. 1917–1928 (2005)
Lazos, L., Poovendran, R., Čapkun, S.: ROPE: Robust position estimation in wireless sensor networks. In: Proceedings of the 4nd International Symposium on Information Processing in Sensor Networks (IPSN’05), pp. 324–331 (2005)
Liu, D., Ning, P., Du, W.: Detecting malicious beacons for secure localization discovery in wireless sensor networks. In: Proceedings of the 25th IEEE International Conference on Distributed Computing Systems (ICDCS’05), pp. 609–619 (2005)
Zhou Y., Fang Y., Zhang Y.: Securing wireless sensor networks: a survey. IEEE Commun. Surv. Tutor. 10, 6–28 (2008)
Liu, D., Ning, P.: Location-based pairwise key establishments for static sensor networks. In: Proceedings of the 1st ACM Workshop on Security in Ad Hoc and Sensor Networks (SASN’03), pp. 72–82 (2003)
Du, W., Deng, J., Han, Y.S., Chen, S., Varshney, P.K.: A key management scheme for wireless sensor networks using deployment knowledge. In: Proceedings of the 23rd Joint Conference of the IEEE Computer and Communications Societies (INFOCOM’04), pp. 586–597 (2004)
Liu D., Ning P.: Improving key predistribution with deployment knowledge in static sensor networks. ACM Trans. Sens. Netw. 1, 204–239 (2005)
Younis M.F., Ghumman K., Eltoweissy M.: Location-aware combinatorial key management scheme for clustered sensor networks. IEEE Trans. Parallel Distrib. Syst. 17, 865–882 (2006)
Misra, S., Bhardwaj, S., Xue, G.: ROSETTA: Robust and secure mobile target tracking in a wireless ad hoc environment. In: Proceedings of the IEEE Military Communication Conference 2006 (MILCOM’06), pp. 1–7 (2006)
Li, Z., Trappe, W., Zhang, Y., Nath, B.: Robust statistical methods for securing wireless localization in sensor networks. In: Proceedings of the 4nd International Symposium on Information Processing in Sensor Networks (IPSN’05), pp. 91–98 (2005)
Zhong, S., Jadliwala, M., Upadhyaya, S., Qiao, C.: Towards a theory of robust localization against malicious beacon nodes. In: Proceedings of the 27th IEEE Conference on Computer Communications (INFOCOM’08), pp. 1391–1399 (2008)
He D., Cui L., Huang H., Ma M.: Design and verification of enhanced secure localization scheme in wireless sensor networks. IEEE Trans. Parallel Distrib. Syst. 20, 1050–1058 (2009)
Zhang Y., Liu W., Fang Y., Wu D.: Secure localization and authentication in ultra-wideband sensor networks. IEEE J. Sel. Areas Commun. 24, 829–835 (2006)
Zhu, W.T., Xiang, Y.: Argus: A light-weighted secure localization scheme for sensor networks. In: Proceedings of the 6th International Conference on Autonomic and Trusted Computing (ATC’09), Lecture Notes in Computer Science, vol. 5586, pp. 164–178 (2009)
Chan, H., Perrig, A., Song, D.: Random key predistribution schemes for sensor networks. In: Proceedings of the 24th IEEE Symposium on Security and Privacy (SSP’03), pp. 197–213 (2003)
Du, W., Deng, J., Han, Y.S., Varshney, P.K.: A pairwise key pre-distribution scheme for wireless sensor networks. In: Proceedings of the 10th ACM Conference on Computer and Communications Security (CCS’03), pp. 42–51 (2003)
Yang, W., Zhu, W.T.: Voting-on-grid clustering for secure localization in wireless sensor networks. In: Proceedings of the IEEE International Conference on Communications (ICC) 2010, (2010)
Author information
Authors and Affiliations
Corresponding author
Additional information
This work was supported by the Singapore A*STAR project SEDS-0721330047 and by the National Natural Science Foundation of China under Grant 60970138.
Rights and permissions
About this article
Cite this article
Zhu, W.T., Xiang, Y., Zhou, J. et al. Secure localization with attack detection in wireless sensor networks. Int. J. Inf. Secur. 10, 155–171 (2011). https://doi.org/10.1007/s10207-011-0127-4
Published:
Issue Date:
DOI: https://doi.org/10.1007/s10207-011-0127-4