Abstract
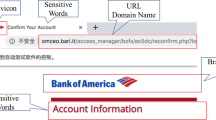
Phishing website is an illegitimate website that is designed by dishonest people to mimic a real website. Those who are entering such a website may expose their sensitive information to the attacker who might use this information for financial and criminal activities. In this technological world, phishing websites are created using new techniques allows them to escape from most anti-phishing tool. So, the white list and blacklist based techniques are less effective when compared with the recent phishing trends. Advanced to that, there exist some tools using machine learning and deep learning approaches by examining webpage content in order to detect phishing websites. Along with the rapid growth of phishing technologies, it is needed to improve the effectiveness and efficiency of phishing website detection. This work reviewed many papers that proposed different real-time as well as non-real-time techniques. As the result, this study suggests a Convolutional Neural Network (CNN) framework with 18 layers and scope of transfer learning in Alex Net for the classification of websites using screenshot images and URLs of phishing and legitimate websites. CNN is a class of deep, feed-forward artificial neural networks (where connections between nodes do not form a cycle) & use a variation of multilayer perceptions designed to require minimal preprocessing.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Issac, B., Chiong, R., & Jacob, S. M. (2014). Analysis of Phishing Attacks and Countermeasures. IBIMA, Bonn, Germany, ISBN 0-9753393-5-4, 339–346.
Ali, W. (2017). Phishing Website Detection based on Supervised Machine Learning with Wrapper Features Selection. International Journal of Advanced Computer Science and Applications, 8(9), 72–78.
APWG report [Online] Available at: https://docs.apwg.org/reports/apwg_trends_report_q4_2018.pdf.
https://www.mathworks.com/content/dam/mathworks/tagteam/Objects/d/80879v00_Deep_Learningebook. pdf.
Adebowale, M. A., Lwin, K. T., Sanchez, E., & Hossain, M. A. (2019). Intelligent web-phishing detection and protection scheme using integrated features of Images, frames and text. Expert Systems with Applications, 115, 300–313.
Deshmukh, M., Popat, S. K., & Student, U. (2017). Different Techniques for Detection of Phishing Attack. International Journal of Engineering Science, 10201.
Atighetchi, M., & Pal, P. (2009). Attribute-based prevention of phishing attacks. In 2009 Eighth IEEE International Symposium on Network Computing and Applications.
Shreeram, V., Suban, M., Shanthi, P., & Manjula, K. (2010). Anti-phishing detection of phishing attacks using genetic algorithm. In 2010 International Conference on Communication Control and Computing Technologies (pp. 447–450), Ramanathapuram.
Almomani, A., Gupta, B. B., Atawneh, S., Meulenberg, A., & Almomani, E. (2013). A survey of phishing email filtering techniques. IEEE communications surveys & tutorials, 15(4), 2070-2090.
Tout, H., & Hafner, W. (2009). Phishpin: An identity-based anti-phishing approach. In 2009 international conference on computational science and engineering (Vol. 3, pp. 347–352).
Zhang, Y., Hong, J. I., & Cranor, L. F. (2007). Cantina: a content-based approach to detecting phishing web sites. In Proceedings of the 16th international conference on World Wide Web (pp. 639–648), ACM.
Dunlop, M., Groat, S., & Shelly, D. (2010). Goldphish: Using images for content-based phishing analysis. In 2010 Fifth international conference on internet monitoring and protection (pp. 123–128).
Deshmukh, M., Popat, S. K., & Student, U. (2017). Link Guard Algorithm Approach on Phishing Detection and Control. International Journal of Advance Foundation and Research in Computer (IJAFRC).
Jiang, J., Lin, X., Ghorbani, A., Ren, K., Zhu, S., Zhang, A. (2017). A deep learning based online malicious URL and DNS detection scheme. In International Conference on Security and Privacy in Communication Systems (pp. 438–448). Springer, Cham.
Mohammad, R., McCluskey, T. L., & Thabtah, F. A. (2013). Predicting phishing websites using neural network trained with back-propagation. In: Proceedings of the 2013 World Congress in Computer Science, Computer Engineering, and Applied Computing. WORLDCOMP 2013 . World Congress in Computer Science, Computer Engineering, and Applied Computing, Las Vegas, Nevada, USA, (pp. 682–686). ISBN 1601322461.
Ferreira, R., Martiniano, A., Napolitano, D., Romero, M., De Oliveira Gatto, D., Farias, E., et al. (2018). Artificial Neural Network for Websites Classification with Phishing Characteristics. Social Networking, 7, 97–109.
Gupta, S., & Singhal, A. (2017, August). Phishing URL detection by using artificial neural network with PSO. In 2017 2nd International Conference on Telecommunication and Networks (TEL-NET), Noida, (pp. 1–6).
Babuška, R. (2003). Neuro-fuzzy methods for modeling and identification. In Abraham A., Jain L.C., Kacprzyk J (Eds.)Recent advances in intelligent paradigms and applications (pp. 161-186). Physica, Heidelberg.
Barraclough, P. A., Hossain, M. A., Tahir, M. A., Sexton, G., & Aslam, N. (2013). Intelligent phishing detection and protection scheme for online transactions (Report). Expert Systems with Applications, 40(11), 4697.
Aleroud, A., & Zhou, L. (2017). Phishing environments, techniques, and countermeasures: A survey. Computers & Security.
Sönmez, Y., Tuncer, T., Gökal, H., & Avcı, E. (2018). Phishing web sites features classification based on extreme learning machine. In 2018 6th International Symposium on Digital Forensic and Security (ISDFS) (pp. 1–5).
https://www.mathworks.com/content/dam/mathworks/tagteam/Objects/d/80879v03_Deep_Learning_ebook.pdf.
Jiang, J. (2017). A deep learning based online malicious URL and DNS detection scheme. Security and Privacy in Communication Networks: SecureComm 2017. Lecture Notes of the Institute for Computer Sciences, Social Informatics and Telecommunications Engineering, (Vol. 239). Springer, Cham.
Adebowale, M. A., Lwin, K. T., Sanchez, E., & Hossain, M. A. (2019). Intelligent web-phishing detection and protection scheme using integrated features of Images, frames and text. Expert Systems with Applications.
Dhamija, R., & Tygar, J. D. (2005). The battle against phishing: Dynamic security skins. In Proceedings of the 2005 Symposium on Usable privacy and security (pp. 77–88).
Afroz, S., & Greenstadt, R. (2011). Phishzoo: Detecting phishing websites by looking at them. In 2011 IEEE fifth International Conference on Semantic Computing (pp. 368–375).
Chen, K.-T., Chen, J.-Y., Huang, C.-R., & Chen, C.-S. (2009). Fighting phishing with discriminative keypoint features. IEEE Internet Computing, 13(3), 56–63.
Fu, A. Y., Wenyin, L., & Deng, X. (2006). Detecting phishing web pages with visual similarity assessment based on earth mover’s distance (EMD). IEEE transactions on dependable and secure computing, 3(4), 301–311.
Haruta, S., Asahina, H., & Sasase, I. (2017). Visual similarity-based phishing detection scheme using image and CSS with target website finder. In GLOBECOM 2017-2017 IEEE Global Communications Conference (pp. 1–6), Singapore.
Jain, A. K., & Gupta, B. B. (2017). Phishing detection: analysis of visual similarity based approaches. Security and Communication Networks, 2017. 5421046:1-5421046:20.
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2021 Springer Nature Singapore Pte Ltd.
About this paper
Cite this paper
Rajaram, J., Dhasaratham, M. (2021). Scope of Visual-Based Similarity Approach Using Convolutional Neural Network on Phishing Website Detection. In: Satapathy, S., Bhateja, V., Janakiramaiah, B., Chen, YW. (eds) Intelligent System Design. Advances in Intelligent Systems and Computing, vol 1171. Springer, Singapore. https://doi.org/10.1007/978-981-15-5400-1_45
Download citation
DOI: https://doi.org/10.1007/978-981-15-5400-1_45
Published:
Publisher Name: Springer, Singapore
Print ISBN: 978-981-15-5399-8
Online ISBN: 978-981-15-5400-1
eBook Packages: Intelligent Technologies and RoboticsIntelligent Technologies and Robotics (R0)