Abstract
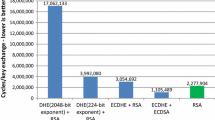
We present a 64-bit optimized implementation of the NIST and SECG-standardized elliptic curve P-224. Our implementation is fully integrated into OpenSSL 1.0.1: full TLS handshakes using a 1024-bit RSA certificate and ephemeral Elliptic Curve Diffie-Hellman key exchange over P-224 now run at twice the speed of standard OpenSSL, while atomic elliptic curve operations are up to 4 times faster. In addition, our implementation is immune to timing attacks—most notably, we show how to do small table look-ups in a cache-timing resistant way, allowing us to use precomputation. To put our results in context, we also discuss the various security-performance trade-offs available to TLS applications.
Access provided by Autonomous University of Puebla. Download to read the full chapter text
Chapter PDF
Similar content being viewed by others
References
Acıiçmez, O., Koç, Ç.K., Seifert, J.-P.: Predicting Secret Keys Via Branch Prediction. In: Abe, M. (ed.) CT-RSA 2007. LNCS, vol. 4377, pp. 225–242. Springer, Heidelberg (2006)
Bernstein, D.J.: A software implementation of NIST P-224 (2001), http://cr.yp.to/nistp224.html
Bernstein, D.J.: Curve25519: New Diffie-Hellman Speed Records. In: Yung, M., Dodis, Y., Kiayias, A., Malkin, T. (eds.) PKC 2006. LNCS, vol. 3958, pp. 207–228. Springer, Heidelberg (2006)
Bernstein, D.J., Chen, H.-C., Chen, M.-S., Cheng, C.-M., Hsiao, C.-H., Lange, T., Lin, Z.-C., Yang, B.-Y.: The billion-mulmod-per-second pc. In: Workshop record of SHARCS 2009: Special-purpose Hardware for Attacking Cryptographic Systems (2009)
Brown, M., Hankerson, D., López, J., Menezes, A.: Software Implementation of the NIST Elliptic Curves over Prime Fields. In: Naccache, D. (ed.) CT-RSA 2001. LNCS, vol. 2020, pp. 250–265. Springer, Heidelberg (2001)
Brumley, B.B., Hakala, R.M.: Cache-Timing Template Attacks. In: Matsui, M. (ed.) ASIACRYPT 2009. LNCS, vol. 5912, pp. 667–684. Springer, Heidelberg (2009)
Internet Engineering Task Force. Elliptic curve cryptography (ECC) cipher suites for transport layer security (TLS) (2006), http://www.ietf.org/rfc/rfc4492
Internet Engineering Task Force. Transport layer security (TLS) session resumption without server-side state (2008), http://www.ietf.org/rfc/rfc5077
Galbraith, S.D., Lin, X., Scott, M.: Endomorphisms for Faster Elliptic Curve Cryptography on a Large Class of Curves. In: Joux, A. (ed.) EUROCRYPT 2009. LNCS, vol. 5479, pp. 518–535. Springer, Heidelberg (2009)
TLS Working Group. Transport layer security (TLS) false start, https://tools.ietf.org/html/draft-bmoeller-tls-falsestart-00
ECRYPT II. eBACS: ECRYPT benchmarking of cryptographic systems, http://bench.cr.yp.to/supercop.html
ECRYPT II. Yearly report on algorithms and keysizes (2010), D.SPA.13 Rev. 1.0, ICT-2007-216676 (2010), http://www.ecrypt.eu.org/documents/D.SPA.13.pdf
Joye, M., Tunstall, M.: Exponent Recoding and Regular Exponentiation Algorithms. In: Preneel, B. (ed.) AFRICACRYPT 2009. LNCS, vol. 5580, pp. 334–349. Springer, Heidelberg (2009)
Kocher, P.C.: Timing Attacks on Implementations of Diffie-Hellman, RSA, DSS, and other Systems. In: Koblitz, N. (ed.) CRYPTO 1996. LNCS, vol. 1109, pp. 104–113. Springer, Heidelberg (1996)
Langley, A.: curve25519-donna: A 64-bit implementation of Curve25519, http://code.google.com/p/curve25519-donna/
Möller, B.: Algorithms for Multi-Exponentiation. In: Vaudenay, S., Youssef, A.M. (eds.) SAC 2001. LNCS, vol. 2259, pp. 165–180. Springer, Heidelberg (2001)
mozilla.org. Network Security Services, http://www.mozilla.org/projects/security/pki/nss/
NIST. Recommendation for key management, special publication 800-57 part 1
The OpenSSL project. OpenSSL—cryptography and SSL/TLS toolkit, http://www.openssl.org
Certicom Research. SEC 2: Recommended elliptic curve domain parameters (2010)
Ivan Ristic. Internet SSL survey. Technical report, Qualys, Black Hat USA (2010)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2012 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Käsper, E. (2012). Fast Elliptic Curve Cryptography in OpenSSL. In: Danezis, G., Dietrich, S., Sako, K. (eds) Financial Cryptography and Data Security. FC 2011. Lecture Notes in Computer Science, vol 7126. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-29889-9_4
Download citation
DOI: https://doi.org/10.1007/978-3-642-29889-9_4
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-29888-2
Online ISBN: 978-3-642-29889-9
eBook Packages: Computer ScienceComputer Science (R0)