Abstract
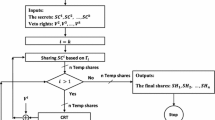
We propose a new construction for computationally secure secret sharing schemes with general access structures where all shares are as short as the secret. Our scheme provides the capability to share multiple secrets and to dynamically add participants on-line, without having to re-distribute new shares secretly to the current participants. These capabilities are gained by storing additional authentic (but not secret) information at a publicly accessible location.
Preview
Unable to display preview. Download preview PDF.
Similar content being viewed by others
References
J. Benaloh, and J. Leichter, Generalized secret sharing and monotone functions, in Advances in Cryptology — CRYPTO '88, S. Goldwasser, ed., vol. 403 of Lecture Notes in Computer Science, Springer-Verlag, 1990, pp. 27–35.
B. Blakley, G. R. Blakley, A. H. Chan, and J. L. Massey, Threshold schemes with disenrollment, in Advances in Cryptology — CRYPTO '92, E. F. Brickell, ed., vol. 740 of Lecture Notes in Computer Science, Springer-Verlag, 1993, pp. 540–548.
C. Blundo, A. Cresti, A. De Santis, and U. Vaccaro, Fully dynamic secret sharing schemes, in Advances in Cryptology — CRYPTO '93, D. R. Stinson, ed., vol. 773 of Lecture Notes in Computer Science, Springer-Verlag, 1994, pp. 110–125.
C. Blundo, A. De Santis, G. Di Crescenzo, A. G. Gaggia, and U. Vaccaro, Multi-secret sharing schemes, in Advances in Cryptology — CRYPTO '94, Y. G. Desmedt, ed., vol. 839 of Lecture Notes in Computer Science, Springer-Verlag, 1994, pp. 150–163.
R. M. Capocelli, A. D. Santis, L. Gargano, and U. Vaccaro, On the size of shares for secret sharing schemes, in Advances in Cryptology — CRYPTO '91, J. Feigenbaum, ed., vol. 576 of Lecture Notes in Computer Science, Springer-Verlag, 1992, pp. 101–113.
L. Csirmaz, The size of a share must be large, in Advances in Cryptology — EUROCRYPT '94, A. De Santis, ed., vol. 950 of Lecture Notes in Computer Science, Springer-Verlag, 1995, pp. 13–22.
D. E. Denning and M. Smid, Key escrowing today, IEEE Communications Magazine, 32 (1994), pp. 58–68.
O. Goldreich, S. Micali, and A. Wigderson, How to play any mental game or a completeness theorem for protocols with honest majority, in Proc. 19th ACM Symposium on Theory of Computing (STOC), 1987, pp. 218–229.
M. Ito, A. Saito, and T. Nishizeki, Secret sharing scheme realizing general access structure, in Proceedings of IEEE Globecom '87, 1987, pp. 99–102.
H. Krawczyk, Secret sharing made short, in Advances in Cryptology — CRYPTO '93, D. R. Stinson, ed., vol. 773 of Lecture Notes in Computer Science, Springer-Verlag, 1994, pp. 136–146.
L. Lamport, Password authentication with insecure communication, Comm. ACM, 24 (1981).
S. Micali, Fair public-key cryptosystems, in Advances in Cryptology — CRYPTO '92, E. F. Brickell, ed., vol. 740 of Lecture Notes in Computer Science, Springer-Verlag, 1993, pp. 113–138.
M. O. Rabin, Efficient dispersal of information for security, load balancing, and fault tolerance, J. Assoc. Comput. Mach., 36 (1989), pp. 335–348.
A. Shamir, How to share a secret, Comm. ACM, 22 (1979), pp. 612–613.
G. J. Simmons, An introduction to shared secret and/or shared control schemes and their application, in Contemporary Cryptology: The Science of Information Integrity, G. J. Simmons, ed., IEEE Press, 1991, pp. 441–497.
D. R. Stinson, An explication of secret sharing schemes, Designs, Codes and Cryptography, 2 (1992), pp. 357–390.
Author information
Authors and Affiliations
Editor information
Rights and permissions
Copyright information
© 1995 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Cachin, C. (1995). On-line secret sharing. In: Boyd, C. (eds) Cryptography and Coding. Cryptography and Coding 1995. Lecture Notes in Computer Science, vol 1025. Springer, Berlin, Heidelberg. https://doi.org/10.1007/3-540-60693-9_22
Download citation
DOI: https://doi.org/10.1007/3-540-60693-9_22
Published:
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-60693-2
Online ISBN: 978-3-540-49280-1
eBook Packages: Springer Book Archive