Abstract
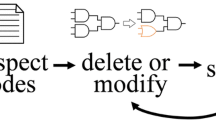
We have developed the first hardware and software (intellectual property) metering scheme that enables reliable low overhead proofs for the number of manufactured parts and copied programs. The key idea is to make each design/ progrsm slightly different during postprocessing phase. Therefore, if two identical hardware/software designs or a design that is not reported by the foundry are detected, the design house has proof of misconduct.
We start by establishing implementation requirements for intellectual property metering. We also establish the connection between the requirements for hardware and software metering and synthesis/compilation process. Furthermore, we present mathematical analysis of statistical accuracy of the proposed hardware and software metering schemes. The effectiveness of the metering scheme is demonstrated on a number of designs and programs.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Preview
Unable to display preview. Download preview PDF.
Similar content being viewed by others
References
R. Anderson, M. Kuhn, “Tamper resistance-a cautionary note.” USENIX Workshop on Electronic Commerce, pp. 1–11, 1996.
T Aura, D. Gollmann, “Software license management with smart cards.” Proceedings of the USENIX Workshop on Smartcard Technology (Smartcard’99), pp. 75–85, May1999.
B.S. Baker, U. Manber, “Deducing similarities in Java sources from bytecodes.” USENIX Technical Conference, pp. 179–90, 1998.
S. Brin, J. Davis, H. Garcia-Molina, “Copy detection mechanisms for digital documents.” SIG-MOD Record, vol. 24, no. 2, pp. 398–409, 1995.
A.E. Caldwell, H. Choi, A.B. Kahng, S. Mantik, M. Potkonjak, G. Qu, J.L. Wong, “Effective iterative techniques for fingerprinting design IP.” Design Automation Conference, pp. 843–848, 1999.
G.J. Chaitin, “Register allocation and spilling via graph coloring.” SIGPLAN’ 82 Symposium on Compiler Construction, pp. 98–105, 1982.
E. Charbon, I. Torunoglu, “Copyright protection of designs based on multi source IPs.” IEEE/ ACM International Conference on Computer Aided Design, pp. 591–595, June 1998.
C.S. Collberg, “Reverse interpretation + mutation analysis = automatic retargeting.” Proceedings of the ACM SIGPLAN 1997 Conference on Programming Language Design and Implementation, pp. 15–18, June 1997
R.E. Crochiere, A.V. Oppenheim, “Analysis of linear digital networks.” Proceedings of the IEEE, vol. 63, no. 4, pp. 581–95., April 1975
S. Dey, V. Gangaram, M. Potkonjak, “A controller redesign technique to enhance testability of controller-data path circuits.” IEEE Transactions on Computer-Aided Design of Integrated Circuits and Systems, vol. 17, no. 2, pp. 157–68, February 1998.
W. Diffie, M. Hellman, “New directions in cryptography.” IEEE Transactions on Information Theory, vol. IT-22, no. 6, pp. 644–54, November 1976.
R. Findley Jr., Raymond, R. Dixon, “Dual smart card access control electronic data storage and retrieval system and methods.” US patent#5629508, May 13, 1997.
P. Flajolet, D. Gardy, L. Thimonier, “Birthday paradox, coupon collectors, caching algorithms and self-organizing search.” Discrete Applied Mathematics, vol. 39, no. 3, pp. 207–229, November 1992.
M.K. Franklin, D. Malkhi, “Auditable metering with lightweight security”. Journal of Computer Security, vol. 6, no. 4, IOS Press, pp. 237–55, 1998.
M.R. Garey, D.S. Johnson, “Computers and intractability. A guide to the theory of NP-com-pleteness.” Oxford, UK: Freeman, 1979.
L.M. Guerra, M. Potkonjak, J.M. Rabaey, “Behavioral-level synthesis of heterogeneous BISR reconfigurable ASIC’s.” IEEE Transactions on Very Large Scale Integration (VLSI) Systems, vol. 6, no. 1, pp. 158–67, March 1998.
F. Hartung, M. Kutter, “Multimedia watermarking techniques.” Proceedings of the IEEE, vol. 87, no. 7, pp. 1079–107, July 1999.
A.B. Kahng, J. Lach, W.H. Mangione-Smith, S. Mantik, I.L. Markov, M. Potkonjak, P. Tucker, H. Wang, G. Wolfe, “Watermarking techniques for intellectual property protection.” 35th ACM/IEEE Design Automation Conference Proceedings, pp. 776–781, June 1998.
A.B. Kahng, D. Kirovski, S. Mantik, M. Potkonjak, J.L. Wong, “Copy detection for intellectual property protection of VLSI design.” IEEE/ACM International Conference on Computer Aided Design, pp. 600–604, November 1999.
D. Kirovski, M. Potkonjak, “Efficient coloring of a large spectrum of graphs.” Proceedings 1998 Design and Automation Conference, pp. 427–32, 1998.
D. Kirovski, D. Liu, J.L. Wong, M. Potkonjak, “Forensic engineering techniques for VLSICAD tools.” 37th ACM/IEEE Design Automation Conference Proceedings, pp. 581–6, June 2000.
K. Lofstrom, W.R. Daasch, D. Taylor, “IC identification circuits using device mismatch.” Proceedings of the International Solid-State Circuits Conference, pp. 372–3, 2000.
D. P. Maher, “Fault induction attacks, tamper resistance, and hostile reverse engineering in perspective.” Financial Cryptography First International Conference, pp. 109–21, 1997.
A. J. Menezes, P.C. van Oorschot, S.A. Vanstone, “Handbook of applied cryptography.” Boca Raton, FL: CRC Press, 1997.
M. Naor, B. Pinkas, “Secure accounting and auditing on the Web.” Computer Networks and ISDN Systems, vol. 30, no. 1–7, Elsevier, pp. 541–50, April 1998.
R.L. Rivest (Edited by: Hirschfeld, R.), “Electronic lottery tickets as micropayments.” Financial Cryptography First International Conference, pp. 307–14, 1997.
C.D. Ross, N.W. Taylor, K.W. Kingdon, H.R. Davis, D. Major “Method and apparatus for electronic licensing.” US patent# 5553143, Sept. 3, 1996
D.C. Thomas, “Method and apparatus for providing security for computer software.” US patent#4446519, May 1984.
J. Pitkow, “In search of reliable usage data on the WWW.” Computer Networks and ISDN Systems, vol. 29, no. 8–13, pp. 1343–55, September 1997.
M. Potkonjak, S. Dey, K. Wakabayashi, “Design-for-Debugging of application specific designs.” International Conference on Computer-Aided Design, pp. 295–301, 1995.
G. Qu, M. Potkonjak, “Analysis of watermarking techniques for graph coloring problem,” IEEE/ACM International Conference on Computer Aided Design, pp. 190–193, November 1998.
J.M. Rabaey, C. Chu, P. Hoang, M. Potkonjak, “Fast prototyping of datapath-intensive architectures.” IEEE Design & Test of Computers, June 1991, vol. 8, no. 2, pp. 40–51, June 1991.
B. Schneier, “Applied cryptography: protocols, algorithms, and source code in C,” 2nd edition New York: Wiley, 1996.
D.R. Stinson, “Cryptography: theory and practice.” Boca Raton, FL: CRC Press, 1995.
L. Stok, J.A.G. Jess, “Foreground memory management in data path synthesis.” International Journal of Circuit Theory and Applications, vol. 20, no. 3, pp. 235–55. May–June 1992
K. Veenstra, Altera Corporation, Personal Communication. January 1999.
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2001 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Koushanfar, F., Qu, G., Potkonjak, M. (2001). Intellectual Property Metering. In: Moskowitz, I.S. (eds) Information Hiding. IH 2001. Lecture Notes in Computer Science, vol 2137. Springer, Berlin, Heidelberg. https://doi.org/10.1007/3-540-45496-9_7
Download citation
DOI: https://doi.org/10.1007/3-540-45496-9_7
Published:
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-42733-9
Online ISBN: 978-3-540-45496-0
eBook Packages: Springer Book Archive