Abstract
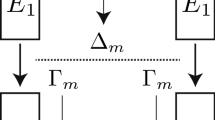
We formally introduce the concept of related-cipher attack. In this paper, we consider the related ciphers as block ciphers with the same round function but with different round numbers. If their key schedules do not depend on the total round number, then related-cipher attack could be applied if the same key is used. We applied this attack to block cipher Square and show that Square is vulnerable to this attack. We also show that a new AES key schedule proposed at ACISP02 is weaker than the original one under this attack. We then classify the differential attacks into three categories: related-message attack (the original differential cryptanalysis), related-key attack and related-cipher attack. These attacks should be taken into consideration in cipher design.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Preview
Unable to display preview. Download preview PDF.
Similar content being viewed by others
References
E. Biham and A. Shamir. Differential Cryptanalysis of the Data Encryption Standard, Springer-Verlag, 1993.
E. Biham. New Types of Cryptanalytic Attacks Using Related Keys. In T. Helleseth, editor, Advances in Cryptology: Proc. of Eurocrypt’ 93, LNCS 765, pages 398–409, Springer-Verlag, 1994.
J. Daemen, L. Knudsen and V. Rijmen. The Block Cipher SQUARE. In E. Biham, editor, Fast Software Encryption-Proc. Forth International Workshop, Haifa, Israel, January 1997, LNCS 1267, pages 13–27, Springer Verlag, 1997.
C. Harpes and J.L. Massey. Partitioning Cryptanalysis. In E. Biham, editor, Fast Software Encryption: Forth International Workshop, Haifa, Israel, January 1997, LNCS 1267, pages 13–27, Springer Verlag, 1997.
L.R. Knudsen. Truncated and higher order differentials. In B. Preneel, editor, Fast Software Encryption: Second International Workshop, Leuven, Belgium, 1994, LNCS 1008, pages 196–211, Springer Verlag, 1995.
L.R. Knudsen and M.J.B. Robshaw. Non-Linear Approximations in Linear Cryptanalysis. In U. Maurer, editor, Advancess in Cryptology-Eurocrypt’96, LNCS 1070, pages 224–235. Springer Verlag, 1995.
X. Lai. Higher order derivatives and differential cryptanalysis. In Proc. “Symposium on Communication, Coding and Cryptography”, in honor of James L. Massey on the occasion of his 60’th birthday, Feb. 10–13, 1994, Monte-Verita, Ascona, Switzerland, 1994.
S.K. Langford and M.E. Hellman. Differential-linear cryptanalysis. In Y. G. Desmedt, editor, Advances in Cryptology-Proc. Crypto’94, LNCS 839, pages 17–26. Springer Verlag, 1994.
B.S. Kaliski Jr. and M.J.B. Robshaw. Linear Cryptanalysis Using Multiple Approximations. In Y. G. Desmedt, editor, Advances in Cryptology-Proc. Crypto’94, LNCS 839, pages 27–39. Springer Verlag, 1994.
J. Massey. SAFER K-64: A Byte-Oriented Block-Ciphering Algorithm. In R. Anderson, editor, Fast Software Encryption-Proc. Cambridge Security Workshop, Cambridge, U.K., Dec. 9–11, 1993, LNCS 809, Springer-Verlag, pp. 1–17. [See also: SAFER K-64: One Year Later. In B. Preneel, editor, Fast Software Encryption — Proceedings of the Second International Workshop on Fast Software Encryption, Springer-Verlag, 1995, pp.212–241; and Strengthened Key Schedule for the Cipher SAFER, posted to the USENET newsgroup sci.crypt, September 9, 1995]
M. Matsui, Linear Cryptanalysis Method for DES Cipher. In T. Helleseth, editor, Advances in Cryptology-Proc. of Eurocrypt’ 93, LNCS 765, pages 386–397, Springer-Verlag, 1994.
L. May, M. Henricksen, W. Millan, G. Carter, and E. Dawson, Strengthening the Key Schedule of the AES. In Information Security and Privacy-Proc. of ACISP 2002, LNCS 2384, pages 226–240.
National Institute of Standards and Technology, Advanced Encryption Standard. Available at http://csrc.nist.gov/encryption/aes/
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2002 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Wu, H. (2002). Related-Cipher Attacks. In: Deng, R., Bao, F., Zhou, J., Qing, S. (eds) Information and Communications Security. ICICS 2002. Lecture Notes in Computer Science, vol 2513. Springer, Berlin, Heidelberg. https://doi.org/10.1007/3-540-36159-6_38
Download citation
DOI: https://doi.org/10.1007/3-540-36159-6_38
Published:
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-00164-5
Online ISBN: 978-3-540-36159-6
eBook Packages: Springer Book Archive