Abstract
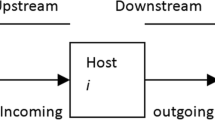
The so-called “Great Firewall of China” operates, in part, by inspecting TCP packets for keywords that are to be blocked. If the keyword is present, TCP reset packets (viz: with the RST flag set) are sent to both endpoints of the connection, which then close. However, because the original packets are passed through the firewall unscathed, if the endpoints completely ignore the firewall’s resets, then the connection will proceed unhindered. Once one connection has been blocked, the firewall makes further easy-to-evade attempts to block further connections from the same machine. This latter behaviour can be leveraged into a denial-of-service attack on third-party machines.
Access provided by Autonomous University of Puebla. Download to read the full chapter text
Chapter PDF
Similar content being viewed by others
Keywords
- Transmission Control Protocol
- Intrusion Detection System
- Port Number
- Child Pornography
- Domain Name System
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
Bellovin, S.: Defending Against Sequence Number Attacks. RFC1948, IETF (May 1996)
Carter, E.: Secure Intrusion Detection Systems. Cisco Press (2001)
Clayton, R.: Failures in a Hybrid Content Blocking System. In: Danezis, G., Martin, D. (eds.) PET 2005. LNCS, vol. 3856, Springer, Heidelberg (2006)
Clayton, R.: Anonymity and Traceability in Cyberspace. Tech Report UCAM-CL-TR-653, Computer Laboratory, University of Cambridge (2005)
Dornseif, M.: Government mandated blocking of foreign Web content. In: von Knop, J., Haverkamp, W., Jessen, E. (eds.) Security, E-Learning, E-Services: Proceedings of the 17. DFN-Arbeitstagung über Kommunikationsnetze, Düsseldorf 2003. Lecture Notes in Informatics, pp. 617–648 (2003)
Edelman, B.: Web Sites Sharing IP Addresses: Prevalence and Significance. Berkman Center for Internet and Society (February 2003), http://cyber.law.harvard.edu/people/edelman/ip-sharing/
King Abdulaziz City for Science and Technology: Local content filtering Procedure. Internet Services Unit, KACST (2004), http://www.isu.net.sa/saudi-internet/contenet-filtring/filtring-mechanism.htm
The OpenNet Initiative: Probing Chinese search engine filtering. Bulletin 005 (August 2004), http://www.opennetinitiative.net/bulletins/005/
The OpenNet Initiative: Internet Filtering in China in 2004–2005: A Country Study (June 2004), http://www.opennetinitiative.net/studies/china/ONI_China_Country_Study.pdf
The OpenNet Initiative: Internet Filtering in Burma in 2005: A Country Study (October 2004), http://www.opennetinitiative.net/burma/ONI_Burma_Country_Study.pdf
Postel, J. (ed.): Transmission Control Protocol: DARPA Internet Program Protocol Specification. RFC 793, IETF (1981)
Norge, T.: Telenor and KRIPOS introduce Internet child pornography filter. Telenor Press Release (September 21, 2004), http://presse.telenor.no/PR/200409/961319_5.html
US District Court for the Eastern District of Pennsylvania: CDT, ACLU, Plantagenet Inc. v Pappert, 337 F.Supp.2d 606 (September 10, 2004)
Villeneuve, N.: Censorship Is In the Router (June 3, 2005), http://ice.citizenlab.org/?p=113
Watson, P.: Slipping in the Window: TCP Reset Attacks. CanSecWest/core04 (2004)
Watson, R.: 20060607-tcp-ttl.diff (June 2006), http://www.cl.cam.ac.uk/~rnw24/patches/
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2006 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Clayton, R., Murdoch, S.J., Watson, R.N.M. (2006). Ignoring the Great Firewall of China. In: Danezis, G., Golle, P. (eds) Privacy Enhancing Technologies. PET 2006. Lecture Notes in Computer Science, vol 4258. Springer, Berlin, Heidelberg. https://doi.org/10.1007/11957454_2
Download citation
DOI: https://doi.org/10.1007/11957454_2
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-68790-0
Online ISBN: 978-3-540-68793-1
eBook Packages: Computer ScienceComputer Science (R0)