
Collection
Advances in Digital Forensics
- Submission status
- Closed
Societies in today’s world are becoming more and more dependent on open networks such as Internet where commercial activities, business transactions and government services are realized. This has led to the fast development of new cyber threats and information security issues which are utilized by cyber criminals. Mistrust for telecommunications and computer network technologies have tremendous socio-economic impacts on global enterprises as well as individuals.
Moreover, the occurrence of international frauds often requires the investigation of facts that occur across international borders. They are also often subject to different jurisdictions and legal systems. The increased complexity of the communication and networking infrastructure is making investigation of the crimes difficult. Clues of illegal digital activities are often buried in large volumes of data that is hard to inspect in order to detect crimes and collect evidence.
Editors
-
Amir Houmansadr
-
-
Wojciech Mazurczyk
Prof. Wojciech Mazurczyk is a WUT Professor at the Institute of Computer Science, Division of Software Engineering and Computer Architecture, Faculty of Electronics and Information Technology, Warsaw University of Technology (WUT).
-
Krzysztof Szczypiorski
Krzysztof Szczypiorski is a Professor of Telecommunications at the Institute of Telecommunications (IT), Faculty of Electronics and Information Technology (FEIT), Warsaw University of Technology (WUT), Poland.
-
Hui Tian
-
Articles (4 in this collection)
-

-
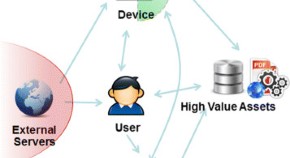
MUSE: asset risk scoring in enterprise network with mutually reinforced reputation propagation
Authors (first, second and last of 6)
- Xin Hu
- Ting Wang
- Reiner Sailer
- Content type: Research
- Open Access
- Published: 18 November 2014
- Article: 17
-
DNSSEC for cyber forensics
Authors
- Haya Shulman
- Michael Waidner
- Content type: Research
- Open Access
- Published: 22 October 2014
- Article: 16

-
PeerShark: flow-clustering and conversation-generation for malicious peer-to-peer traffic identification
Authors
- Pratik Narang
- Chittaranjan Hota
- VN Venkatakrishnan
- Content type: Research
- Open Access
- Published: 08 October 2014
- Article: 15



