Abstract
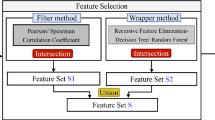
The widespread usage of the Internet has increased network security issues. Some of the serious threats are Brute force, Heartbleed, Botnet, Web attacks, DoS, DDoS, and Infiltration of the network. With the increased usage of online services and the development of new technologies like IoT, Cloud, Edge, and Mobile Computing, the detection of these threats is important and becoming paramount. This study presents an Intrusion Detection System (IDS) framework by proposing various hybrid models for the detection of malicious traffic. The models are developed using feature selection techniques, namely Recursive Feature Elimination, Chi-Square, Principal Component Analysis, and five Machine Learning (ML) techniques. In this experiment, the standard CSE-CIC-IDS 2018 dataset is used to examine the performance evaluation of the proposed approaches. In this paper, according to the comparison of the proposed hybrid approaches, Recursive Feature Elimination with Random Forest performs better than the other approaches with an accuracy of 99.23%. The proposed approach provides better accuracy as compared to earlier reported similar approaches in the literature.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Executive Perspectives Cisco Report (2022) Cisco Annual Internet Report–Cisco Annual Internet Report (2018–2023) White Paper. [online] Cisco. https://www.cisco.com/c/en/us/solutions/collateral/executive-perspectives/annual-internet-report/white-paper-c11-741490.html. Accessed 4 September 2022
Selvakumar K, Karuppiah M, Sairamesh L, Hafizul Islam SK, Hassan MM, Fortino G, Raymond Choo K-K (2019) Intelligent temporal classification and fuzzy rough set-based feature selection algorithm for intrusion detection system in WSNs. Inf Sci 497:77–90
Sharafaldin I, Lashkari AH, Ghorbani AA (2018) Toward generating a new intrusion detection dataset and intrusion traffic characterization. ICISSp 1:108–116
Unb.ca. 2022. IDS 2018 | Datasets | Research | Canadian Institute for Cybersecurity | UNB. https://www.unb.ca/cic/datasets/ids-2018.html. Accessed 4 September 2022
Samrin R, Vasumathi D (2017) Review on anomaly based network intrusion detection system. In: 2017 international conference on electrical, electronics, communication, computer, and optimization techniques (ICEECCOT). IEEE, pp 141–147
Ansari Md SA, Chattopadhayay A, Das S. A kernel level VFs logger for building efficient file system intrusion detection system. In: 2010 second international conference on computer and network technology. IEEE, pp 273–279
Elshafie HM, Mahmoud TM, Ali AA (2019) Improving the performance of the snort intrusion detection using clonal selection. In: 2019 international conference on innovative trends in computer engineering (ITCE). IEEE, pp 104–110
Keserwani PK, Govil MC, Pilli ES, Govil P (2021) An optimal NIDS for VCN using feature selection and deep learning technique: IDS for VCN. Int J Digit Crime Forensics (IJDCF) 13(6):1–25
Ansari Md SA, Pal K, Govil MC, Govil P, Srivastava A (2021) Ensemble machine learning for P2P traffic identification. Int J Comput Digit Syst
Yin C, Zhu Y, Fei J, He X (2017) A deep learning approach for intrusion detection using recurrent neural networks. IEEE Access 5:21954–21961
Nisioti A, Mylonas A, Yoo PD, Katos V (2018) From intrusion detection to attacker attribution: a comprehensive survey of unsupervised methods. IEEE Commun Surv Tutor 20(4):3369–3388
Ansari Md SA, Govil MC, Pal K, Samaddar SG (2020) Tools and techniques in optimization of network resources. In: 2020 3rd international conference on emerging technologies in computer engineering: machine learning and internet of things (ICETCE). IEEE, pp 1–7
Barbhuiya S, Papazachos Z, Kilpatrick P, Nikolopoulos DS (2018) RADS: real-time anomaly detection system for cloud data centres. arXiv:1811.04481
Alharbi A, Alsubhi K (2021) Botnet detection approach using graph-based machine learning. IEEE Access 9:99166–99180
Abou Daya A, Salahuddin MA, Limam N, Boutaba R (2020) BotChase: graph-based bot detection using machine learning. IEEE Trans Netw Serv Manage 17(1):15–29
Elsayed MS, Le-Khac NA, Dev S, Jurcut AD (2020) Detecting abnormal traffic in large-scale networks. In: 2020 international symposium on networks, computers and communications (ISNCC). IEEE, pp 1–7
Nguyen KK et al (2018) Cyberattack detection in mobile cloud computing: a deep learning approach. In: 2018 IEEE wireless communications and networking conference (WCNC). IEEE
Smys S, Basar A, Wang H (2020) Hybrid intrusion detection system for internet of things (IoT). J ISMAC 2(04):190–199
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2023 The Author(s), under exclusive license to Springer Nature Singapore Pte Ltd.
About this paper
Cite this paper
Biswas, S., Kumar, C., Som, S., Ansari, M.S.A., Govil, M.C. (2023). AI-Enabled IDS for Identifying Malicious Traffics in Cloud Systems. In: Borah, S., Gandhi, T.K., Piuri, V. (eds) Advanced Computational and Communication Paradigms . ICACCP 2023. Lecture Notes in Networks and Systems, vol 535. Springer, Singapore. https://doi.org/10.1007/978-981-99-4284-8_7
Download citation
DOI: https://doi.org/10.1007/978-981-99-4284-8_7
Published:
Publisher Name: Springer, Singapore
Print ISBN: 978-981-99-4283-1
Online ISBN: 978-981-99-4284-8
eBook Packages: Intelligent Technologies and RoboticsIntelligent Technologies and Robotics (R0)