Abstract
With the continuous development of cloud computing technology, the demand for enterprises to access the cloud has increased. At the same time, with the development of 4G and 5G network technology and the improvement of the performance of mobile devices, more and more users are accessing the enterprise network through mobile terminals. Gartner first proposed the concept of SASE (Secure Access Service Edge) in the report “The Future of Network Security Is in the Cloud”, which is a new solution for enterprise network interconnection and security issues protection in multi-branch scenarios by delivering network and security capabilities through distributed cloud. This article focused on analyzing the background, development history, key capability requirements and deployment architectures of SASE. In this article, a framework for key SASE capabilities is proposed, and two common SASE deployment frameworks are summarized. Finally, the future trend of SASE in terms of market, technology and application is prospected.
Access provided by Autonomous University of Puebla. Download conference paper PDF
Similar content being viewed by others
Keywords
1 Introduction
1.1 Development Background
The traditional network and security architecture is designed for the enterprise datacenter required for user and device access. The comprehensive development of Chinese digital economy requires new type of infrastructure. In 2020, with the top-down promotion of new infrastructure, 5G will become the infrastructure of the digital economy and 5G network will make large amounts of data distributed in their networks and infrastructure [1]. Therefore, the cloud computing pressure has increased sharply, and there is an urgent need for computing power to sink to the edge [2]. As such, we are likely to see major security risks arising from misconfigurations, poor network management, and secure integration between the network, meaning that cybersecurity risks directly impact the company operations [3, 4]. For IT business and cybersecurity managers, implementing complex policies to block potential cyberattacks will become more difficult, so the company needs to create a more robust edge network.
In this situation, the development of enterprises increasingly presents a coordinated and decentralized operation model of stores or branches, which significantly improves productivity and efficiency, but at the same time comes with security and efficiency challenges. With the outbreak of the global crown epidemic in early 2020, the trend of enterprises going to the cloud and remote mobile office continues to expand, and it is normalized [5]. The challenges brought to enterprises are network overhead, that is, business service quality, user speed experience, and security issues. It manifests as: Insufficient network application awareness, Low remote access performance and increased data security threats.
1.2 The Meaning of SASE
In 2019, Gartner first proposed the concept of SASE (Secure Access Service Edge) in the report “The Future of Network Security Is in the Cloud” [6], and defined it as an entity-based identity, real-time context, enterprise security/collaboration. The meaning of SASE is in the four key words:
-
1.
“Secure” means that SASE security design enables users to directly access cloud resources without connecting through MPLS or VPN, providing users with cloud access security proxy, secure web gateway, remote browser isolation, intrusion prevention, etc. Secondly.
-
2.
“Access” means an access principal whose identity is attached to each enterprise resource: person, application, service or device.
-
3.
“Service” means that providing network capabilities and security capabilities to users in the form of services.
-
4.
“Edge” means that every branch, mobile office, home office, and IoT device [7] that needs to be connected to the intranet can be regarded as the edge of the enterprise.
2 The Key Capabilities and Architectures
SASE is the integration of existing network and security technologies, so it is crucial to sort out the key abilities and architectures contained in SASE. The capability requirements of SASE are sorted out, and the capability framework of SASE is proposed. Then, the deployment architectures that conform to the SASE concept and key technical characteristics are proposed.
2.1 The Key Capability of SASE
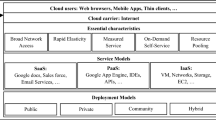
SASE is composed of four capability domains, which are network, security, cloud deployment, and unified management and control. Through these four capability domains, the normative requirements and tests for SASE's capabilities can be well put forward.
For network capability, SASE should have basic network connection capabilities to realize data interoperability between user terminals, branches, and data centers, and network management and acceleration capabilities [8] (Table 1).
The security capabilities of SASE include zero-trust access capabilities and different levels of security protection capabilities [9] (Table 2).
Cloud deployment capabilities are mainly cloud deployment and service orchestration capabilities of SASE (Table 3).
As one of the most critical capability domains of SASE, the unified management and control capability enables the joint scheduling and monitoring of multiple functional components and provides the capability to users through a unified interface [10] (Table 4).
2.2 The Deployment Architectures of SASE
Benefiting from the development of cloud computing and virtualized networks, SASE makes the network and security capabilities cloud-native and realizes a distributed architecture. When choosing the solution deployment architecture, SASE service providers give priority to the deployment and implementation of solutions that are highly compatible with their own products, such as software, hardware product advantages, and resource pool deployment advantages. At present, the mainstream deployment architecture of SASE can be divided into the following two types: PoP-based SASE architecture and gateway-based SASE architecture.
PoP-Based SASE Architecture.
PoP-based SASE architecture refers to an architecture that integrates the main capabilities of SASE into PoPs and transforms them into distributed security resource pools to provide access services. The PoP-based SASE architecture can be seen as an upgrade of the SD-WAN architecture, which is widely used by SD-WAN service providers and operators(see Fig. 1).
The PoP-based SASE architecture consists of the following parts:
PoP point: PoP point is usually composed of computer room, public cloud, private cloud, data center, etc., and jointly accept the unified control and scheduling of the SASE management and control platform. In terms of functions, through nodes deployed in various places, relying on traffic diversion and other means to provide users with the ability to access the SASE network nearby. On the one hand, PoP check traffic and implement functions such as zero-trust authentication, abnormal traffic analysis, and behavior auditing.
SASE management and control center: The SASE unified management and control platform is responsible for tasks such as management, scheduling, and decision-making of all PoPs.
Proxy gateway: The proxy gateway is installed in the form of software or hardware at the exit of terminals, branches, data centers, and public clouds, and is responsible for transferring registration and authentication information of the management and control plane and diverting user traffic to PoP points.
Gateway-Based SASE Architecture.
The difference between the gateway-based SASE architecture and the PoP-based architecture is that this architecture integrates functional components in the gateway instead of the PoP, thus eliminating the need for PoP construction and interconnection. This type of architecture is mostly found in network hardware manufacturers, and the advantage is to reduce the situation that users in remote areas cannot access nearby due to insufficient coverage of PoP points.

The gateway-based SASE architecture consists of the following parts:
SASE management and control center: The SASE unified management and control platform is responsible for tasks such as management, scheduling, and decision-making of all PoPs.
Proxy Gateway: The proxy gateway is installed in the form of software or hardware at the exit of terminals, branches, data centers, and public clouds, and is responsible for transferring registration and authentication information of the management and control plane and diverting user traffic to PoP points.
Please note that the first paragraph of a section or subsection is not indented. The first paragraphs that follows a table, figure, equation etc. does not have an indent, either.
3 The Future Trends of SASE in China
Due to the unique advantages of SASE technology and architecture, as well as the extensive and cutting-edge application scenarios, SASE will develop rapidly in the future market and technology waves, profoundly affecting the process of ICT industry and digital transformation.
In terms of Marketing, the SASE market has a large space for substitution, and the growth trend is relatively clear. As the country continues to promote the use of cloud by enterprises, the growth point of the SASE market will mainly come from the transformation of enterprise IT in 2022–2025 and the new growth brought by various mobile applications, public cloud, private cloud, computing power network and other technologies. Computing, network, and security needs, SASE will further expand the market for new needs. At the same time, with its own advantages, SASE will replace about 40% of the traditional network and security market in the next three years.
On the technical side, SASE will combine AI&5G to create new technical services. With the maturation of key technologies such as artificial intelligence, 5G and the rise of concepts related to intelligent cloud networks, major SASE vendors will move important technologies or solutions toward intelligence and automation.
In terms of application, SASE application scenarios will continue to develop ubiquitously. With the digital transformation and development of traditional industries such as smart cities and smart factories, the application scenarios of SASE are no longer limited to the behavioral safety of terminals and employees. In the future, by extending the capabilities of SD-WAN, SASE can integrate new security functions into the Internet of Things and solve the problems caused by the increase in the number of devices.
References
Xia, J.: China 5G: Opportunities and Challenges. J. Telecommu. Poli. 46(2) (2022)
Jeff, V.: How 6 top SD-WAN and SASE vendors are evolving. J. Network World (Online) (2022)
Tsochev, G.R., Trifonov, R.I.: Cloud computing security requirements: A Review. J. IOP Conference Series: Materials Science and Engineering 1216(1) (2022)
Maria, K.: Cato adds fine-grained CASB controls to SASE platform. J. Network World (Online) (2022)
Michael, W.: How SASE is defining the future of network security. Journal Network Security 2020(12), 6–8 (2020)
Wei, X.: Research on building a multi-cloud environment security defense framework based on Gartner's SASE idea. J. Info. Netw. Sec. 2021(S1), 222–226 (2021)
Martin, G.: CPaaS and SASE: the best defences against IoT threats. J. Netw. Sec. 2021(9), 9–12 (2021)
Simon, P.: SD-WAN revolutionises IoT and edge security. J. Netw. Sec. 2021(8), 14–15 (2021)
Zhiyong: Building zero trust network security based on SASE. J. Info. Comp. (Theoretical Edition) 34(01), 227–230 (2022)
Michael, C.: Juniper adds security upgrades for SASE, security management Journal. Network World (Online) (2022)
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2023 The Author(s), under exclusive license to Springer Nature Singapore Pte Ltd.
About this paper
Cite this paper
Chen, R., Yue, S., Zhao, W., Fei, M., Wei, L. (2023). Overview of the Development of Secure Access Service Edge. In: Wang, Y., Liu, Y., Zou, J., Huo, M. (eds) Signal and Information Processing, Networking and Computers. ICSINC 2022. Lecture Notes in Electrical Engineering, vol 996. Springer, Singapore. https://doi.org/10.1007/978-981-19-9968-0_17
Download citation
DOI: https://doi.org/10.1007/978-981-19-9968-0_17
Published:
Publisher Name: Springer, Singapore
Print ISBN: 978-981-19-9967-3
Online ISBN: 978-981-19-9968-0
eBook Packages: Computer ScienceComputer Science (R0)