Abstract
An optical asymmetric cryptosystem built on chaotic zone plate phase mask (CZPPM) has been proposed. Here the pixels of an image are shuffled by employing Arnold transform \(\left( {{\text{AT}}^{\omega } } \right)\) and is then modulated with the CZPPM featuring in the gyrator Transform domain (GT). This increases randomness and adds chaotic parameters that make the system highly secure. The proposed system strengthens the security of the cryptosystem and does not permit the attacker to retrieve the initial image without the expertise of keys. The robustness of the projected cryptosystem has been investigated and validated based on an extra degree of freedom by simulating on MATLAB 9.9.0 (R2020b), and investigational outcomes have been shown to emphasize the efficacy of the algorithm.
Access provided by Autonomous University of Puebla. Download conference paper PDF
Similar content being viewed by others
Keywords
1 Introduction
With substantial innovations in transmission and information processing technologies, it has become a challenge to convey the information with security. An optical 4f system of DRPE in Fourier domain proposed by Refregier and Javidi was a great accomplishment in this arena in 1995 [1]. This set off the path for many researchers for constructing other cryptosystem centered on DRPE with superior security and elevated noise diminution. These systems were still exposed to many attacks known as known plaintext attack (KPA) [2, 3], chosen plaintext or ciphertext attack (CPA, CCA), etc. [4] An idea has been taken in the direction to model an asymmetric system [5] that deliver solution to insecure transmission concern and make it resilient from numerous attacks by boosting the randomness and improving chaotic mask key parameters.
2 Key Generation: Chaotic Zone Plate Phase Mask
Chaotic random phase masks (CRPM) [6] are used to increase randomness and to add chaotic parameters which makes the system highly secure in terms of private keys. Logistic map is one dimension (1D) non-linear chaotic maps and is used to generate the randomness in the CRPM. It can be expressed [7, 8].
It is iterated \(n\) times. Where \(p\) is bifurcation parameter and lies between \(~0 < p < 4\), \(x_{0}\) is an initial value and \(x_{n} \in \left[ {0,1} \right]\) is an iterative value where \(n\) varies from 0 to M × N. \(M\) and \(N\) are size of a chaotic random mask in pixels. The 1D sequence \(X = x_{1} ,x_{2} ,~x_{3} ,x_{4} , \ldots ,~x_{{M \times N}}\) that is produced by Eq. (1) is rearranged into 2D matrix as \(Y = y_{{ij}}\), where \(i\) varies from \(\left\{ {1,2, \ldots ,M} \right\}\) and \(j\) varies from \(\left\{ {1,2, \ldots ,N} \right\}\) and \(y_{{ij}} \in \left( {0,1} \right)\). CRPM a 2D matrix is expressed as
The Fresnel lens is built on quadratic phase change and the efficacy of zone plates. It is given [3] by
where \(r\) is the lens radius, \(f\) is the focal length, and λ is the wavelength of incident light. Now, \({\text{CZPPM}}\left( {x,y} \right)\) is obtained by multiplying above two functions \(L_{{\lambda ,f}} \left( r \right)\) and \({\text{CRPM}}\left( {x,y} \right)\), i.e., Equation (1) and (2) and can be stated as
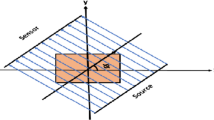
3 Proposed Cryptosystem
Asymmetric encryption technique built on CZPPM and \({\text{AT}}^{\omega }\) [9, 10] is proposed in this paper. The \({\text{AT}}^{\omega }\) scrambles the image \(I\left( {x,y} \right)\) of size \(M~ \times ~M\) by shuffling the pixels arbitrarily as in Eq. (5). Then the obtained result is transformed in gyrator domain [10], and phase is truncated to produce \(G\left( {u,v} \right)\) as in Eq. (6). The encrypted image is generated by multiplying \(G\left( {u,v} \right)\) with arbitrary phase mask in gyrator domain and further truncating its phase as in Eq. (7). The CZPPM and \({\text{AT}}^{\omega }\) applied through encryption operates as supplementary key because it comprises number of parameters as well as expands the randomness which further enhances the security.
Two decryption keys \({\text{DK}}_{1}\) and \({\text{DK}}_{2}\) were generated in the process where amplitude truncation is performed as shown in Eqs. (8) and (9)
The current graph of the planned encryption stated is displayed in Fig. 1.
The decipherment procedure is the reversal process of the encryption which retrieves the original image \(I\left( {x,y} \right)\). Following are the equations to decipher the encoded image \(E\left( {x,y} \right)\).
4 Simulations Results
This paper demonstrates the statistical analysis and simulation results verifies the sensitivity of the indicated procedure and reveals that it accomplishes superior performance of recuperating a good superiority image. Findings also confirms the protection assessment based on correlation coefficient, noise attack, and key sensitivity. Contemplate initial image of baboon with size 256 × 256.
For simulation values use are p = 3.96, x0 = 0.35, λ = 6328 Å, f = 200 mm, ω = 5 and orders of GT are α = 0.4π and β = 0.7π. Figure 2 shows the CZPPM key generated from CRPM and Fresnel zone plate (FZP).
4.1 Statistical Analysis
For statistical analysis, entropy [11] of the image has been analyzed, and the obtained value for baboon image is 6.319 which is close to standard value that guarantees failure of information is nearby zero. The information is homogenously scattered, and it does not deliver any valuable information to the attacker. It can be confirmed from the value obtained above that the projected system is extremely efficient.
Peak signal to noise ratio (PSNR) [12] achieved 23 dB after first level of phase retrieval and 28 dB attained after the second level of phase retrieval.
4.2 Performance Analysis
The mean square error (MSE) [13] determined for baboon image is 5.6346 × 10–22. Figure 3 presents the number of iterations versus MSE. Here, MSE drops with the increase in number of iterations and after 50 iterations, MSE becomes constant therefore image randomization stabilizes.
4.3 Robustness Analysis
The proposed algorithm is verified against occlusion attack [14, 15] where the encrypted image has been occluded for different sizes, but the images are still visible from human eye till 75% which proves the system is robust. 45% and 70% occluded encrypted images and its retrieved images are presented in Fig. 4.
4.4 Robustness Analysis
This system has been investigated against KPA, CPA, and special attack to verify its strength. Sets of initial and cipher images have been picked to uncover the authentic key, the erroneous value of parameter headed to incorrect generation of key. To verify the conjunction of the iteration procedure, MSE versus iterations are employed to recover the decryption keys. It can be viewed from MSE plot that decipherment key cannot be recovered even with large iteration number as shown in Fig. 5.
5 Conclusion
The proposed asymmetric cryptosystem improves the security of the scheme as chaotic mask shifts the phase of the retrieved output and scrambling creates dispersion in the system. The introduced masking accomplishes superior execution of PSNR, MSE, occlusion, and noise as equated to existing systems. The CZPPM is further protected and cannot recapture initial image without the knowledge of all the parameters utilized for producing key. Experimental result reveals the viability and robustness of asymmetric cryptosystem.
References
Refregier, P., Javidi, B.: Optical image encryption based on input plane and Fourier plane random encoding. Opt. Lett. 20(7), 767–769 (1995)
Peng, X., Zhang, P., Wei, H., Yu, B.: Known-plaintext attack on optical encryption based on double random phase keys. Opt. Lett. 31(8), 1044–1046 (2006)
Gopinathan, U., Monaghan, D.S., Naughton, T.J., Sheridan, J.T.: A known-plaintext heuristic attack on the Fourier plane encryption algorithm. Opt. Express 14(8), 3181–3186 (2006)
Zhang, C., Liao, M., He, W., Peng, X.: Ciphertext-only attack on a joint transform correlator encryption system. Opt. Express 21(23), 28523–28530 (2013)
Qin, W., Peng, X.: Asymmetric cryptosystem based on phase-truncated Fourier transforms. Opt. Lett. 35(2), 118–120 (2010)
Abuturab, M.R.: Asymmetric multiple information cryptosystem based on chaotic spiral phase mask and random spectrum decomposition. Opt. Laser Tech. 98, 298–308 (2018)
Barrera, J.F., Henao, R., Torroba, R.: Optics encryption method using toroidal zone plates. Opt. Commun. 248, 35–40 (2005)
Liansheng, S., Bei, Z., Xiaojuan, N., Ailing, T.: Optical multiple-image encryption based on the chaotic structured phase masks under the illumination of a vortex beam in the gyrator domain. Opt. Express 24(1), 499–515 (2016)
Chen, L., Zhao, D., Ge, F.: Image encryption based on singular value decomposition and Arnold transform in fractional domain. Opt. Commun. 291, 98–103 (2013)
Liu, Z., Chen, H., Liu, T., Li, P., Xu, L., Dai, J., Liu, S.: Image encryption by using gyrator transform and Arnold transform. J. Electron. Imaging. Proc. SPIE. 20(1), 013020 (2011)
Khurana, M., Singh, H.: A spiral-phase rear mounted triple masking for securing optical image encryption based on gyrator transform. Recent Patents Comput. Sci. 12(2), 80–94 (2019)
Khurana, M., Singh, H.: Two-level phase retrieval in fractional Hartley domain for secure image encryption and authentication using digital signatures. Multimedia Tools Appl. 79, 13967–13986 (2020)
Wang, S., Meng, X., Yin, Y., Wang, Y., Yang, X., Zhang, X., Peng, X., He, W., Dong, G., Chen, H.: Optical image watermarking based on singular value decomposition ghost imaging and lifting wavelet transform. Opt. Lasers Eng. 114, 76–82 (2019)
Liansheng, S., Xiao, Z., Chongtian, H., Ailing, T., Krishna Asundi, A.: Silhouette-free interference-based multiple-image encryption using cascaded fractional Fourier transforms. Opt. Lasers Eng. 113, 29–37 (2019)
Singh, H., Khurana, M.: An asymmetric optical cryptosystem of double image encryption based on optical vortex phase mask using Gyrator transform domain. Recent Patents Comput. Sci. 13(3), 672–685 (2020)
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2022 The Author(s), under exclusive license to Springer Nature Singapore Pte Ltd.
About this paper
Cite this paper
Khurana, M., Singh, H. (2022). Asymmetric Image Cryptosystem Based on Chaotic Zone Plate Phase Mask and Arnold Transform. In: Khanna, K., Estrela, V.V., Rodrigues, J.J.P.C. (eds) Cyber Security and Digital Forensics . Lecture Notes on Data Engineering and Communications Technologies, vol 73. Springer, Singapore. https://doi.org/10.1007/978-981-16-3961-6_5
Download citation
DOI: https://doi.org/10.1007/978-981-16-3961-6_5
Published:
Publisher Name: Springer, Singapore
Print ISBN: 978-981-16-3960-9
Online ISBN: 978-981-16-3961-6
eBook Packages: EngineeringEngineering (R0)