Abstract
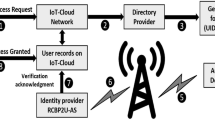
Internet-based client authentication protocols must be strengthened to reduce attacks and security vulnerabilities that threaten the performance of apps in fast Internet distribution and cloud computing. For secure access to services, IoT safety is thus of critical importance. High safety encryption with dual factors will be provided. This article offers a mobile user authentication with flexible biometric authentication and a core entry management framework for IoT services. The proposed system provides mutual encryption and an integral arrangement that ensures safe access to cloud servers. The legislation preserves anonymous user identity against the eavesdroppers, guarantees the security of the session key, and responds to the challenges.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
S. Challa, M. Wazid, A.K. Das, N. Kumar, A.G. Reddy, E.J. Yoon, K.Y. Yoo, Secure signature-based authenticated key establishment scheme for future IoT applications. IEEE Access 5, 3028–3043 (2017)
M. Wazid, A.K. Das, V. Odelu, N. Kumar, M. Conti, M. Jo, Design of secure user authenticated key management protocol for generic IoT networks. IEEE Internet of Things J. 5(1), 269–282 (2018)
Maissa Dammak, Omar Rafik Merad Boudia (Token-based lightweight authentication to secure IoT networks, IEEE CCNC, 2019)
Y. Park, Y. Park, Three-factor user authentication and key agreement using elliptic curve cryptosystem in wireless sensor networks. Sensors 16(12), 2123 (2017)
L. Atzori, A. Iera, G. Morabito, The internet of things: a survey. Comput. Netw. (2010)
H. Li, X. Zhou, Study on security architecture for Internet of Things. in Applied Informatics and Communication (Springer, Berlin, 2011), pp. 404–411
H.D. Ma, IOT: objectives and scientific challenges. J. Comput. Sci. Technol. (2011)
M. Thoma, S. Meyer, K. Sperner, S. Meissner, T. Braun, On iot-services: survey, classification and enterprise integration, in 2012 IEEE International Conference on Green Computing and Communications (GreenCom), November 2012. (IEEE, 2012), pp. 257–260
K.T. Nguyen, M. Laurent, N. Oualha, Survey on secure communication protocols for the Internet of Things. Ad Hoc Netw. (2015)
C.X. Ren, Y.B. Gong, F. Hao, X.Y. Cai, Y.X. Wu, When biometrics meet IoT: a survey, in Proceedings of the 6th International Asia Conference on Industrial Engineering and Management Innovation (Atlantis Press, 2016), pp. 635–643
J.K. Lee, S.R. Ryu, K.Y. Yoo, Fingerprint-based remote user authentication scheme using smart cards. Electron Lett. (2002)
C.H. Lin, Y.Y. Lai, A flexible biometrics remote user authentication scheme. Comput. Stand Interfaces (2004)
L. Chen, F. Wei, C. Ma, A secure user authentication scheme against smart-card loss attack for WSN using symmetric key techniques. Int. J. Distrib. Sens. Netw. 2015
A.K. Das, A. Goswami, A robust anonymous biometric-based remote user authentication scheme using smart cards. J. King Saud Univ.-Comput. Inf. Sci. (2015)
Y. An, Security analysis and enhancements of an effective biometric-based remote user authentication scheme using smart cards. BioMed Res. Int. (2012)
C.T. Li, M.S. Hwang, An efficient biometrics-based remote user authentication scheme using smart cards. J. Netw. Comput. Appl. (2010)
Y.P. Liao, C.M. Hsiao, A secure ECC-based RFID authentication scheme integrated with ID-verifier transfer protocol. Ad Hoc Netw. (2014)
B. Ndibanje, H.J. Lee, S.G. Lee, Security analysis and improvements of authentication and access control in the internet of things. Sensors (2014)
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2021 Springer Nature Singapore Pte Ltd.
About this paper
Cite this paper
Kameswara Rao, M., Santhi, S.G. (2021). A Novel User Authentication Protocol Using Biometric Data for IoT Networks. In: Rathore, V.S., Dey, N., Piuri, V., Babo, R., Polkowski, Z., Tavares, J.M.R.S. (eds) Rising Threats in Expert Applications and Solutions. Advances in Intelligent Systems and Computing, vol 1187. Springer, Singapore. https://doi.org/10.1007/978-981-15-6014-9_11
Download citation
DOI: https://doi.org/10.1007/978-981-15-6014-9_11
Published:
Publisher Name: Springer, Singapore
Print ISBN: 978-981-15-6013-2
Online ISBN: 978-981-15-6014-9
eBook Packages: Intelligent Technologies and RoboticsIntelligent Technologies and Robotics (R0)