Abstract
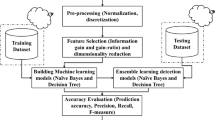
The traditional intrusion detection as one of the network security defense technology, plays an important role in the field of network security. But in a cloud environment application there response speed, data size, and many other restrictions, unable to meet the demand of real time validity, etc. Therefore, to build an intrusion detection system in cloud computing environment is an important subject. This paper aims at the design requirements of intrusion detection in cloud environment, through the research of the intrusion detection algorithm, proposed the use of Extreme Learning Machine (ELM) algorithm as an intrusion detection classification algorithm and the rationality verification using extreme learning machine algorithm. At the same time for massive high-dimensional intrusion detection data redundancy and noise influences the efficiency of detection by principal component analysis PCA algorithm for feature extraction, dimensionality reduction to improve the detection efficiency, reduces the detection time. Experiment results show that the algorithm is effective.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Helman, P., Liepins, G., Richards, W.: Foundations of intrusion detection. In: Proceedings of the Fifth Computer Security Foundations Workshop, pp. 114–120 (1992)
Jiang, J., Ma, H.: Summary of network security intrusion detection research. J. Softw. 11, 1460–1466 (2012)
Anderson, J.P.: Computer security threat monitoring and surveillance. Fort Washington: Pennsylvania 11(2), 65–68 (1980)
Helman, P., Liepins, G., Richards, W.: Foundations of intrusion detection. In: Proceedings of the Fifth Computer Security Foundations Workshop, pp. 114–120 (2002)
Huang, G.B., Zhu, Y.Q., Siew, C.K.: Extreme learning machine: a new learning scheme of feedforward neural networks. Proc. IJCNN 2, 985–990 (2004)
Huang, G.B., Chen, L.: Convex incremental extreme learning machine. Neuro Comput. 70, 3056–3062 (2007)
Huang, G.B., Chen, Y.Q., Babri, H.A.: Classification ability of single hidden layer feedforward neural networks. IEEE Trans. Neural Netw. 11(3), 799–801 (2014)
Mao, Y., Zhou, X.: Overview of feature selection algorithms. Pattern Recognit. AI 20(2), 211–218 (2007)
Jolliffe, I.T.: Principal Component Analysis. Springer, Berlin (2002)
KDD Cup 1999 Data: Information and Computer Science. University of California, Irivine. http://kdd.ics.uci.edu/databases/kddcup99/kddcup99.html
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2019 Springer Nature Singapore Pte Ltd.
About this paper
Cite this paper
Sang, Y. (2019). Research on Intrusion Detection Algorithm in Cloud Computing. In: Hung, J., Yen, N., Hui, L. (eds) Frontier Computing. FC 2018. Lecture Notes in Electrical Engineering, vol 542. Springer, Singapore. https://doi.org/10.1007/978-981-13-3648-5_205
Download citation
DOI: https://doi.org/10.1007/978-981-13-3648-5_205
Published:
Publisher Name: Springer, Singapore
Print ISBN: 978-981-13-3647-8
Online ISBN: 978-981-13-3648-5
eBook Packages: Intelligent Technologies and RoboticsIntelligent Technologies and Robotics (R0)