Abstract
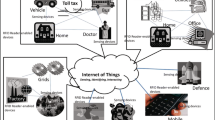
RFID (Radio Frequency IDentification) system has found enormous applications in retail, health care, transport, and home appliances. Over the years, many protocols have been proposed for RFID security using symmetric key and public key cryptography. Based on the nature of RFID tags’ usage in various applications, existing RFID protocols primarily focus on tag identification or authentication property. Internet of Things (IoT) is emerging as a global network in which every object in physical world would be able to connect to web of world via Internet. As a result, IoT infrastructure requires integration of several complimentary technologies such as sensor networks, RFID system, embedded system, conventional desktop environment, mobile communications and so on. It is prudent that RFID system will play significant roles in IoT infrastructure. In that context, RFID system should support more security properties, such as mutual authentication, key establishment and data confidentiality for its wide-spread adoption in future Internet applications. In this paper, we present a strong security and privacy of RFID system for its suitability in IoT infrastructure. The proposed protocol provides following security goal:
-
mutual authentication of tags and readers.
-
authenticated key establishment between tag and reader.
-
secure data exchange between tag-enabled object and reader-enabled things.
The protocol provides narrow-strong privacy and forward secrecy.
Access provided by Autonomous University of Puebla. Download to read the full chapter text
Chapter PDF
Similar content being viewed by others
References
European Commission: Internet of Things – An action plan for Europe, http://eur-lex.europa.eu/LexUriServ/LexUriServ.do?uri=COM:2009:0278:FIN:EN:PDF
Roman, R., Najera, P., Lopez, J.: Securing the Internet of Things. IEEE Computer 44(9), 51–58 (2011)
ISO/IEC 14443-2:2001. Identification cards – Contactless integrated circuit(s) cards – Proximity cards – Part 2: Radio frequency power and signal interface
Feldhofer, M., Dominikus, S., Wolkerstorfer, J.: Strong Authentication for RFID Systems using the AES Algorithm. In: Joye, M., Quisquater, J.-J. (eds.) CHES 2004. LNCS, vol. 3156, pp. 357–370. Springer, Heidelberg (2004)
Hopper, N., Blum, M.: Secure Human Identification Protocols. In: Boyd, C. (ed.) ASIACRYPT 2001. LNCS, vol. 2248, pp. 52–66. Springer, Heidelberg (2001)
Juels, A., Weis, S.A.: Authenticating Pervasive Devices with Human Protocols. In: Shoup, V. (ed.) CRYPTO 2005. LNCS, vol. 3621, pp. 293–308. Springer, Heidelberg (2005)
Gilbert, H., Robshaw, M., Sibert, H.: An Active Attack Against HB+ - a Provably Secure Lightweight Authentication Protocol. IET Electronic Letters 41(21), 1169–1170 (2005)
Bringer, J., Chabanne, H., Dottax, E.: HB++: a Lightweight Authentication Protocol Secure against Some Attacks. In: proceedings of Security, Privacy and Trust in Pervasive and Ubiquitous Computing, pp. 28–33 (2006)
Avoine, G., Oechslin, P.: RFID Traceability: A Multilayer Problem. In: S. Patrick, A., Yung, M. (eds.) FC 2005. LNCS, vol. 3570, pp. 125–140. Springer, Heidelberg (2005)
Peris-Lopez, P., Hernandez-Castro, J.C., Estevez-Tapiador, J.M., Ribagorda, A.: An Efficient Authentication Protocol for RFID Systems Resistant to Active Attacks. In: Denko, M.K., et al. (eds.) EUC-WS 2007. LNCS, vol. 4809, pp. 781–794. Springer, Heidelberg (2007)
Peris-Lopez, P., Hernandez-Castro, J.C., Tapiador, J.M.E., Li, T., van der Lubbe, J.C.A.: Weaknesses in Two Recent Lightweight RFID Authentication Protocols. In: Bao, F., Yung, M., Lin, D., Jing, J. (eds.) Inscrypt 2009. LNCS, vol. 6151, pp. 383–392. Springer, Heidelberg (2010)
Hernandez-Castro, J.C., Peris-Lopez, P., Phan, R.C.-W., Tapiador, J.M.E.: Cryptanalysis of the David-Prasad RFID Ultralightweight Authentication Protocol. In: Ors Yalcin, S.B. (ed.) RFIDSec 2010. LNCS, vol. 6370, pp. 22–34. Springer, Heidelberg (2010)
Vaudenay, S.: On privacy models for RFID. In: Kurosawa, K. (ed.) ASIACRYPT 2007. LNCS, vol. 4833, pp. 68–87. Springer, Heidelberg (2007)
Hankerson, D., Menezes, A., Vanstone, S.: Guide to Elliptic Curve Cryptography. Springer (2004)
Lee, Y.K., Batina, L., Verbauwhede, I.: Untraceable RFID Authentication Protocols: Revision of EC-RAC. In: Proceedings of the IEEE International Conference on RFID, pp. 178–185 (2009)
Hein, D., Wolkerstorfer, J., Felber, N.: ECC Is Ready for RFID – A Proof in Silicon. In: Avanzi, R.M., Keliher, L., Sica, F. (eds.) SAC 2008. LNCS, vol. 5381, pp. 401–413. Springer, Heidelberg (2009)
Lee, Y.K., Sakiyama, K., Batina, L., Verbauwhede, I.: Elliptic Curve Based Security Processor for RFID. IEEE Transactions on Computer 57(11), 1514–1527 (2008)
Oren, Y., Feldhofer, M.: A Low-resource Public-key Identification Scheme for RFID Tags and Sensor Nodes. In: Proceedings of the ACM Conference on Wireless Network Security, pp. 59–68 (2009)
Bringer, J., Chabanne, H., Icart, T.: Cryptanalysis of EC-RAC, a RFID Identification Protocol. In: Franklin, M.K., Hui, L.C.K., Wong, D.S. (eds.) CANS 2008. LNCS, vol. 5339, pp. 149–161. Springer, Heidelberg (2008)
Deursen, T., Radomirovic, S.: Attacks on RFID Protocols. Cryptology ePrint Archive: listing for 2008(2008/310) (2008)
van Deursen, T., Radomirović, S.: EC-RAC: Enriching a Capacious RFID Attack Collection. In: Ors Yalcin, S.B. (ed.) RFIDSec 2010. LNCS, vol. 6370, pp. 75–90. Springer, Heidelberg (2010)
Fan, J., Hermans, J., Vercauteren, F.: On the Claimed Privacy of EC-RAC III. In: Ors Yalcin, S.B. (ed.) RFIDSec 2010. LNCS, vol. 6370, pp. 66–74. Springer, Heidelberg (2010)
Lee, Y.K., Batina, L., Singelee, D., Verbauwhede, I.: Low-Cost Untraceable Authentication Protocols for RFID (extended version). In: Proceedings of the ACM Conference on Wireless Network Security (WiSec), pp. 55–64 (2010)
RFID Security & Privacy Lounge, http://www.avoine.net/rfid/
Hermans, J., Pashalidis, A., Vercauteren, F., Preneel, B.: A new RFID privacy model. In: Atluri, V., Diaz, C. (eds.) ESORICS 2011. LNCS, vol. 6879, pp. 568–587. Springer, Heidelberg (2011)
Schnorr, C.P.: Efficient identification and signatures for smart cards. In: Brassard, G. (ed.) CRYPTO 1989. LNCS, vol. 435, pp. 239–252. Springer, Heidelberg (1990)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2013 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Das, M.L. (2013). Strong Security and Privacy of RFID System for Internet of Things Infrastructure. In: Gierlichs, B., Guilley, S., Mukhopadhyay, D. (eds) Security, Privacy, and Applied Cryptography Engineering. SPACE 2013. Lecture Notes in Computer Science, vol 8204. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-41224-0_5
Download citation
DOI: https://doi.org/10.1007/978-3-642-41224-0_5
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-41223-3
Online ISBN: 978-3-642-41224-0
eBook Packages: Computer ScienceComputer Science (R0)