Abstract
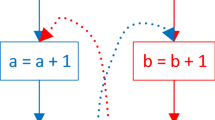
In this paper we propose a software watermarking technique based on the fact that different semantic instances might be abstracted in the same syntactic object. Our idea is to hide the watermark in a particular semantic instance and to distribute the corresponding syntactic construct. The extraction process uses a secret key in order to recover the information loss and reconstruct the watermark. In particular, we focus on loops and we base the embedding and extraction algorithm on the semantic understanding of loop-unrolling.
Access provided by Autonomous University of Puebla. Download to read the full chapter text
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
Apt, K.R., Plotkin, G.D.: Countable nondeterminism and random assignment. J. ACM 33(4), 724–767 (1986)
Bacon, D.F., Graham, S.L., Sharp, O.J.: Compiler transformations for high-performance computing. ACM Comput. Surv. 26(4), 345–420 (1994)
Cohen, F.B.: Operating system protection through program evolution. Comput. Secur. 12(6), 565–584 (1993)
Collberg, C., Carter, E., Debray, S., Huntwork, A., Kececioglu, J., Linn, C., Stepp, M.: Dynamic path-based software watermarking. SIGPLAN Not 39(6), 107–118 (2004)
Collberg, C., Thomborson, C.: Software watermarking: Models and dynamic embeddings. In: Principles of Programming Languages 1999, POPL 1999, San Antonio, TX (January 1999)
Collberg, C., Thomborson, C.: Watermarking, tamper-proofing, and obfuscation – tools for software protection. Technical Report TR00-03, University of Arizona (February 10, 2000)
Collberg, C., Thomborson, C., Low, D.: A taxonomy of obfuscating transformations. Technical Report 148, University of Auckland (July 1997)
Collberg, C., Thomborson, C., Low, D.: Manufacturing cheap, resilient, and stealthy opaque constructs. In: Principles of Programming Languages 1998, San Diego, CA (1998)
Cousot, P.: Constructive Design of a Hierarchy of Semantics of a Transition System by Abstract Interpretation. Theoretical Computer Science 277(1-2), 47–103 (2002)
Cousot, P., Cousot, R.: Abstract interpretation: a unified lattice model for static analysis of programs by construction or approximation of fixpoints. In: Conference Record of the Fourth Annual ACM SIGPLAN-SIGACT Symposium on Principles of Programming Languages, Los Angeles, California, pp. 238–252. ACM Press, New York (1977)
Cousot, P., Cousot, R.: Systematic design of program analysis frameworks. In: Conference Record of the Sixth Annual ACM SIGPLAN-SIGACT Symposium on Principles of Programming Languages, San Antonio, Texas, pp. 269–282. ACM Press, New York (1979)
Cousot, P., Cousot, R.: Systematic Design of Program Transformation Frameworks by Abstract Interpretation. In: Conference Record of the 19th ACM Symposium on Principles of Programming Languages, pp. 178–190. ACM Press, New York (2002)
Cousot, P., Cousot, R.: An abstract interpretation-based framework for software watermarking. In: Conference Record of the 31st Annual ACM SIGPLAN-SIGACT Symposium on Principles of Programming Languages, Venice, Italy, ACM Press, New York (2004)
Davidson, R.L., Myhrvold, N.: Method and systems for generating and auditing a signature for a computer program. US patent 5.559.884, Assignee: Microsoft Corporation (1996)
Moskowitz, S.A., Cooperman, M.: Method for stega-cipher protection of computer code. US patent 5.745.569, Assignee: The Dice Company (1996)
Nagra, J., Thomborson, C.D.: Threading software watermarks. In: Fridrich, J. (ed.) IH 2004. LNCS, vol. 3200, pp. 208–223. Springer, Heidelberg (2004)
Qu, G., Potkonjak, M.: Hiding signatures in graph coloring solutions. In: Pfitzmann, A. (ed.) IH 1999. LNCS, vol. 1768, pp. 348–367. Springer, Heidelberg (2000)
Shimanovsky, B., Feng, J., Potkonjak, M.: Hiding data in Dna. In: Revised Papers from the 5th International Workshop on Information Hiding, London, UK. Springer, Heidelberg (2003)
Weiser, M.: Program slicing. In: ICSE 1981: Proceedings of the 5th international conference on Software engineering, Piscataway, NJ, USA, pp. 439–449. IEEE Press, Los Alamitos (1981)
Author information
Authors and Affiliations
Editor information
Rights and permissions
Copyright information
© 2008 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Dalla Preda, M., Giacobazzi, R., Visentini, E. (2008). Hiding Software Watermarks in Loop Structures. In: Alpuente, M., Vidal, G. (eds) Static Analysis. SAS 2008. Lecture Notes in Computer Science, vol 5079. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-540-69166-2_12
Download citation
DOI: https://doi.org/10.1007/978-3-540-69166-2_12
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-69163-1
Online ISBN: 978-3-540-69166-2
eBook Packages: Computer ScienceComputer Science (R0)