Abstract
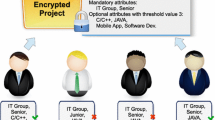
Ciphertext-policy attribute-based encryption(CP-ABE) has become a crucial technical for cloud computing in that it enables one to share data with users under the access policy defined by himself. Generally, the universe of attributes is not fixed before the system setup in practice. So in this paper, we propose a CP-ABE scheme with large attribute universe based on the scheme presented by Chen et al. The number of attributes is independent of the public parameter in our scheme, and it inherents the excellent properties of both constant ciphertext and constant computation cost.
Access provided by CONRICYT-eBooks. Download to read the full chapter text
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
Sahai A. and Waters B.: Fuzzy identity based encryption. In: Proc. Advances in Cryptology-Eurocrypt, pp. 457-473(2005)
Chen C., Zhang Z., and Feng D.: Efficient ciphertext-policy attribute-based encryption with constant-size ciphertext and constant computation-cost. In: Proc. ProveSec’11, pp. 84-101(2011)
Goyal V., Pandey O., Sahai A. andWaters B.: Attribute-based encryption for fine-grained access control of encrypted data. In: Proc. CCS’06, pp. 89-98(2006)
Ostrovsky R., Sahai A. and Waters B.: Attribute-based encryption with nonmonotonic access structures. In: Proc. ACM Conference on Computer and Communication Security, pp. 195-203(2007)
Bethencourt J., Sahai A. and Waters B.: Ciphertext-policy attribute-based encryption. In: Proc. IEEE Symposium on Security and Privacy, pp. 321-334(2007)
Cheung L. and Newport C.: Provably secure ciphertext policy abe. In: Proc. ACM Conference on Computer and Communication Security, pp. 456-465(2007)
Emura K., Miyaji A., Nomura A., et al.: A ciphertext-policy attribute-based encryption scheme with constant ciphertext length. In: Proc. ISPEC’09, pp. 13-23(2009)
Zhou Z., and Huang D.: On efficient ciphertext-policy attribute-based encryption and broadcast encryption. In: Proc. CCS’10, pp. 753-755(2010)
Ge A., Zhang R., Chen C., Ma C.and Zhang,Z.: Threshold ciphertext-policy attribute-based encryption with constant-size ciphertexts. In: Proc. ACISP’12, pp. 336-349(2012)
Chen C., Chen J., Lim H., et al.: Fully secure attribute-based systems with short ciphertexts/signatures and threshold access structures. In: Proc. CT-RSA’13, pp. 50-67(2013)
Guo F., Mu Y., Susilo W., Wong D.and Varadharajan,V.: CP-ABE with constant-size keys for lightweight devices. In: IEEE Trans. Inf. Forensics Security, vol.9, no.5, pp. 763-771(2014)
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2017 Springer International Publishing AG
About this paper
Cite this paper
Xiao, S., Ge, A., Wei, F., Ma, C. (2017). Ciphertext-Policy Attribute Based Encryption with Large Attribute Universe. In: Xhafa, F., Barolli, L., Amato, F. (eds) Advances on P2P, Parallel, Grid, Cloud and Internet Computing. 3PGCIC 2016. Lecture Notes on Data Engineering and Communications Technologies, vol 1. Springer, Cham. https://doi.org/10.1007/978-3-319-49109-7_11
Download citation
DOI: https://doi.org/10.1007/978-3-319-49109-7_11
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-319-49108-0
Online ISBN: 978-3-319-49109-7
eBook Packages: EngineeringEngineering (R0)