Abstract
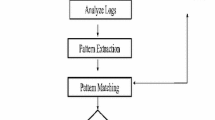
Monitoring network communication is one of the primary methods used for years to combat network threats. Recent attacks on corporations networks shows that classical perimeter centric detection methods, based on the analysis of signatures, statistical anomalies or heuristic methods aimed at protection from the outside do not work, and are easily circumvented by new generations of malware. Increasingly apparent becomes the need to create additional internal line of defense, aimed at detecting and blocking what penetrated inside and operates in a network environment. The paper presents such solution – a new method for threats detection, based on novel principle – local monitoring and analysis of the system and application’s network activity, detecting traces of malware operation to the level of process running on the system.
Access provided by Autonomous University of Puebla. Download to read the full chapter text
Chapter PDF
Similar content being viewed by others
Keywords
References
2013 Data Breach Investigations Report. Verizon, http://www.verizonenterprise.com/DBIR/2013/
Fortinet 2013 Cybercrime Report. Fortinet, http://www.fortinet.com/resource_center/whitepapers/cybercrime_report_on_botnets_network_security_strategies.html
2013 Information Security Breaches Survey, https://www.gov.uk/government/publications/information-security-breaches-survey-2013-technical-report
The Demise in Effectiveness of Signature and Heuristic Based Antivirus, http://docs.media.bitpipe.com/io_10x/io_102267/item_632588/2013-01-09_the_demise_of_signature_based_antivirus_final.pdf
Defeating Advanced Persistent Threat Malware. Infoblox, http://securematics.com/sites/default/files/secure/default/files/pdfs/infoblox-whitepaper-defeating-apt-malware.pdf
Piper, S.: Definitive Guide to Next-Generation Threat Protection. CyberEdge Group, LLC, http://www2.fireeye.com/definitive-guide-next-gen-threats.html
Assessing the Effectiveness of Antivirus Solutions, Hacker Intelligence Initiative, Monthly Trend Report #14, http://www.imperva.com/docs/HII_Assessing_the_Effectiveness_of_Antivirus_Solutions.pdf
Skrzewski, M.: Analyzing Outbound Network Traffic. In: Kwiecień, A., Gaj, P., Stera, P. (eds.) CN 2011. CCIS, vol. 160, pp. 204–213. Springer, Heidelberg (2011)
ENISA Threat Landscape 2013 – Overview of current and emerging cyber-threats, https://www.enisa.europa.eu/activities/risk-management/evolving-threat-environment/enisa-threat-landscape-2013-overview-of-current-and-emerging-cyber-threats
IBM X-Force 2013 Mid-Year Trend and Risk Report. IBM, http://www-03.ibm.com/security/xforce/downloads.html
The Advanced Cyber Attack Landscape. FireEye, Inc., http://www.security-finder.ch/fileadmin/dateien/pdf/studien-berichte/fireeye-advanced-cyber-attack-landscape-report.pdf
Skrzewski, M.: Monitoring system’s network activity for rootkit malware detection. In: Kwiecień, A., Gaj, P., Stera, P. (eds.) CN 2013. CCIS, vol. 370, pp. 157–165. Springer, Heidelberg (2013)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2014 Springer International Publishing Switzerland
About this paper
Cite this paper
Skrzewski, M. (2014). System Network Activity Monitoring for Malware Threats Detection. In: Kwiecień, A., Gaj, P., Stera, P. (eds) Computer Networks. CN 2014. Communications in Computer and Information Science, vol 431. Springer, Cham. https://doi.org/10.1007/978-3-319-07941-7_14
Download citation
DOI: https://doi.org/10.1007/978-3-319-07941-7_14
Publisher Name: Springer, Cham
Print ISBN: 978-3-319-07940-0
Online ISBN: 978-3-319-07941-7
eBook Packages: Computer ScienceComputer Science (R0)