Abstract
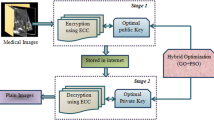
As a part of the information technology (IT) curriculum and to gain practical knowledge and skills in the field of technology, we have proposed an approach on “EncryptoX, as a Secure Storage System (SSS) using Hybrid Cryptography.” The main objective behind doing this project report is to gain skills and knowledge regarding various cryptography and storage techniques. In this study, we have included various techniques, concepts, better methods of data storage, and preservation employing software testing. As the world is moving further into the digital era and generating vast amount of data, thus securing emerges to be very crucial.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Osman, I., & Kelly, J.. (1996). Meta-hueuristics theory and applications. ISBN: 978-1-4613-1361-8, pp. 1–690.
Sharma, M., & Kaur, P. (2021). A comprehensive analysis of nature-inspired meta-heuristic techniques for feature selection problem. Archives of Computational Methods in Engineering, 28, 1103–1127.
Nick, A., & Lee, G..(2017). Cloud computing principles, systems and applications. ISBN: 978-3-319-54645-2 (pp. 1–378).
https://nevonprojects.com/secure-file-storage-on-cloud-using-hybrid-cryptography/
Reece, B. D., & Ruby, D. (2020). Secure file storage on cloud using hybrid cryptography. International Journal of Engineering and Technical Research, 8(03).
Jena, A., Das, A. K., Mohapatra, H., & Prasad, D. (2020). Automated software testing foundations, applications and challenges, ISBN:978-981-15-2455-4 (pp. 1–165).
Ellims, M., & Jackson, K., ISO 9001: Making the right mistakes. SAE technical paper series 2000-01-0714.
Davis, M., & Weyuker, E. J. (1998). Metric-based test data adequacy criteria. Computer Journal, 13(1), 17–24.
Jorgensen, P. (1995). Software testing a craftsman’s approach. CRC Press.
Lyu, M. R., Huang, Z., Sze, S. K., & Cai, X. (2003). An empirical study on testing and fault tolerance for software reliability engineering. Proceedings – International Symposium on Software Reliability Engineering, 2003, 119–130.
Cabe, M., & T. J. (1976). A complexity measure. IEEE Transactions on Software Engineering, 2(4), 202–213.
Richard, D. J., & Thompson, M. C. (1993). An analysis of test data selection criteria using the relay model of fault detection. IEEE Transactions on Software Engineering, 19(6), 533–553.
Torkar, R., Mankefors, S., Hansson, K., & Jonsson, A. (2003). An exploratory study of component reliability using unit testing. In Proceeding 14 international symposium on system reliability engineering (pp. 227–233).
Zhu, H., Hall, P. A. V., & May, J. H. R. (1997). Software unit test coverage and adequacy. ACM Computing Surveys, 29(4), 366–427.
Voas, J. M., & Miller, K. W. (1995). Software testability: The new verification. IEEE Software, 12, 17–18.
Zhu, H. (1996). A formal analysis of subsume relation between software testing adequacy criteria. IEEE Transactions on Software Engineering, 22(4), 248–255.
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2022 Springer Nature Switzerland AG
About this chapter
Cite this chapter
Priyadarshini, S.B.B., Sahu, A.A., Ray, V., Ray, P., Subudhi, S. (2022). EncryptoX: A Hybrid Metaheuristic Encryption Approach Employing Software Testing for Secure Data Transmission. In: Khari, M., Mishra, D.B., Acharya, B., Gonzalez Crespo, R. (eds) Optimization of Automated Software Testing Using Meta-Heuristic Techniques. EAI/Springer Innovations in Communication and Computing. Springer, Cham. https://doi.org/10.1007/978-3-031-07297-0_11
Download citation
DOI: https://doi.org/10.1007/978-3-031-07297-0_11
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-031-07296-3
Online ISBN: 978-3-031-07297-0
eBook Packages: Intelligent Technologies and RoboticsIntelligent Technologies and Robotics (R0)