Abstract
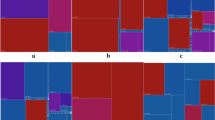
The traffic among the hosts and behaviors of the anomalous hosts in the network is usually complex. In network traffic, there is a key problem that is how to identify the security incidents. The corresponding question that who have contributed to the incidents is arisen then. A method, which detects both anomalies and events at the same time is quite helpful. A data from network traffic can be composed of the hosts and different attributes (traffic flow like amount of upload package and download package) in time series. Based on the structure of the network traffic data, we propose an anomaly and event detection method based on the network attributes in time series. The method analyzes both the host’s behavior and the temporal features of the network traffic.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Huang, H., Al-Azzawi, H., Brani, H.: Network traffic anomaly detection. Eprint Arxiv (2014)
Gupta, M., Gao, J., Aggarwal, C., Han, J.: Outlier detection for temporal data: a survey. IEEE Trans. Knowl. Data Eng. 26(9), 2250–2267 (2014)
Ide, T., Kashima, H.: Eigenspace-based anomaly detection in computer systems. In: Proceedings of the 10th ACM SIGKDD, pp. 440–449, August 2004
Akoglu, L., Faloutsos, C.: Event detection in time series of mobile communication graphs. In: Proceedings of Army Science Conference, vol. 2 (2008)
Ahmed, M., Mahmood, A., Hu, J.: A survey of network anomaly detection techniques. J. Netw. Comput. Appl. 60, 19–31 (2015)
Monowar, H., Bhuyan, D., Bhattacharyya, K., Kalita, J.: Network traffic anomaly detection: methods, systems and tools. IEEE Commun. Surv. Tutor. 16(1), 303–336 (2014)
Lakhina, A., Crovella, M., Diot, C.: Diagnosing network-wide traffic anomalies. ACM Sigcomm Comput. Commun. Rev. 34(4), 219–230 (2004)
Novakov, S., Lung, C., Lambadaris, I., Seddigh, N.: Combining statistical and spectral analysis techniques in network traffic anomaly detection. In: 2012 Next Generation Networks and Services, pp. 94–101 (2012)
Kaur, G., Saxena, V., Gupta, J.: A novel multi scale approach for detecting high bandwidth aggregates in network traffic. Int. J. Secur. Appl. 7(5), 81–100 (2013)
Kwon, D.W., Ko, K., Vannucci, M., Reddy, A.L.N., Kim, S.: Wavelet methods for the detection of anomalies and their application to network traffic analysis. Qual. Reliab. Eng. Int. 22(8), 953–969 (2006)
Gao, J., Fan, W., Turaga, D., Verscheure, O.: Consensus extraction from heterogeneous detectors to improve performance over network traffic anomaly detection. In: Proceedings - IEEE INFOCOM, vol. 267, no. 2, pp. 181–185 (2011)
Mansman, F., Meier, L., Keim, D.A.: Visualization of host behavior for network security. In: VizSEC 2007, pp. 187–202 (2007)
Iglesias, F., Zseby, T.: Analysis of network traffic features for anomaly detection. Mach. Learn. 101, 59–84 (2015)
Br, B.: Multi-scale analysis and modeling using wavelets. J. Chemom. 13(3–4), 415–434 (1999)
Acknowledgement
This work is partially supported by National Natural Science Foundation of China (Grant No. 61702372, No. 61672380) and The Fundamental Research Funds for the Central Universities of China.
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2020 Springer Nature Switzerland AG
About this paper
Cite this paper
Zhao, Q., Zhang, Y., Shi, Y., Li, J. (2020). Analyzing and Visualizing Anomalies and Events in Time Series of Network Traffic. In: Boonyopakorn, P., Meesad, P., Sodsee, S., Unger, H. (eds) Recent Advances in Information and Communication Technology 2019. IC2IT 2019. Advances in Intelligent Systems and Computing, vol 936. Springer, Cham. https://doi.org/10.1007/978-3-030-19861-9_2
Download citation
DOI: https://doi.org/10.1007/978-3-030-19861-9_2
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-030-19860-2
Online ISBN: 978-3-030-19861-9
eBook Packages: Intelligent Technologies and RoboticsIntelligent Technologies and Robotics (R0)