Abstract
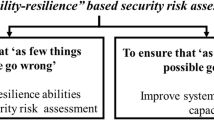
Security mitigation strategies are being designed, installed and operated in the protection of a diverse range of assets including people, information and physical buildings or sites. Some of these mitigation strategies are informed by risk and are instigated to address a particular threat or to reduce a known vulnerability. Nevertheless, many of these mitigation strategies are put into place with little regard for the greater system, being the organization and/or the security system. Such an approach reduces the ability of security to be effective, a significant issue as security has the capacity to bear multiple meanings (Smith and Brooks, 2013: 6) that result in differing views of what needs to be achieved when providing security.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Preview
Unable to display preview. Download preview PDF.
Similar content being viewed by others
References
Barton, J. and Haslet, T. (2007). Analysis, Synthesis, Systems Thinking and Scientific Method: Rediscovering the Importance of Open Systems.. Systems Research and Behavioural Science, 24, 143–155.
Beard, B. and Brooks, D.J. (2009). Consensual Security Risk Assessment: Overcoming Bias, Conflicting Interests and Parochialism. Paper presented at the Proceedings of the 2nd Australian Security and Intelligence Conference, Perth.
Bertalanffy, L.V. (1950). The Theory of Open Systems in Physics and Biology.. Science, New Series, 111(2872), 23–29.
Bertalanffy, L.V. (1968). General Systems Theory: Foundations, Development, Application. New York: George Braziller, Inc.
Brooks, D.J. (2010). What Is Security: Definition Through Knowledge Categorisation.. Security Journal, 23(3), 225–239.
Brooks, D.J. (2011). Security Risk Management: A Psychometric Map of Expert Knowledge Structure.. Risk Management: An International Journal, 13(1/2), 17–41. doi: 10.1057/rm.2010.7.
Building Technology Division (1997). GSA Security Criteria. Public Building Services, General Services Administration.
CCTViNFO (2009). Quadrant Security Completes First UK Installation to Use Cisco Surveillance Technology. Accessed June 13, 2013, from http://www.cctvinfo.com/news_article.aspx?news_id=6686
Coole, M. and Brooks, D.J. (2011). Mapping the Organizational Relations Within Physical Security’s Body of Knowledge: A Management Heuristic of Sound Theory and Best Practice. Paper presented at the 4th Australian Security and Intelligence Conference, Perth.
Cubbage, C. and Brooks, D.J. (2012). Corporate Security in the Asia Pacific Region: Crisis, Crime, Fraud and Misconduct. Boca Raton, FL: Taylor & Francis.
Department of Defense (2006). Unified Facilities Criteria: Security Engineering Electronics Security Systems. Author.
Dominguez, D., Parks, J., Williams, A. and Washburn, S. (2012). Special Nuclear Material and Critical Infrastructure Security Modeling and Simulation of Physical Protection Systems. Paper presented at the 46th Annual IEEE International Carnahan Conference on Security Technology, Boston.
Fischer, R.J. and Green, G. (2004). Introduction to Security. 7th ed. Boston: Butterworth Heinemann.
Fischer, R.J., Halibozek, E. and Green, G. (2008). Introduction to Security. 8th ed. Boston: Butterworth-Heinemann.
Garcia, M.L. (2008). The Design and Evaluation of Physical Protection Systems. 2nd ed. Burlington, MA: Butterworth-Heinemann.
Haimes, Y.Y. (2006). On the Definition of Vulnerabilities in Measuring Risks to Infrastructures.. Risk Analysis, 26(2), 293–296.
INCOSE (2006). Systems Engineering Handbook: A Guide for System Life Cycle Processes and Activities. International Council on Systems Engineering.
Keren, M. (1979). Ideological Implications of the Use of Open Systems Theory in Political Science.. Behavioural Science, 24, 311–324.
Knoke, M.E. (2012). Physical Security: Protection of Assets Manual. Alexandria, VA: ASIS International.
Koffka, K. (1963). Principles of Gestalt Psychology. New York: Harcourt, Brace & World Inc.
Lord, S. and Nunes-Vaz, R. (2013). Designing and Evaluating Layered Security.. International Journal of Risk Assessment and Management, 17(1), 19–45.
Lussier, R.N. (2009). Management Fundamentals: Concepts, Applications, Skills Development, 4th ed. Mason, OH: South-Western Cengage Learning.
Manunta, G. and Manunta, R. (2006). Theorizing about Security, in Gill, M. (ed.) The Handbook of Security. New York: Palgrave Macmillan. pp. 629–657.
Midgley, G. (2003). Systems Thinking: General Systems Theory, Cybernetics and Complexity. London: Sage.
Popper, K. (1963). Conjectures and Refutations: The Growth of Scientific Knowledge. London: Routledge.
Rogers, B.B. (2006). Engineering Principles for Security Managers, in Gill, M. (ed.) The Handbook of Security. Basingstoke: Palgrave Macmillan. pp. 66–89.
Roper, C.A. (1999). Risk Management for Security Professionals. Woburn, WA: Butterworth Heinermann.
Seldon, A. (ed.) (2012). The CCTV Handbook. Randburg: Technews Publishing (Pty) Ltd.
Smith, C.L. and Brooks, D.J. (2013). Security Science: The Theory and Practice of Security. Waltham, MA: Elsevier.
Standards Australia (2009). AS/NZS ISO31000:2009 Risk Management: Principles and Guidelines. Sydney: Standards Australia International Ltd.
Standards Australia (2012). Risk Management: Guidelines on Risk Assessment Techniques. Sydney: Author.
Talbot, J. and Jakeman, M. (2009). Security Risk Management: Body of Knowledge. 2nd ed. Hoboken, New Jersey: John Wiley & Sons, Inc.
Winston, A. (2009). CCTV Complexity Can Be Repaired. Accessed June 13, 2013, from http://www.bdonline.co.uk/news/international/cctv-complex-can-be-repaired-say-oma/3152195.article
Wittgenstein, L. (1953/2001). Philosophical Investigations. Oxford: Blackwell Publishing.
Editor information
Editors and Affiliations
Copyright information
© 2014 David Brooks and Clifton L. Smith
About this chapter
Cite this chapter
Brooks, D., Smith, C.L. (2014). Engineering Principles in the Protection of Assets. In: Gill, M. (eds) The Handbook of Security. Palgrave Macmillan, London. https://doi.org/10.1007/978-1-349-67284-4_6
Download citation
DOI: https://doi.org/10.1007/978-1-349-67284-4_6
Publisher Name: Palgrave Macmillan, London
Print ISBN: 978-1-349-67286-8
Online ISBN: 978-1-349-67284-4
eBook Packages: Palgrave Social Sciences CollectionSocial Sciences (R0)