Abstract
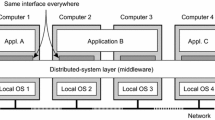
Distributed object technologies offer promise for improvements in system flexibility and evolvability but pose new challenges for both data management and security. Data management can be implemented either through distributed object interfaces added to a conventional database system architecture or through decoupled, distributed components that coordinate to provide database capabilities. Key security issues include security context and responsibilities in n-tiered architectures and in decoupled data management components, security-awareness of applications, and assurance.
Chapter PDF
Similar content being viewed by others
References
Benzel, T.C.V. and Sebes, E.J. (1996) Security for distributed object interoperability between trusted and untrusted systems, Proceedings of the Annual Computer Security Applications Conference.
Blakeley, J.A. (1996) Data access for the masses through OLE DB. SIGMOD Record, 25 (2), 161–172.
Chappell, D. (1996) Understanding ActiveX and OLE. Microsoft Press, Redmond, Washington.
Common Criteria Editorial Board (1996) Common Criteria for Information Technology Security Evaluation, CCEB-961011, V.1.0.
Microsoft Corp. (1997) Component Object Model Introduction, http://www.microsoft.com/oledev/olecom/Ch01.htm.
Microsoft Corp. (1997a) Microsoft: Universal Data Access,http://www.microsoft.com/data.
National Computer Security Center (1985) Department of Defense Trusted Computer Systems Evaluation Criteria, DOD 5200.28-STD.
National Security Agency/Object Management Group (1997), CORBA security implementers’ panel discussion, Proceedings of CORBA Security Workshop.
Object Management Group (1995) The Common Object Request Broker: Architecture and Specification, Revision 2.0.
Object Management Group (1996) Common Secure Interoperability, orbosl96–05–07.
Object Management Group (1997) CORBA Services: Common Object Services Specification, Chapter 15,Security Services Specification.
Object Management Group (1997a), OMA Executive Overview, http://www.omg.org/omg00%omaov.htm.
Simon, R. and Zurko, M.E. (1996) Adage: An Architecture for Distributed Authorization, The Open Group Research Institute.
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 1998 IFIP
About this chapter
Cite this chapter
McCollum, C.D., Faatz, D.B., Herndon, W.R., Sebes, E.J., Thomas, R.K. (1998). Distributed object technologies, databases, and security. In: Lin, T.Y., Qian, S. (eds) Database Security XI. IFIP Advances in Information and Communication Technology. Springer, Boston, MA. https://doi.org/10.1007/978-0-387-35285-5_2
Download citation
DOI: https://doi.org/10.1007/978-0-387-35285-5_2
Publisher Name: Springer, Boston, MA
Print ISBN: 978-1-5041-2914-5
Online ISBN: 978-0-387-35285-5
eBook Packages: Springer Book Archive