Abstract
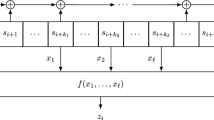
The fast correlation attack described by Meier and Staffelbach
Preview
Unable to display preview. Download preview PDF.
Similar content being viewed by others
References
W. Meier and O. Staffelbach, “Fast correlation attacks on certain stream ciphers”, Journal of Cryptology, vol. 1, no. 3, pp. 159–176, 1989.
D. Coppersmith, “Fast evaluation of logarithms in fields of characteristic two”, IEEE Trans. on Information Theory, vol. IT-30, no. 4, pp. 587–594, July 1984.
J. L. Massey, “Shift-register synthesis and BCH decoding”, IEEE Trans. Information Theory, vol. IT-15, pp. 122–127, 1969.
T. Siegenthaler, “Decrypting a class of stream ciphers using ciphertext only”, IEEE Trans. Computers, vol. C-34, pp. 81–85, 1985.
J. O. Brüer, “On nonlinear combinations of linear shift register sequences”, in Proc. IEEE ISIT, les Arcs, France, June 21–25 1982.
P. R. Geffe, “How to protect data with ciphers that are really hard to break”, Electronics, pp. 99–101, January 1973.
V. S. Pless, “Encryption schemes for computer confidentiality”, IEEE Trans. Computers, vol. C-26, pp. 1133–1136, November 1977.
C. Chepyzhov and B. Smeets, “On a fast correlation attack on stream ciphers”, in Advances in Cryptology — EUROCRYPT '91. 1991, pp. 176–185, Springer-Verlag.
M. J. Mihaljevic and J. Golic, “A comparison of cryptanalytic principles based on iterative error-correction”, in Advances in Cryptology — EUROCRYPT '91. 1991, pp. 527–531, Springer-Verlag.
K. Zeng and M. Huang, “On the linear syndrome method in cryptanalysis”, in Advances in Cryptology — CRYPTO '88. 1990, pp. 469–478, Springer-Verlag.
K. Nishimura and M. Sibuya, “Probability to meet in the middle”, J. of Cryptology, vol. 2, no. 1, pp. 13–22, 1990.
K. Huber, “Some comments on Zech's logarithm”, IEEE Trans. Information Theory, vol. IT-36, no. 4, pp. 946–950, July 1990.
A. M. Odlyzko, “Discrete logarithms and their cryptographic significance”, in Advances in Cryptology — EUROCRYPT '84. 1985, pp. 224–314, Springer-Verlag.
I. F. Blake, R. Fuji-Hara, R. C. Mullin, and S. A. Vanstone, “Computing logarithms in finite fields of characteristic two”, SIAM Journal on Algebraic Discrete Methods, vol. 5, pp. 276–285, 1985.
Author information
Authors and Affiliations
Editor information
Rights and permissions
Copyright information
© 1995 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Penzhorn, W.T., Kühn, G.J. (1995). Computation of low-weight parity checks for correlation attacks on stream ciphers. In: Boyd, C. (eds) Cryptography and Coding. Cryptography and Coding 1995. Lecture Notes in Computer Science, vol 1025. Springer, Berlin, Heidelberg. https://doi.org/10.1007/3-540-60693-9_10
Download citation
DOI: https://doi.org/10.1007/3-540-60693-9_10
Published:
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-60693-2
Online ISBN: 978-3-540-49280-1
eBook Packages: Springer Book Archive