Abstract
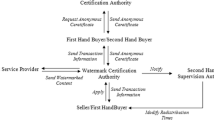
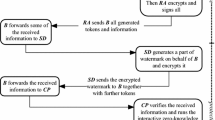
Anonymity is one of important requirements for electronic marketplaces to offer similar privacy as current marketplace. Unfortunately, most watermarking protocols in the literature have been developed without considering a buyer’s anonymity. It would be unsatisfactory for the buyer to reveal his/her identity to purchase multimedia contents. In this paper we propose an anonymous buyer-seller watermarking protocol, where a buyer can purchase contents anonymously, but anonymity control is provided, i.e., a seller can trace the identity of a copyright violator. The proposed scheme also provides unlinkability of contents purchased by a buyer. Another distinct feature of our scheme is that the identification of an illegal buyer is accomplished in a way such that the seller can directly convince a judge that the buyer has redistributed contents. This feature removes any possibility of dispute. Furthermore, when the innocent buyer is falsely accused by a malicious seller, it is possible to prove his/her innocence without attending a court and revealing any privacy.
This work was supported by grant No.R 01-2001-000-00537-0 (2002) from the Korea Science & Engineering Foundation.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Preview
Unable to display preview. Download preview PDF.
Similar content being viewed by others
References
N. Asokan, V. Shoup, and M. Waidner, Optimistic fair exchange of digital signatures, IEEE Journal on selected Areas in communications, 18(4), pp.591–610, Apr.2000. 423, 426
F. Bao, An Efficient Verifiable Encryption scheme for Encryption of Discrete Logarithms, CARDIS’98, vol.1820 of LNCS2000. 423, 426
S. Brands Untraceable Off-line Cash in Wallets with Observers Advances In Cryptology: Proc of CRYPTO’93, pp.302–318, 1994. 423
G. R. Blakley, C. Meadows, G.B. Purdy Fingerprinting Long Forgiving Messages, Crypto’85, LNCS 218, Springer-Verlag, Berlin 1986, 180–189. 421, 423
D. Boneh and J. Shaw, Collusion-Secure Fingerprinting for Digital Data, Crypto’95, LNCS 963, pp. 452–465, Springer-Verlag, Berlin, 1995. 421, 422, 423
J. Camenisch and I. Damgard, Verifiable encryption and applications to group signatures and signatures sharing, Technical Report RS 98-32, Brics, Department of Computer Science, University of Aarhus, Dec.1998. 423, 426
D. Chaum, A. Fiat, and M. Naor, Untraceable Electronic Cash Advances in Cryptology-CRYPTO’88, pp.319–327,1990. 423
I. J. Cox, J. Kilian, T. Leighton, and T. Shamoon, Secure spread spectrum watermarking for images, audio and video, IEEE Trans.on Image Processing, vol.6, no.12, pp.1673–1678, 1997. 421, 422
S. Craver, N. Memon, B. L. Yeo, and M. M. Yeung, Can Invisible Watermarks Resolve Rightful Ownership?, IBM research Report, RC 20509, July 25, 1996. 421
S. Craver, N. Memon, B. L. Yeo, and M. M. Yeung, Resolving Rightful Ownership with invisible Watermarking Techniques: Limitations, Attacks and implications, Technical report, IBM Research Report RC 20755, March1997.
S. Craver, Zero Knowledge Watermark Detection, Proceedings of the Third International workship on Information Hiding, Springer Lecture Notes in Computer Science, vol.1768, pp.101–116, 2000.
Joe Killian, F. Thomson Leighton, Lesley R. Matheson, Talal G. Shamoon, Robert E. Tarjan, and Francis Zane, Resistance of Digital Watermarks to Collusive Attacks, Proceedings of the IEEE International Symposium on Information Theory, 1998. 422
Anna Lysyanskaya, Ronald L. Rivest, Amit Sahai, and Stefan Wolf. Pseudonym systems http://theory.lcs.mit.edu/ anna/lrsw99.ps, 1999. 423
N. Memon and P. W. Wong, A Buyer-Seller Watermarking Protocol based on amplitude Modulation and the ElGamal Public Key Cryptosystem, Proceedings of SPIE99, vol3657. 426
N. Memon and P. W. Wong, A Buyer-Seller Watermarking Protocol, IEEE Transactions on image processing, vol.10, no.4, April 2001. 422, 423, 426, 428, 430
B. Pfitzmann and M. Schunter, Asymmetric Fingerprinting, Eurocrypt’96, LNCS 1070, pp.84–95, Springer-Verlag, Berlin 1996. 422, 423, 428
B. Pfitzmann and M. Waidner, Anonymous Fingerprinting, Eurocrypt’97, LNCS 1233, Spring-Verlag, Berlin 1997, 88–102422, 423, 428
B. Pfitzmann and Ahmad-Reza Sadeghi, Coin-Based Anonymous Fingerprinting, Eurocrypt’99, LNCS 1592, Spring-Verlag, Berlin 1996, 150–164. 422, 423
G. Poupard and J. Stern, Fair Encryption of RSA Keys, Enrocrypt2000, LNCS, pp.173–190, Springer-Verlag, 2000. 423, 426
L. Qian and K. Nahrstedt, Watermarking Schemes and Protocols for Protection Rightful Ownership and Customer’s Rights, Academic Press Journal of Visual Communication and Image Representation, 1998. 422, 423
M. Ramkumar and A. N. Akansu, Image Watermarks and Counterfeit Attacks: Some Problems and Solutions, Content Security and Data Hiding in Digital Media, Newark, NJ, May 14, 1999. 421
M. Stadler, Public verifiable secret sharing, Eurocrypt’96, LNCS 1070, pp.191-199, Springer Verlag, 1996. 423, 426
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2003 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Soo Ju, H., Jeong Kim, H., Hoon Lee, D., In Lim, J. (2003). An Anonymous Buyer-Seller Watermarking Protocol with Anonymity Control. In: Lee, P.J., Lim, C.H. (eds) Information Security and Cryptology — ICISC 2002. ICISC 2002. Lecture Notes in Computer Science, vol 2587. Springer, Berlin, Heidelberg. https://doi.org/10.1007/3-540-36552-4_29
Download citation
DOI: https://doi.org/10.1007/3-540-36552-4_29
Published:
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-00716-6
Online ISBN: 978-3-540-36552-5
eBook Packages: Springer Book Archive