Abstract
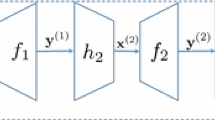
Motivated by the representation of biometric and multimedia objects, we consider the problem of hiding noisy point-sets using a secure sketch. A point-set X consists of s points from a d-dimensional discrete domain [0,N – 1]d. Under permissible noises, for every point \(\left \langle x_1,..,x_d\right \rangle \in X\), each x i may be perturbed by a value of at most δ. In addition, at most t points in X may be replaced by other points in [0,N – 1]d. Given an original X, we want to compute a secure sketch P. A known method constructs the sketch by adding a set of random points R, and the description of (X∪R) serves as part of the sketch. However, the dependencies among the random points are difficult to analyze, and there is no known non-trivial bound on the entropy loss. In this paper, we first give a general method to generate R and show that the entropy loss of (X∪R) is at most s(dlogΔ+ d + 0.443), where Δ= 2δ+1. We next give improved schemes for d = 1, and special cases for d = 2. Such improvements are achieved by pre-rounding, and careful partition of the domains into cells. It is possible to make our sketch short, and avoid using randomness during construction. We also give a method in d = 1 to demonstrate that, using the size of R as the security measure would be misleading.
The original version of this chapter was revised: The copyright line was incorrect. This has been corrected. The Erratum to this chapter is available at DOI: 10.1007/978-3-540-34547-3_36
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
Alon, N., Goldreich, O., Håstad, J., Peralta, R.: Simple constructions of almost k-wise independent random variables. In: Proc. of the 31st FOCS, pp. 544–553 (1990)
Boyen, X.: Reusable cryptographic fuzzy extractors. In: Proceedings of the 11th ACM conference on Computer and Communications Security, pp. 82–91. ACM Press, New York (2004)
Chang, E.-C., Fedyukovych, V., Li, Q.: Secure sketch for multi-set difference. Cryptology ePrint Archive, Report, 2006/090 (2006), http://eprint.iacr.org/
Chang, E.-C., Shen, R., Teo, F.W.: Finding the original point set hidden among chaff. In: ASIACCS 2006 (to appear)
Clancy, T.C., Kiyavash, N., Lin, D.J.: Secure smartcard-based fingerprint authentication. In: ACM Workshop on Biometric Methods and Applications (2003)
Garris, M.D., Michael McCabe, R.: Fingerprint minutiae from latent and matching tenprint images. NIST Special Database 27 (2000)
Dodis, Y., Reyzin, L., Smith, A.: Fuzzy extractors: How to generate strong keys from biometrics and other noisy data. In: Cachin, C., Camenisch, J.L. (eds.) EUROCRYPT 2004. LNCS, vol. 3027, pp. 523–540. Springer, Heidelberg (2004)
Coffman Jr., E.G., Flatto, L., Jelenković, P.: Interval packing: The vacant-interval distribution. The Annals of Applied Probability 10(1), 240–257 (2000)
Juels, A., Sudan, M.: A fuzzy vault scheme. In: IEEE Intl. Symp. on Information Theory (2002)
Juels, A., Wattenberg, M.: A fuzzy commitment scheme. In: Proc. ACM Conf. on Computer and Communications Security, pp. 28–36 (1999)
Maltoni, D., Maio, D., Jain, A.K., Prabhakar, S.: Handbook of Fingerprint Recognition. Springer, Heidelberg (2003)
Minsky, Y., Trachtenberg, A., Zippel, R.: Set reconciliation with nearly optimal communications complexity. In: ISIT (2001)
Palasti, I.: On some random space filling problems. Publ. Math. Inst. Hung. Acad. Sci. 5, 353–359 (1960)
Rényi, A.: On a one-dimensional problem concerning random space-filling. Publ. Math. Inst. Hung. Acad. Sci. 3, 109–127 (1958)
Tuyls, P., Goseling, J.: Capacity and examples of template-protecting biometric authentication systems. In: ECCV Workshop BioAW, pp. 158–170 (2004)
Yang, S., Verbauwhede, I.: Automatic secure fingerprint verification system based on fuzzy vault scheme. In: IEEE Intl. Conf. on Acoustics, Speech, and Signal Processing (ICASSP), pp. 609–612 (2005)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2006 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Chang, EC., Li, Q. (2006). Hiding Secret Points Amidst Chaff. In: Vaudenay, S. (eds) Advances in Cryptology - EUROCRYPT 2006. EUROCRYPT 2006. Lecture Notes in Computer Science, vol 4004. Springer, Berlin, Heidelberg. https://doi.org/10.1007/11761679_5
Download citation
DOI: https://doi.org/10.1007/11761679_5
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-34546-6
Online ISBN: 978-3-540-34547-3
eBook Packages: Computer ScienceComputer Science (R0)