Abstract
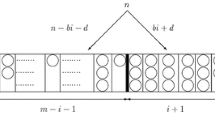
A quadratic search method for hash tables whose size is a power of 2 is presented. It allows full table searching, and yet eliminates secondary clustering, which occurs when different keys hashed initially to the same location proceed to trace through the same sequence of locations. Comparisons with other methods are made experimentally.
Article PDF
Similar content being viewed by others
Avoid common mistakes on your manuscript.
References
W. D. Maurer, “An improved hash code for scatter storage,”Comm. ACM 11(1):35–38 (1968).
C. E. Radke, “The use of quadratic residue research,”Comm. ACM 13(2):103–105 (1970).
J. R. Bell, “The quadratic quotient method: a hash code eliminating secondary clustering,”Comm. ACM 13(2):107–109 (1970).
F. R. A. Hopgood and J. Davenport, “The quadratic hash method when the table size is a power of 2,”Comput. J. 15(4):314–315 (1972).
R. Morris, “Scatter storage techniques,”Comm. ACM 11(1):38–43 (1968).
Author information
Authors and Affiliations
Rights and permissions
About this article
Cite this article
Nishihara, S., Hagiwara, H. A full table quadratic search method eliminating secondary clustering. International Journal of Computer and Information Sciences 3, 123–128 (1974). https://doi.org/10.1007/BF00976638
Received:
Revised:
Issue Date:
DOI: https://doi.org/10.1007/BF00976638