Abstract
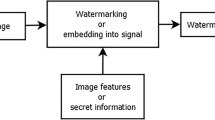
Image authentication is the technology of verifying image origin, integrity and authenticity. A rich stream of research on image authentication has shown various trade-off among four favorable features, namely robustness, security, versatility and efficiency. Image data authentication has the highest level of security but provides no robustness/versatility. Image content authentication from robust hashing keeps robust to limited types of operations, and as a result its versatility is not satisfactory. Existing designs of image content authentication from advanced cryptographic primitives achieve robustness, security and versatility, at the cost of low efficiency. In this paper, we present a new design of image authentication with an improved trade-off among the aforementioned features. Our versatile design is robust to a number of predefined image processing operations. Its security can be reduced to q-strong Diffie-Hellman (q-SDH), a complexity problem used by existing cryptographic algorithms. From the aspect of efficiency, the new design has a constant-size authentication overhead (⩽ 2 kB) and a constant verification time (around 0.05 s). While the time of generating authentication overhead increases linearly with the number of permissible editing operations, it only takes around 0.33 s for 1000 types of permissible operations. We believe the new design will facilitate image applications where trustworthy image editing is required.
Article PDF
Similar content being viewed by others
Avoid common mistakes on your manuscript.
References
Zhang H G, Han W B, Lai X J, et al. Survey on cyberspace security. Sci China Inf Sci, 2015, 58: 110101
Du L, Cao X C, Zhang W, et al. Semi-fragile watermarking for image authentication based on compressive sensing. Sci China Inf Sci, 2016, 59: 059104
Friedman G L. The trustworthy digital camera: restoring credibility to the photographic image. IEEE Trans Consumer Electron, 1993, 39: 905–910
Merkle R C. A digital signature based on a conventional encryption function. In: Proceedings of Conference on the Theory and Applications of Cryptographic Techniques, Santa Barbara, 1987. 369–378
Venkatesan R, Koon S, Jakubowski M H, et al. Robust image hashing. In: Proceedings of the 2000 International Conference on Image Processing, Vancouver, 2000. 664–666
Monga V, Evans B L. Perceptual image hashing via feature points: performance evaluation and tradeoffs. IEEE Trans Image Process, 2006, 15: 3452–3465
Xiang S J, Yang J Q, Huang J W. Perceptual video hashing robust against geometric distortions. Sci China Inf Sci, 2012, 55: 1520–1527
Huang F J, Huang J W. Calibration based universal JPEG steganalysis. Sci China Ser F-Inf Sci, 2009, 52: 260–268
Lin C-Y, Chang S-F. A robust image authentication method distinguishing JPEG compression from malicious manipulation. IEEE Trans Circ Syst Video Technol, 2001, 11: 153–168
Tang Z, Zhang X, Li X, et al. Robust image hashing with ring partition and invariant vector distance. IEEE Trans Inform Forensic Secur, 2016, 11: 200–214
Kim J, Lee S, Yoon J, et al. PASS: privacy aware secure signature scheme for surveillance systems. In: Proceedings of the 14th IEEE International Conference on Advanced Video and Signal Based Surveillance, Lecce, 2017. 1–6
Chen H, Wang S, Zhang H, et al. Image authentication for permissible cropping. In: Proceedings of the 14th International Conference on Information Security and Cryptology, Fuzhou, 2018. 308–325
Naveh A, Tromer E. Photoproof: cryptographic image authentication for any set of permissible transformations. In: Proceedings of IEEE Symposium on Security and Privacy, San Jose, 2016. 255–271
Ben-Sasson E, Chiesa A, Tromer E, et al. Succinct non-interactive arguments for a von neumann architecture. IACR Cryptol ePrint Archive, 2013, 2013: 879
Katz J, Lindell Y. Introduction to Modern Cryptography. 2nd ed. Boca Raton: CRC Press, 2014
Merkle R C. A certified digital signature. In: Proceedings of the 9th Annual International Cryptology Conference, Santa Barbara, 1989. 218–238
Xie L H, Arce G R, Graveman R F. Approximate image message authentication codes. IEEE Trans Multimedia, 2001, 3: 242–252
Tang Z, Zhang X, Huang L, et al. Robust image hashing using ring-based entropies. Signal Process, 2013, 93: 2061–2069
Xiang S, Kim H, Huang J. Histogram-based image hashing scheme robust against geometric deformations. In: Proceedings of the 9th Workshop on Multimedia & Security, Dallas, 2007. 121–128
Choi Y S, Park J H. Image hash generation method using hierarchical histogram. Multimed Tools Appl, 2012, 61: 181–194
Tang Z, Dai Y, Zhang X, et al. Perceptual image hashing with histogram of color vector angles. In: Proceedings of the 8th International Conference Active Media Technology, Macau, 2012. 237–246
Gharde N D, Thounaojam D M, Soni B, et al. Robust perceptual image hashing using fuzzy color histogram. Multimed Tools Appl, 2018, 77: 30815–30840
Lou D-C, Liu J-L. Fault resilient and compression tolerant digital signature for image authentication. IEEE Trans Consumer Electron, 2000, 46: 31–39
Sun Q, Chang S F. A robust and secure media signature scheme for JPEG images. J VLSI Sign Process Syst Sign Image Video Technol, 2005, 41: 305–317
Kee E, Johnson M K, Farid H. Digital image authentication from JPEG headers. IEEE Trans Inform Forensic Secur, 2011, 6: 1066–1075
Iida K, Kiya H. Robust image identification for double-compressed and resized JPEG images. In: Proceedings of Asia-Pacific Signal and Information Processing Association Annual Summit and Conference, Honolulu, 2018. 1968–1974
Yao H, Wei H, Qin C, et al. An improved first quantization matrix estimation for nonaligned double compressed JPEG images. Signal Process, 2020, 170: 107430
Lei Y, Wang Y, Huang J W. Robust image hash in Radon transform domain for authentication. Signal Process-Image Commun, 2011, 26: 280–288
Tang Z, Ling M, Yao H, et al. Robust image hashing via random Gabor filtering and DWT. Comput Materials Continua, 2018, 55: 331–344
Hu Y C, Lo C C, Chen W L. Probability-based reversible image authentication scheme for image demosaicking. Future Generation Comput Syst, 2016, 62: 92–103
Davarzani R, Mozaffari S, Yaghmaie K. Perceptual image hashing using center-symmetric local binary patterns. Multimed Tools Appl, 2016, 75: 4639–4667
Swaminathan A, Mao Y, Wu M. Image hashing resilient to geometric and filtering operations. In: Proceedings of IEEE 6th Workshop on Multimedia Signal Processing, 2004. 355–358
Swaminathan A, Mao Y, Wu M. Robust and secure image hashing. IEEE Trans Inform Forensic Secur, 2006, 1: 215–230
Rackoff C, Simon D R. Non-interactive zero-knowledge proof of knowledge and chosen ciphertext attack. In: Proceedings of the 11th Annual International Cryptology Conference, Santa Barbara, 1991. 433–444
Krawczyk H, Rabin T. Chameleon hashing and signatures. IACR Cryptol ePrint Archive, 1998, 1998: 10
Chen X, Zhang F, Susilo W, et al. Identity-based chameleon hashing and signatures without key exposure. Inf Sci, 2014, 265: 198–210
Chen X, Zhang F, Kim K. Chameleon hashing without key exposure. In: Proceedings of the 7th International Conference Information Security, Palo Alto, 2004. 87–98
Ateniese G, de Medeiros B. On the key exposure problem in chameleon hashes. In: Proceedings of the 4th International Conference on Security in Communication Networks, Amalfi, 2004. 165–179
Bellare M. A note on negligible functions. IACR Cryptology ePrint Archive, 1997, 1997: 4
Pointcheval D, Stern J. Security proofs for signature schemes. In: Proceedings of International Conference on the Theory and Application of Cryptographic Techniques, Saragossa, 1996. 387–398
Boneh D, Lynn B, Shacham H. Short signatures from the Weil Pairing. In: Proceedings of the 7th International Conference on the Theory and Application of Cryptology and Information Security, Gold Coast, 2001. 514–532
Mitsunari S, Sakai R, Kasahara M. A new traitor tracing. IEICE Trans Fundamentals Electron Commun Comput Sci, 2002, 85: 481–484
Boneh D, Boyen X. Short signatures without random oracles. In: Proceedings of International Conference on the Theory and Applications of Cryptographic Techniques, Interlaken, 2004. 56–73
You J, Reiter U, Hannuksela M M, et al. Perceptual-based quality assessment for audio-visual services: a survey. Signal Process-Image Commun, 2010, 25: 482–501
Zhai G T, Min X K. Perceptual image quality assessment: a survey. Sci China Inf Sci, 2020, 63: 211301
Nguyen L. Accumulators from bilinear pairings and applications. In: Proceedings of Cryptographers’ Track at the RSA Conference, San Francisco, 2005. 275–292
Baric N, Pfitzmann B. Collision-free accumulators and fail-stop signature schemes without trees. In: Proceedings of International Conference on the Theory and Application of Cryptographic Techniques, Konstanz, 1997. 480–494
Guo F, Susilo W, Mu Y. Introduction to Security Reduction. Berlin: Springer, 2018
Acknowledgements
This work was supported by National Natural Science Foundation of China (Grant Nos. 61902070, 61822202, 62032005, 61872089, 61872087).
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Chen, H., Huang, X., Wu, W. et al. Efficient and secure image authentication with robustness and versatility. Sci. China Inf. Sci. 63, 222301 (2020). https://doi.org/10.1007/s11432-020-3007-5
Received:
Revised:
Accepted:
Published:
DOI: https://doi.org/10.1007/s11432-020-3007-5