Abstract
To evaluate the performance of cognitive radio (CR) under the energy detection scheme, the proper selection of threshold is an important and a critical task. The threshold is generally selected, either under a target probability of detection \((\overline{P_d})\) called as the constant detection rate (CDR) principle, or under the target probability of false alarm \((\overline{P_{fa}})\), called as the constant false alarm rate (CFAR) principle. To ensure sufficient protection to the licensed users (or primary users), the selection of threshold under the CDR principle is best suited. This paper discusses and analyzes the inefficiency of CR under the blind use of CDR principle, mainly, when primary receiver is located at a sufficient distance d from the secondary transmitter where signal to interference plus noise ratio (SINR) is larger than a cut-off value \(SINR_{th}\) (which is a minimum SINR required to properly decode the intended information of primary user). To overcome this inefficiency, we propose an approach which while considering distance d between the secondary transmitter and primary receiver as an important parameter, makes an interference-aware selection of threshold based on the CDR and CFAR principles. Under the proposed approach, the CR system achieves a significant gain in its throughput even under the low signal to noise ratio conditions.
Similar content being viewed by others
Explore related subjects
Discover the latest articles, news and stories from top researchers in related subjects.Avoid common mistakes on your manuscript.
1 Introduction
The high rate transition of wireless communication from wireless telephony to the interactive internet services and multimedia services has led to the increased demand of high data rates [1–3]. To accommodate the high data rate applications and large number of wireless communication devices within the limited available spectrum is a difficult and a challenging task, and this gives rise to the spectrum scarcity [1, 4]. In addition to this, the fixed spectrum allocation policies have led the spectrum scarcity problem to its peak [5, 6]. However, measurements carried out by the federal communications commission (FCC) have revealed that the licensed spectrum in most part of the world is underutilized for most of the time, and this gives birth to the concept of cognitive radio (CR) [7].
The CR is a concept that allows unlicensed users to temporarily use that portion of the licensed spectrum which is not being used by the licensed users [1, 2, 8]. However, the spectrum reuse must be performed in a manner which does not cause any harm to an ongoing communication of the licensed users [1, 2, 4]. In the cognitive scenario, the authors authorized to use the licensed band are generally called as licensed or primary users (PUs) while the unauthorized users are called as unlicensed or secondary users (SUs). Under the energy detection scheme, the performance of CR system is evaluated with the help of two important parameters namely probability of false alarm \(P_{fa} \) and probability of detection \(P_d \). The \(P_{fa} \) is the probability with which an idle band is detected as busy while \(P_d \) denotes the probability with which a busy band is detected as busy. The low \(P_{fa} \) is required to maximize the licensed channel utilization while high \(P_d \) is necessary to ensure sufficient level of protection to the PUs. So, for an efficient CR system, the values of \(P_{fa} \) and \(P_d \) must be low and high, respectively [3, 5, 9]. To maximize the utilization of licensed spectrum while ensuring a sufficient level of protection to the PUs, the spectrum sensing (SS) is a very important component [10]. There are many sensing techniques which are broadly classified as, energy detection [4, 5, 9, 11, 12] cyclostationary feature detection [13] and matched filter detection [14], etc. However, out of all these sensing techniques, energy detection is the only technique which works independently without requiring any prior information (i.e. signal characteristics) of PU signal, also, it is simple and involves low computational complexities [10, 15]. Under the energy detection scheme, the received energy is compared with a pre-decided reference threshold \(\lambda \) and based on this comparison the status (active/idle) of the frequency band is decided [4, 5, 9, 11]. The performance of CR majorly depends on the value of detection threshold, therefore the proper selection of it is a critical task [16, 17]. In the CR system, the threshold selection is generally made with the help of constant detection rate (CDR) or constant false alarm rate (CFAR) principle [17–21]. Under CDR principle, the CR aims to decrease its false alarm probability (or indirectly, increase its achievable throughput) with the constraints to maintain its \(P_d \) to a target value \(\overline{P_d}\), while, under CFAR principle it aims to improve its detection probability with the constraints to maintain its \(P_{fa} \) value to \(\overline{P_{fa}}\) [17, 18]. However, from the PU point of view, to ensure sufficient level of protection to the PUs, the selection of threshold under the CDR principle is most favorable (even under the low signal to noise ratio—SNR conditions), while, from the SU’s perspective, to improve the licensed channel utilization, the selection of threshold under the CFAR principle has an edge over the CDR principle [17, 20]. So, based on the system preferences (whether to ensure high protection to PU or facilitate high throughput to CR user), the selection of threshold is made accordingly. However, some of the research works have considered the static detection threshold, calculated independent of CDR or CFAR principle (as in [19]). In [22], the authors designed an experimental set-up and based on the performed measurements on noise power, the threshold is set. In [23], Moghimi et al. while working under the non-Gaussian noise conditions attempted to minimize its false alarm probability under the constraints to maintain a constant detection probability of \(\overline{P_d}\). In [24], to improve the utilization of licensed spectrum, the authors worked under the spectrum sharing scheme while setting a target of maintaining \(P_d \) to a constant value \(\overline{P_d}\). In [9], Liang et al. first formulated the sensing-throughput tradeoff problem and then optimized the sensing time (under the CDR principle) in a manner which maximizes the achievable throughput of the CR user. The authors in [4, 24] proposed a novel frame and decoder structures under which the CR operates beyond any sensing-throughput tradeoff problem, however, the proposed approach was bounded to ensure a minimum level of protection \(\overline{P_d}\) to the licensed users. Verma and Sahu [25], while operating under the CDR principle weighted the contribution of [4, 24] by designing an optimal frame duration where the achievable throughput of CR system is maximized. The authors in [26, 27] exploited the cooperation of PUs (under the CDR principle) to improve the sensing efficiency and throughput of proposed CR system of [4, 24]. The authors in [4, 5, 9, 28, 29] also worked under the CDR principle with a common aim to improve achievable throughput of the CR user.
In [30], Dubey and Verma while exploiting the advantages of the CFAR principle proposed an adaptive threshold which significantly enhances the sensing efficiency of the CR system. The authors in [31] chose threshold under the CFAR principle where they studied and developed a model for the signal uncertainty, they further analyzed the CR throughput under the presence and absence of noise uncertainty. The authors in [17, 19, 32–35] also considered selection of threshold under the CFAR principle while working with a common motto to improve protection of PUs.
In this paper, through the analysis performed we first show that: the CR system operating under the blind use of CDR principle results in an overprotection of PU, mainly, when CR is located at a sufficient distance d from the PU where received SINR (as received by the primary receiver) is higher than its tolerable SINR threshold \(SINR_{th} \). Such an overprotection approach results in an undesirable degradation to achievable throughput of CR user even under the good spectrum reuse conditions (analyzed and explained in Sects. 3, 4).
In the cognitive literature many related works have also been done where distance between primary and secondary user has been used as an important variable. In [16], the authors proposed a novel method which uses the distance between PU and SU as an important parameter to determine the detection threshold. In this paper, the SU first decides its transmission power based on the distance information and then using it, the selection of threshold is made. The authors in [34] considered the distance information between PU and SU to control the transmission power of SU so that an undesirable interference can be prevented. A heuristic algorithm has been proposed in [36] which exploit additional information about PU, such as related to frequency allocation and its geo-location. The idea of algorithm is to autonomously determine the detection threshold based on the relative position of SU with the base station. In [28], the authors proposed a new metric “probability of interference \(P_I \)” which considers the distance between secondary transmitter and primary receiver as an important entity to improve the licensed channel utilization. The authors in [29, 37] extended the work of [28] to further enhance its achievable throughput.
However, it is a challenging task to know the distance between PU and SU, but with the advancement to signal processing techniques, this has been quiet possible. In [38], the authors used the extended Kalman filter to localize the primary user and estimate its transmission power. A received signal strength (RSS) method has been used in [39] to estimate the location and effective radiated isotropic power of primary transmitter. The investigations in [40] use a generic path loss model and auxiliary network of sensors to determine the location of transmitting nodes in the cellular network. There are many similar works as in [41, 42] which attempts to estimate the distance and radiated power of a transmitting node.
In this paper we attempt to overcome the inefficiency of CDR principle mainly for the case where \(SINR>SINR_{th}\). Because for this case, considering the worst situation, even if a missed detection occurs at the SU end, the PU can still operate and decode its desired information properly.
To do so, we formulate the distance d of secondary transmitter from the primary receiver where \(SINR=SINR_{th} \), such a distance can be called as critical distanceFootnote 1 \(d_c \). For a distance \(d\le d_c \), the SINR received at the primary receiver end is less than (or equal to) the minimum decodable SINR value (i.e. \(SINR\le SINR_{th})\), in this scenario, if a missed detection occurs, the PU communication can badly be interfered. While for the case when \(d>d_c \), since \(SINR>SINR_{th} \), so, even for a case of missed detection the SU can still operate without causing any significant loss to an ongoing communication of the PU.
So, motivated with this fact, we propose an intelligent selection of detection threshold as follows:
Initially, when a CR wants to communicate, it is not sure about how much close it is located to the primary receiver.
So, with an aim to ensure sufficient level of protection to the PUs, the CR system operates while selecting threshold under the CDR principle (elaborated through the flowchart in Fig. 6.). During the communication, whenever the concerned channel is detected as busy, the CR does not blindly assumes it as busy instead it looks for the case under which for a large distance d the channel is falsely detected as busy. To do so, it first locates the primary transmitter using any of the approaches as explained in [38–40, 42] and then computes its distance d from the primary receiver (elaborated in Sect. 4). If, the condition \(d\le d_c \) exists then the channel is assumed as busy and communication is stopped from the concerned channel. But for the other case \(d>d_c \) where even under the case of missed detection the PU data is still decodable, the threshold is selected under the CFAR principle.
In this manner, the proposed system harnesses the benefits from both, the CDR and the CFAR principles and improves the achievable throughput of CR user while ensuring sufficient protection required to the PU system.
Moreover, the computation of critical distance \(d_c \) and the estimation of distance d is done only once when the CR (operating under the CDR principle) shows the status of concerned channel as busy. So, it introduces the minimum possible complexity to the CR system.
The rest of the paper is organized as follows: Sect. 2 presents the overview of energy detection scheme based CR system. Section 3 analyzes and discusses the inefficiency of CR system under the CDR principle, mainly when a PU is located far away from the sensing node where \(SINR>SINR_{th} \) . Section 4 formulates the critical distance based on which the intelligent selection of detection threshold is proposed. Section 5 discusses the obtained simulation results, and finally, the article is concluded in Sect. 6.
2 The overview of energy detection scheme
Under the energy detection scheme, the presence and absence of PU on a frequency band of interest can be represented by the following hypothesis \(H_1 \) and \(H_0 \) as follows [4, 5, 9]:
where, s(n) and u(n) are the PU and the noise signals which are assumed to be independent and identically distributed (i.i.d.) with their mean value of zero and variances of \(\sigma _p^{2}\) and \(\sigma _u^{2}\), respectively. y(n) is the overall signal as received by the sensing node.
The test statistic for the energy detection scheme can be written as [9, 11, 15]:
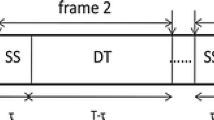
where, N is the number of samples collected at the sensing node and is represented as \(N=\tau f_s, \tau \) denotes the sensing time out of a given frame of T units (Fig. 1) and \(f_s \) is the sampling frequency of the received signal. For a given detection threshold \(\lambda \), the probability of detection \(P_d \) and false alarm \(P_{fa} \) can be written as:
where, \(p_1 (x)\) and \(p_0 (x)\) denotes the probability density function (PDF) of the test statistic \(\pounds (y)\) under the hypothesis \(H_1 \) and \(H_0 \), respectively.
Under the circularly symmetric complex Gaussian (CSCG) PU signal and noise case, the \(P_d \) and \(P_{fa} \) can be written as [4, 5, 9, 24–27]:
where, Q(.) denotes the complementary distribution function of the standard Gaussian signal and can be represented as [9]:
and, \(SNR_P \) represents the SNR of PU signal received at the sensing node and is given by:
\(P_p (=\sigma _p^{2})\) is the power of primary signal received by the sensing node.
From the PU perspective, higher the value of \(P_d \), the better protection is assured to the PU and from the SU perspective, lower the value of \(P_{fa} \), the higher are the chances to increase the licensed spectrum utilization. So, for a good CR system, the values of \(\hbox {P}_\mathrm{d} \) and \(\hbox {P}_{\mathrm{fa}} \) must be high and low respectively, as much as possible.
As can be seen from (6) and (7), under the given values of \(\sigma _u^{2}, SNR_p \) and N, the \(P_d \) and \(P_{fa} \) mainly depends on the threshold \(\lambda \). So, proper selection of \(\lambda \) is a critical factor to determine the performance of CR system.
Under the CDR principle, for a given \(\overline{P_d}\), the values of \(\lambda (=\lambda _d)\) and \(P_{fa} (=P_{fa,CDR})\) can be given as (from Eqs. (6), (7)):
and
In the same manner, under the CFAR principle, for a given \(\overline{P_{fa}}\), the values of \(\lambda (=\lambda _{fa})\) and \(P_d (=P_{d,CFAR})\) can be given as (from Eqs. (6), (7)):
and
3 The analysis of inefficiency of CR system under the CDR principle
Out of a given frame duration of T units (Fig. 1), the CR first senses the spectrum for \(\tau \) units and based on the sensing decision (active/idle) the further action is taken. If the channel is sensed to be idle, it is accessed by the SU for its communication, otherwise a new channel search is initiated to find the next idle channel.
The instantaneous transmission rates for the CR system can be written as follows [5, 9, 25]:
where, \(C_{00} \) is the transmission rate when an idle channel was detected as idle and \(C_{01} \) is the transmission rate when a busy channel was detected as idle and \(P_{rs} \) & \(SNR_s \) denotes the power and SNR of the SU received at its receiving end. Under the CDR principle, the achievable throughput of SU can finally be written as (using (11), (14), (15)):
where, \(P({H_0})\) and \(P({H_1})\) denotes the actual probabilities with which a target channel is idle and busy respectively.
Under low SNR regime, assuming \(2SNR_p +1\approx 1\), the equation in (6) can be written as:
the assumption \(2SNR_p +1\approx 1\) has only been introduced to bring simplicity and clarity to derived equation in (23) which is only intended to show the variation of \(P_{fa,CDR} \) with distance d. However, even if this assumption is not considered, the relation between distance d and \(P_{fa,CDR} \) remains unchanged (only representation of equation shall appear complex without disturbing its meaning).
From (17), under the CDR principle, assuming a target detection probability of \(\overline{P_d}\), the value of \(\lambda (=\lambda _d)\) can be written as:
From (18), the false alarm probability \(P_{fa,CDR}\) in terms of \(\overline{P_d}\) can be expressed as (from (7), (18)):
The transmitted power of the PU received at the sensing node which is located at a distance \(d_{ps} \) apart can be modeled as follows [43]:
where, \(P_p \) is the power transmitted from the PU, \(d_{ps} \) is the distance between primary transmitter and the sensing node, \(P_{rps}\) denotes the power from the primary transmitter as received by the SU, \(d_0 \) is the reference distance chosen, \(K_{ps} \) is a constant that depends on the antenna characteristics and free space path loss up to a distance \(d_0 \) and r denote the path loss exponent.
In Eq. (20), the terms \(K_{ps} \) and \(d_0^{r}\) constitutes the constants terms, so this equation can be re-written as:
where \(c=K_{ps} . d_0^{r}\).
From Eqs. (9) and (21), the \(SNR_p \) can be written as:
Now, from Eqs. (19) and (22) we have:
Under the given values of \(\overline{P_d}, N, \sigma _u^{2}, P_p, c\) and r, from Eq. (23), the Fact 1 can be deduced as:
Fact 1: Under the CDR principle, the false alarm probability \(P_{fa,CDR} \) varies in direct proportion to the distance \(d_{ps} \) (Fig. 2), or in other words, as the PU moves away from the SU, the false alarm probability increasesFootnote 2, and vice-versa.
From Eq. (16) it is also clear that, with the increase in false alarm probability the achievable throughput C decreases, so the Eq. (16) in combination to Eq. (23) deduces the Fact 2 as follows:
Fact 2: Under the CDR principle, as the PU moves away from the SU, the achievable throughput of SU decreases (Fig. 3), and vice-versa.
Based on the analysis performed we strongly argue that, in the conditions when SU is located at sufficiently large distance from the PU where \(SINR>SINR_{th} \) and the licensed spectrum can be exploited to its maximum, the CR system operating under the CDR principle becomes over-protective which results in an undesirable loss to its achievable throughput.
In this manner, under the CDR principle, the CR system looses the best spectrum utilization opportunities and proves to be inefficient.
4 The proposed intelligent selection of detection threshold
In this paper we consider a network scenario with one primary transmitter which serves as the base station of a cellular network or a TV broadcast station with its service range of R (Fig. 4).
During missed detection, the power of secondary signal received at the primary receiver end can be modeled as (from (21)):
where, \(P_s \) is the transmission power of SU, d is the distance between secondary transmitter and primary receiver under the worst condition, \(P_{rsp} \) denotes the received power at the primary receiver, r is the path loss exponent of the path between the secondary transmitter and the primary receiver and \(\alpha \) is the constant.
Under the case of missed detection, the SINR of primary receiver which is located on the cell boundary closest to the secondary transmitter, as shown in Fig. 4 (i.e., the receiver with worst SINR if SU transmits) can be denoted as:
where, \(P_{rpp} \) is the power of the PU received at its receiving end, and can be represented as:
where \(P_p \) is the power transmitted from the primary transmitter, R is the service range of the primary network, r is the path loss exponent between the primary transmitter and primary receiver and \(\beta \) is the constant term.
From Eqs. (24) and (26), the Eq. (25) can be re-written as:
as it is a established fact that, under the conditions of missed detection, the intended information can only be decoded by the PU if and only if \(SINR>SINR_{th} \), or in other words, \(SINR_n =\frac{SINR}{SINR_{th}}>1\), where \(SINR_n \) is the normalized SINR and \(SINR_{th} \) is the minimum value of SINR required by the primary receiver to successfully decode its intended information (i.e., with a desirable bit error rate probability).
In Eq. (27), under the known values of \(\alpha , \beta , P_p, P_s\) and noise, the value of SINR depends mainly on the distance between secondary transmitter and primary receiver d.
Assuming the marginal condition of \(SINR_n =1\) (as shown in Fig. 5) which can only be achieved at a certain distance \(d(=d_c)\), the Eq. (27) can be re-written as:
finally, from Eq. (28), the critical distance \(d_c \) can be written as (also depicted through Fig. 5):
Now, based on the flowchart of Fig. 6, we propose the intelligent selection of detection threshold as follows:
In the start of communication, since a CR is unaware of its distance d from the primary receiver, so with an aim to ensure sufficient protection to the PUs, the CR starts its communication while selecting threshold under the CDR principle. During its sensing phase, if the channel is detected as busy, then in place of blindly assuming it as busy the CR tries to search for the other case under which the channel can undesirably appear as busy. This generally happens when a CR is located at a large distance from the PU. In such a scenario, in order to ensure the target level of protection to the PUs, the CR system undesirably treats system noise as the PU signal which increases the false alarm probability (Fig. 2) and the channel is falsely detected as busy. To overcome this situation, the CR first locatesFootnote 3 the primary transmitter using any of the approaches as proposed in [38–40, 42]. Knowing the distance\(^{3}\) \(d_{ps} \) between the secondary and primary transmitters, the distance d between the secondary transmitter and the primary receiver can further be computed as:
where, R is the service range of the primary network which is already known to the CR user. Finally, if the distance d is less than or equal to the critical distance \(d_c \) then the concerned channel is assumed as busy and CR search for another idle channel. While, for the case when distance d is higher than the critical distance \(d_c \), in such a scenario the CR attempts to maximum utilize the licensed channel, so it communicate using the CFAR principle.
In this manner the CR makes a novel effort to maximum utilize the licensed spectrum by exploiting the CDR and CFAR principles, opportunistically. Moreover, the proposed CR system efficiently improves the throughput of CR system mainly in the low SNR regime where it is a real challenge to do so.
5 Results and analysis
As illustrated in Sect. 1, the noise and primary signals are considered to be CSCG. Here are the following assumed parameters: Target frequency band= 60 MHz, Frame duration \(T=100\,\hbox {msec}\), Sensing time \(\tau =14\,\hbox {msec}\), the probability with which a target band is idle \(P({H_0})=0.8\), Power transmitted from the SU \(P_s = 0.1\,\hbox {watt}\), transmitted power from the PU \(P_p = 1\,\hbox {watt}\), the service range R of the primary network= 450 m, the transmitting and receiving antenna gains are chosen to be unity, the \(SINR_{th}\) is set to 8 dB which is the minimum threshold used for BPSK demodulation with a bit error rate of \(2e-4\), and the reference distance \(d_o \) is set to be 10 m. The graph in Fig. 7 shows the variation of CR throughput with the distance d of secondary transmitter from the primary receiver. It is shown that, below the critical distance \(d_c \) (as marked) the throughput of CR under the blind use of CDR principle and proposed approach is same. But, as the distance goes beyond \(d_c \), the throughput of CR under the blind use of CDR principle gets outperformed by the proposed approach. This variation in performance of CR is observed because, beyond \(d_c \), the CR system operating under the proposed approach exploits the best spectrum reuse opportunities (mainly in the low SNR region where accessing of licensed spectrum is a real challenge) but it fails to do so while operating under the blind use of CDR principle. The estimation of critical distance \(d_c \) has significant importance in the implementation of the proposed approach. However, even if \(d_c \) is not estimated properly, the CR under the proposed approach still achieves high value of throughput than it is achieved when CR is operated under the blind use of CDR principle. This is well illustrated through the simulation graph in Figs. 8 and 9.
The graph in Fig. 10 illustrates that, as the distance between secondary transmitter-primary receiver goes beyond \(d_c \), the false alarm probability \(P_{fa} \) under the blind use of CDR principle increases sharply which results in a continuous decrement to the spectrum reusability. While, under the proposed approach, the \(P_{fa} \) maintains a low and a constant value (however, value of \(P_{fa} \) is set according to the designed regulation policies). From the figure it can be concluded that, the proposed approach efficiently harnesses the spectrum reusability condition which improve the throughput of CR system.
The Fig. 11 plots throughput of CR system with the distance d under various values of path loss exponent r. It is illustrated that, with the increase in r, the loss in the path between secondary transmitter and primary receiver increases which further improves opportunity to efficiently utilize the licensed spectrum. Under the proposed approach, the CR exploits this fact to enhance its achievable throughput while under the blind use of CDR principle it misses to do so.
6 Conclusion
This article first studies and analyzes the efficiency of cognitive radio under the CDR principle. Based on the analysis we argue that, the CR operating under the CDR principle undesirably faces the throughput loss even under the good spectrum reusability conditions, mainly when primary user is located at sufficient distance from secondary user where chances of interference to it are negligible. To overcome this inefficiency, we propose a cognitive radio system which exploits the advantages of CDR and CFAR principles opportunistically and improves the throughput of CR system, mainly in the low SNR regime (which is a real challenge). The simulation results suggest that, with the increase in path loss between the primary user and the sensing node, the spectrum reusability increases. The proposed approach efficiently exploits the channel conditions which improves the throughput of cognitive radio system, while blind use of CDR principle fails to do so. The simulation results provided well justifies the proposed approach. In future work, with an idea to improve robustness of the proposed CR system under the shadowing and fading effects of wireless communication channel, we further plan to extend it to the cooperation of more than one cognitive user.
Notes
Based on the settings of various parameters assumed (assumptions are given in Sect. 5), the value of critical distance \(d_c\) may vary.
As per the properties of the Q function Q(x), it shows sharp variation for a given range of x, as \(x\epsilon ({-4, 4})\), however, beyond this range, the variations are negligible. So, this results in an un-noticeable variation to the achieved simulation curves (for some range of variable on x-axis), as depicted in Figs. 2 and 3.
During sensing, the distance between the secondary transmitter and primary transmitter (\(d_{ps}\)) may also be computed as follows: The term \(P_{rps}\) in Eq. (21) shows the power of primary transmitter received at the sensing node (i.e. secondary transmitter). Since, the values \(P_{rps}\), \(P_p\), r and the constant c are already known at the CR end, the distance \(d_{ps}\) can be computed as:
$$\begin{aligned} d_{ps} =exp\left( {\frac{1}{r}.ln\left( {c.\frac{P_p}{P_{rps}}} \right) } \right) \end{aligned}$$
References
Mitola, J., & Maguire, G. Q. (1999). Cognitive radio: Making software radio more personal. IEEE Personal Communications, 6(4), 13–18.
Mitola, J. (2000). Cognitive radio: An integrated agent architecture for software defined radio. PhD. Dissertation, Royal Institute of Technology (KTH), Stockholm.
Ghasemi, A., et al. (2007). Fundamental limits of spectrum-sharing in fading environments. IEEE Transactions on Wireless Communications, 6(2), 649–658.
Pandit, S., & Singh, G. (2013). Throughput maximization with reduced data loss rate in cognitive radio network. Telecommunication Systems, 57, 209–215. doi:10.1007/s11235-013-9858-z.
Stotas, S., & Nallanathan, A. (2011). Optimal sensing time and power allocation in multiband cognitive radio networks. IEEE Transactions On Communications, 59(1), 226–235.
Kaur, P., Uddin, M., & Khosla, A. (2012). Throughput analysis for opportunistic spectrum access among unlicensed devices. In National conference on communications (NCC) (pp. 1–5). doi:10.1109/NCC.2012.6176818.
Federal Communications Commission. (Nov. 2002). Spectrum policy task force report. FCC 02–155.
Haykin, S. (2005). Cognitive radio: brain-empowered wireless communications. IEEE Journal on Selected Areas in Communications, 23, 201–220.
Liang, Y.-C., et al. (2008). Sensing-throughput tradeoff for cognitive radio networks. IEEE Transactions on Wireless Communications, 7(4), 1326–1336.
Altrad, O., et al. (2014). Opportunistic spectrum access in cognitive radio networks under imperfect spectrum sensing. IEEE Transactions on Vehicular Technology, 63(2), 920–925.
Digham, F., et al. (2007). On the energy detection of unknown signal over fading channels. IEEE Transactions on Communications., 55(1), 21–24.
Altrad, O., & Muhaidat, S. (2013). A new mathematical analysis of the probability of detection in cognitive radio over fading channels. EURASIP Journal on Wireless Communications and Networking, 2013, 1–11.
Du, K. L., & Mow, W. H. (2010). Affordable cyclostationary-based spectrum sensing for cognitive radio with smart antennas. IEEE Transactions on Vehicular Technology, 59(4), 1877–1886.
Kay, S. M. (1998). Fundamentals of statistical signal processing. Volume 2: Detection theory. Upper Saddle River, NY: Prentice-Hall.
Ma, J., et al. (2008). Soft combination and detection for cooperative spectrum sensing in cognitive radio networks. IEEE Transaction on Wireless Communications, 7(11), 4502–4507.
Choi, H.-H., et al. (2008). Adaptive sensing threshold control based on transmission power in cognitive radio systems. In IEEE conference on cognitive radio oriented wireless networks and communication (CrownCom) (pp. 1–6).
Wang, N., et al. (2013). Adaptive spectrum sensing algorithm under different primary user utilizations. IEEE Communications Letters, 17(9), 1838–1841.
Mariani, A., et al. (2011). Effects of noise power estimation on energy detection for cognitive radio applications. IEEE Transactions on Communications, 59(12), 3410–3420.
Ye, Z. et al. (2008). Energy detection using estimated noise variance for spectrum sensing in cognitive radio networks. In IEEE wireless communications and networking conference (WCNC) (pp. 711–716).
Peh, E., & Liang, Y.-C. (2007). Optimization for cooperative sensing in cognitive radio networks. In IEEE wireless communications and networking conference (WCNC) (pp. 27–32).
Singh, N. T. & Singh, B. J. (2014). Performance improvement in sensing error probability for low SNR scenarios in cognitive radio networks. In IEEE international conference on recent advances and innovations in engineering (ICRAIE) (pp. 1–4).
Cabric, D., et al. (2006). Experimental study of spectrum sensing based on energy detection and network cooperation. In Proceedings of the international technology and policy for accessing spectrum.
Moghimi, F., et al. (2009). Lp-norm spectrum sensing for cognitive radio networks impaired by non-gaussian noise. In Proceedings of the IEEE conference GLOBECOM (pp. 1–6).
Stotas, S., & Nallanathan, A. (2011). Enhancing the capacity of spectrum sharing cognitive radio networks. IEEE Transactions on Vehicular Technology, 60(8), 3768–3779.
Verma, G., & Sahu, O. P. (2015). Interference aware optimization of throughput in cognitive radio system. Defence Science Journal, 65, 312–318.
Verma, G., & Sahu, O. P. (2015). Throughput enhancement to the cognitive radio networks under the precaution is better than the cure approach (PBC). In Proceedings of the IEEE international conference on signal processing and communication engineering systems (SPACES) (pp. 1–4). Vijayawada: K.L. University.
Verma, G., & Sahu, O. P. (2015). Throughput enhancement to the cognitive radio networks under the precaution based cooperation of the primary users. In Proceedings of the IEEE international conference on signal processing, informatics, communication and energy systems (SPICES) (pp. 1–4). Calicut: NIT Calicut.
Lin, Y.-E., et al. (2013). On using interference-aware spectrum sensing for dynamic spectrum access in cognitive radio networks. IEEE Transactions on Mobile Computing, 12(3), 461–474.
Kan, C., et al. (2013). Optimization of cooperative sensing in interference-aware cognitive radio networks over imperfect reporting channel. In IEEE international conference on wireless communication and signal processing (WCSP) (pp. 1–6).
Dubey, R. K., & Verma, G. (2015). Improved spectrum sensing for cognitive radio based on adaptive threshold. In IEEE international conference on advances in computing and communication engineering (ICACCE) (pp. 253–256).
Benitez, M. L., et al. (2013). Signal uncertainty in spectrum sensing for cognitive radio. IEEE Transactions on Communications, 61(4), 1231–1241.
Benitez, M. L., et al. (2010). Performance of spectrum sensing for cognitive radio based on field measurements of various radio technologies. In IEEE international conference on European wireless (EW) (pp. 969–977).
Lehtomaki, J. J., et al. (2007). CFAR outlier detection with forward methods. IEEE Transactions on Signal Processing, 55(9), 4702–4706.
Hamdi, K., et al. (2007). Power control in cognitive radio systems based on spectrum sensing side information. In International conference on communications (ICC) (pp. 5161–5165).
Dubey, R. K., & Verma, G. (2015). Improved spectrum sensing for cognitive radio based on adaptive double threshold. International Journal of Emerging Trends in Electrical and Electronics (IJETEE), 11(2), 1–6.
Nasreddine, J., et al. (2010). Location-based adaptive detection threshold for dynamic spectrum access. In IEEE symposium on new frontiers in dynamic spectrum (pp. 1–10).
Kan, C., et al. (2012). Sensing-throughput tradeoff for interference-aware cognitive radio networks. In IEEE international conference on computer science and network technology (ICCSNT) (pp. 660–665).
Werner, J., et al. (2013). Estimating the primary user location and transmit power in cognitive radio systems using extended kalman filters. In IEEE international conference on wireless on-demand network systems and services (WONS) (pp. 68–73).
Radhi, N., et al. (2011). Estimate primary user localization using cognitive radio networks. In IEEE international conference on innovations in information technology (IIT) (pp. 381–385).
Wang, J., et al. (2010). Weighted centroid algorithm for estimating primary user location: theoretical analysis and distributed implementation. arXiv:1011.2313 (pp. 1–25).
Wild, B., et al. (2005). Detecting primary receivers for cognitive radio applications. IEEE symposium on new frontiers in dynamic spectrum access networks (DySPAN) (pp. 124–130).
Xiao, L., et al. (2007). Sensor-assisted localization in cellular systems. IEEE Transactions on Wireless Communications, 6(12), 4244–4248.
Huang, T., & Li, J. (2013). A weighted cooperative spectrum sensing scheme based on dynamic double energy thresholds in cognitive radio networks. In IEEE conference, global high tech congress on electronics (GHTCE) (pp. 201–204).
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Verma, G., Sahu, O.P. Intelligent selection of threshold in cognitive radio system. Telecommun Syst 63, 547–556 (2016). https://doi.org/10.1007/s11235-016-0141-y
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11235-016-0141-y