Abstract
Decoy-state method has been widely employed in the quantum key distribution (QKD), since it can not only solve photon-number-splitting attacks but also substantially improve the QKD performance. In conventional three-intensity decoy-state proposal, one not only needs to randomly modulate light sources to different intensities, but also has to prepare them into different bases, which may cost a lot of random numbers in practical applications. Here, we propose a simple decoy-state scheme with biased basis choices where the decoy pulses are only prepared in X basis. Through this way, it can save cost of random numbers and further simplify the electronic control system. Moreover, we carry out corresponding proof-of-principle demonstration. By incorporating with lower-loss asymmetric Mach–Zehnder interferometers and superconducting single-photon detectors, we can obtain a secret key rate of 1.65 kbps at 201 km and 19.5 bps at 280 km coiled optical fibers, respectively, showing very promising applications in future quantum communications.
Similar content being viewed by others
Explore related subjects
Discover the latest articles, news and stories from top researchers in related subjects.Avoid common mistakes on your manuscript.
1 Introduction
Quantum key distribution (QKD), as a means of symmetric encryption technique, allows to share secret keys between two legitimate communicating parties (Alice and Bob) at certain distance even under existence of an eavesdropper, Eve. Its unconditional security based on the laws of quantum physics [1,2,3] has received widespread attention. Since the first BB84 protocol was proposed by Bennett and Brassard [4], it has been widely implemented with various schemes [5,6,7,8,9]. Nowadays, more and more field test QKD networks have been built in the world [10,11,12,13,14,15].
Generally, a weak coherent source (WCS) is widely applied in most QKD systems, since the ideal single-photon source is not yet available under current technology. However, this source opens a back door for sophisticated eavesdroppers such as adopting the photon-number-splitting (PNS) attacks [16, 17], which significantly degrades the performance of QKD system due to the non-negligible multiphoton components. Fortunately, the decoy-state method [18, 19] was proposed as an efficient countermeasure to solve this security issue. Up to date, a great many QKD implementations with decoy-state method have been reported [20,21,22,23].
In most reported QKD transmission, standard three-intensity decoy-state method has been implemented [18, 19], where the light sources are randomly modulated into three different intensities and simultaneously each intensity is randomly prepared into X or Z basis. Obviously, during the modulation and state preparation processes, it consumes a large number of random numbers and raises high requirements for electric circuit control in high-speed QKD system. In order to reduce both the consumption of random numbers and precision for electric circuit control, we propose a simplified decoy-state scheme with biased basis choices. Unlike standard three-intensity decoy-state proposal, it only needs to prepare the decoy states into X basis, then the redundancy on preparing states in Z basis for the decoy states is removed.
In this manuscript, we carry out a proof-of-principle experimental demonstration for the scheme with biased basis choices. We run a 50 MHz clocked setup with phase-coding scheme. By incorporating with lower-loss asymmetric MZ interferometers and superconducting single-photon detectors, we can achieve secret key rates of 1.65 kbps at 201 km and 19.5 bps at 280 km, respectively.
The organization of the paper is as follows. In Sect. 2, we briefly review the theory of decoy-state with biased basis choices; in Sect. 3, we describe our experimental setup; in Sect. 4, we analyze the experimental data; finally, conclusion and outlook are given out in Sect. 5.
2 Theory
In the following, let’s briefly review the operation stages for the decoy-state scheme with biased basis choices.
-
1.
Alice randomly modulates her light sources into three different intensities, the signal \((\mu )\), the weak decoy \((\nu )\) and the vacuum state (o), each with a probability of \(P_{\mu }, P_{\nu }, P_{o}\), individually. Moreover, the signal pulses \((\mu )\) are randomly prepared into X or Z basis, each with a probability of \(P_{X|\mu } \) or \( P_{Z|\mu }\), respectively. The weak decoy pulses are only prepared in X basis. The vacuum pulses do not need to choose any basis.
-
2.
Upon receiving pulses sent from Alice, Bob randomly carries out projection measurement with either X or Z basis, corresponding to a probability of \(P_X \) or \(P_Z\), individually. Meantime, he records all the measurement results.
-
3.
After finishing all pulses transmission and measurement, Alice and Bob publicly announce the basis applied on each pulse, and keep only the sifted keys with matched basis.
-
4.
Alice/Bob carries out post-processing processes, including error correction and privacy amplification, to obtain the secure keys.
Table 1 indicates the distinction on preparing states between the standard method and our present work. In the standard method, both signal state and decoy state are prepared in X or Z basis. Nevertheless, Alice does not need to choose X or Z basis for vacuum state. Differing from the standard method, the decoy state is only prepared in X basis in our present work, thereby reducing the complexity of the QKD system and the cost of random numbers.
In order to facilitate the understanding, we take polarization coding for example to provide the contrast of schematic diagram between the standard scheme and our scheme as shown in Figs. 1 and 2, respectively. Here, ‘\(+\)’ and ‘−’ denote X basis. ‘H’ and ‘V’ denote Z basis. As we can see from Fig. 1, Alice needs eight lasers to generate the signal or the decoy states , and prepares them in either Z or X basis. For vacuum state, all lasers are just blocked. In contrast, only six lasers are needed in the present work, as displayed in Fig. 2. Obviously, it can not only simplify the experimental setup, but also reduce random number cost with biased basis choices.
In our scheme, we use the WCS as light source, whose photon-number distribution follows a Poisson distribution : \(P_{\xi }(i) = \frac{\xi ^{i}}{i!}e^{-\xi }\), where \(i \in \{0,1,2...\}\) and \(\xi \) represents the average photon number per pulse. Besides, the channel can be modeled as a linear channel. We define \(Y_{i}\), \(Q_{i}\) and \(e_{i}\) to be the yield, the gain and error rate of an i-photon state, which can be expressed as: \(Y_{i} = 1-(1-Y_{0})(1-\eta )^{i}\) , \(Q_{i} = Y_{i}\frac{\xi ^{i}}{i!}e^{-\xi }\), \(e_{i} = \frac{e_{0}Y_{0}+e_{d}[1-(1-\eta )^{i}](1-Y_{0})}{Y_{i}}\), individually. Here, \(\eta \) is the overall transmission and detection efficiency, defined as \(\eta := t_{AB}\eta _{B}\), \(t_{AB}\) represents the transmittance of a channel with the length of \(\iota \) kilometers, defined as \(t_{AB}:= 10^{-\alpha \iota /10}\) where \(\alpha \) is the loss coefficient of optical fiber, and \(\eta _{B}\) corresponds to the detection efficiency at Bob’s side. \(Y_{0}\) is the background rate, which includes the detector dark count and other background noises. \(e_{d}\) denotes the probability that a photon hits the wrong detector. \(e_{0}\) is the error rate of the background, which is usually assumed as 0.5.
As proven in Ref. [24], for any \(i \ge 2\) and \(\mu> \nu >0\), the following inequalities hold for WCS,
Then, we can obtain a lower bound of the yield for single-photon pulses as:
where \( Q_\mu ^{X} \) and \(Q_\nu ^{X}\) represent the gain of decoy state and signal state in the X basis, respectively, which can be expressed as: \( Q_\mu ^{X} = \sum _{i=0}^\infty Y_{i}^{X}P_{\mu }(i) \), \( Q_\nu ^{X} = \sum _{i=0}^\infty Y_{i}^{X}P_{\nu }(i) \). The proof for Eq. (2) will be given in the appendix. Since the decoy state is only prepared in X basis, we are not able to observe the gain of the decoy state in Z basis. Fortunately, as described in Ref. [25], in principle, a single-photon state is basis independent, and the yields of single-photon state in different basis are equal, i.e., \( Y_{1}^{Z,L} = Y_{1}^{X,L} \). Similarly, we can obtain the upper bound of the quantum-bit error-rate (QBER) of single-photon pulses in X basis:
where \({E_\nu }^{X}\) represents the average QBER of decoy state in X basis, which can be expressed as: \( {E_\nu }^{X} = \frac{\sum _{i=0}^\infty e_{i}Y_{i}^{X}P_{\nu }(i)}{{Q_\nu }^{X}} \). Moreover, by referring Ref. [25] when taking the finite size effect into account, we can get the upper bound of the phase-flip error-rate with the following formula:
which depends on the bit error rate in X basis \(e_{1}^{bX}\) and the deviation of the phase error rate \(\theta _{X}\) from the extracted value under circumstance of finite size effect [25]. We have the following inequality [25]:
where \(P_{\theta _{X}}\) is a controllable variable set as \(10^{-7}\) in the simulation; \(n_{X} (:=N_{\nu }P_{X}Y_{1}^{X,L}\nu e^{-\nu })\) represents the amount of decoy states that Alice sends and Bob measures in the X basis and \(n_{Z} (:=N_{\mu }^{Z}P_{Z}Y_{1}^{Z,L}\mu e^{-\mu })\) is in accord with the amount of signal states that Alice sends and Bob measures in the Z basis. Here, we use \(N_{k}^{\alpha }\) to denote the number of pulses Alice prepares in k intensity and in \(\alpha \) basis, where \(k \in \{\mu , \nu , o \}\) and \(\alpha \in \{X, Z \}\). In our scheme, only \(N_{\mu }^{X}\), \(N_{\mu }^{Z}\), \(N_{\nu }\) and \(N_{o}\) are contained. Besides, the function \(\xi _{X}(\theta _{X})\) is given by [25]:
where \(q_{X}= \frac{n_{X}}{n_{X}+n_{Z}}\) and \(e_{bX}\) can be replaced by \(e_{1}^{bX}\). We can compute the value of \(\theta _{X}\) as long as \(P_{\theta _{X}}\) and \(e_{1}^{bX}\) are given. Therefore, the upper bound of \(e_{1}^{pZ}\) can be obtained.
Under practical experimental conditions, the finite size effect is non-negligible on account of a restricted number of pulses Alice sends. Taking statistical fluctuations into account, we make corresponding changes on estimation of \(Y_{1}^{X,L}\) and \(e_{1}^{bX,U}\). On the basis of the statistical fluctuation analysis [26, 27], we could achieve the following equations which can be used to estimate the values of \(Y_{1}^{X,L}\) and \(e_{1}^{bX,U}\):
Following the standard error analysis assumption, we set the deviations coefficient \(\sigma \) as 5.3, corresponding to a failure probability of \(10^{-7}\).
With the above, we can now calculate the secure key generation rate with the formula:
where \(Q_{\mu }^{Z}\), \(E_{\mu }^{Z}\) each represents the gain and the QBER in Z basis, whose values can be experimentally observed; \( q=P_{\mu }P_{Z|\mu }P_Z \) is the raw data sift factor; \( P_{\mu } \) is the probability of preparing the signal pulses; \( P_{Z|\mu } \) is the probability of sending out the signal pulses prepared in Z basis; \(Q_{1}^{Z,L} = Y_{1}^{Z,L}\mu e^{-\mu }\) and \(Y_{1}^{Z,L}\) are the lower bound of the gain and yield of single-photon components in Z basis, respectively. \(f_{EC}\) is the error correction inefficiency function; \(H(x)=-xlog_{2}(x)-(1-x)log_{2}(1-x) \) is the binary Shannon information function.
In order to give a visualized impression on the performance of the present scheme with biased basis choices, we do some simulations and compare it with the conventional decoy-state scheme, as shown in Fig. 3. The simulation parameters are listed out in Table 2. Besides, the loss coefficient of optical fiber is 0.2 dB/km and the data size is set at \(10^{8}\). We can see from Fig. 3 that, our present scheme is less sensitive to the finite size effect and shows advantages at longer transmission distances compared with the standard three-intensity decoy-state method.
3 Experiment
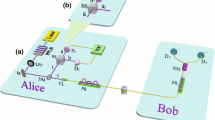
The schematic of our experimental setup is shown in Fig. 4. Here, we use phase-coding QKD scheme by employing asymmetrical Mach–Zehnder interferometers (AMZIs). At Alice’s side, a diode laser with a central wavelength of 1550.6 nm and a repetition rate of 50 MHz is used to generate phase randomized laser pulses. The pulses are randomly modulated into three different intensities through an intensity modulator (IM) and subsequently, sent into an AMZI. After passing through the first AMZI, each pulse is randomly prepared into one of the BB84 states \((0, \pi /2, \pi , 3\pi /2)\) through a phase modulator (PM), and then attenuated into single-photon level by an attenuator (Att). Afterwards, it is sent to Bob through ultralow-loss (ULL) single-mode fiber (G.652D ULL) with a transmission coefficient of 0.172 dB/km. At Bob’s side, another AMZI is employed to randomly carry out projection measurement with X or Z basis, individually. At the outport of the second AMZI, photons are measured through superconducting nanowire single-photon detectors (SNSPD), and their arriving time are recorded with an time-to-digital converter (TDC). Moreover, a control board (CB) is used to apply voltages for PM at either Alice’s or Bob’s side.
In our experiment, what we employed is a set of lower-loss AMZIs. As in Fig. 4, at each side, we use a fiber polarization beam-splitter (FPBS) to replace a fiber beam-splitters (FBS). Through this way, at least 3 dB channel loss can be reduced compared with normal AMZI setup. The SNSPD used here is commercial superconducting nanowire single-photon detector, which is cooled to 2.2 K, with a dark count rate of 15 per second, and a detection efficiency of 60%.
We run the experiment with ultralow-loss (ULL) single-mode fiber at two different lengths, i.e., 201 km and 280 km, individually. In each run, we keep the total number of pulses sent out at Alice’s side as \(N = 10^{11}\).
Schematic of the experimental setup. Laser: 1550 nm diode laser; IM: intensity modulator; Att: attenuator; CB: control board; PC: polarization controller; FBS: fiber beam-splitter; FPBS: fiber polarization beam-splitter; TDC: time to digital converter; SNSPD: superconducting nanowire single-photon detector; ULL fiber: ultralow-loss single-mode fiber; PM: phase modulator
4 Results and discussion
We implement the decoy-state protocol with biased basis choice in the finite-key regime over the ULL fiber lengths of 201 and 280 km. For each distance, the optimized parameters shown in Table 3 are obtained by simulation to achieve the optimal system performance. The total number of pulses sent from Alice is \(N = 10^{11}\). Taking statistical fluctuations into account [26, 27], the systematic parameters and the calculated secure key rates are shown in Table 3. Figure 5 evidently verifies that the experimental key rates are in agreement with the theoretical predictions. The experimental key rates are \(3.29\times 10^{-5}\) and \(3.90\times 10^{-7}\) bits per pulse corresponding to secret key extraction at the rates of 1.65 kbps and 19.5 bps, respectively.
5 Conclusions
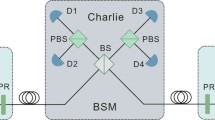
In summary, we present a proof-of-principle demonstration for the scheme of decoy-state QKD with biased basis choices, where the decoy pulses are only prepared in X basis. With biased basis choices, it can not only reduce the random number costs, but also improve the QKD performance in practical implementations. Furthermore, in combination with superconducting single-photon detectors and lower-loss asymmetric MZ interferometers, a secret key rate of 1.65 kbps and 19.5 bps at the transmission distances of 201 km and 280 km are observed, respectively. In principle, this system can be further extended to the measurement-device-independent protocols, and thus show more outstanding characteristics. Our work may provide valuable references for practical implementation of QKD in the near future.
References
Ekert, A.-K.: Quantum cryptography based on Bell’s theorem. Phys. Rev. Lett. 67, 661 (1991)
Lo, H.-K., Chau, H.F.: Unconditional security of quantum key distribution over arbitrarily long distances. Science 283, 2050 (1999)
Mayers, D.: Unconditional security in quantum cryptography. J. ACM 48, 351 (2001)
Bennett, C.H., Brassard, G.: Quantum cryptography: public key distribution and coin tossing. In: Proceedings of the IEEE International Conference on Computers, Systems and Signal Processing, pp. 175–179. IEEE, New York (1984)
Bruss, D.: Optimal eavesdropping in quantum cryptography with six states. Phys. Rev. Lett. 81, 3018 (1998)
Laing, A., Scarani, V., Rarity, J.-G., et al.: Reference-frame-independent quantum key distribution. Phys. Rev. A 82, 012304 (2010)
Lo, H.-K., Marcos, C., Bing, Q.: Measurement-device-independent quantum key distribution. Phys. Rev. Lett. 108, 130503 (2012)
Lucamarini, M., Dynesand, Z.-L., Shields, A.-J.: Overcoming the rate-distance limit of quantum key distribution without quantum repeaters. Nature 557, 400 (2018)
Sasaki, T., Yamamoto, Y., Koashi, M.: Practical quantum key distribution protocol without monitoring signal disturbance. Nature 509, 475 (2014)
Peev, M., et al.: The SECOQC quantum key distribution network in Vienna. New J. Phys. 11, 075001 (2009)
Sasaki, M., et al.: Field test of quantum key distribution in the Tokyo QKD network. Opt. Express 19, 10387 (2011)
Wang, S., et al.: Field and long-term demonstration of a wide area quantum key distribution network. Opt. Express 22, 21739 (2014)
Stucki, D., et al.: Long-term performance of the SwissQuantum quantum key distribution network in a field environment. Opt. Lett. 13, 123001 (2011)
Dynes, J.-F., et al.: Stability of high bit rate quantum key distribution on installed fiber. Opt. Express 20, 16339 (2012)
Dixon, A.-R., et al.: High speed prototype quantum key distribution system and long term field trial. Opt. Express 23, 7583 (2015)
Brassard, G., Lutkenhaus, N., Mor, T., Sanders, B.-C.: Limitations on practical quantum cryptography. Phys. Rev. Lett. 85, 1330 (2000)
Lutkenhaus, N., Jahma, M.: Quantum key distribution with realistic states: photon-number statistics in the photon-number splitting attack. New J. Phys. 4, 44 (2002)
Wang, X.-B.: Beating the photon-number-splitting attack in practical quantum crytography. Phys. Rev. Lett. 94, 230503 (2005)
Lo, H.-K., Ma, X., Chen, K.: Decoy state quantum key distribution. Phys. Rev. Lett. 94, 230504 (2005)
Frohlich, B., et al.: Long-distance quantum key distribution secure against coherent attacks. Optica 4, 163 (2017)
Boaron, A., et al.: Secure quantum key distribution over 421 km of optical fiber. Phys. Rev. Lett. 121, 190502 (2018)
Wang, Q., et al.: Experimental decoy-state quantum key distribution with a sub-poissionian heralded single-photon source. Phys. Rev. Lett. 100, 090501 (2008)
Zhang, C.-H., et al.: Proof-of-principle demonstration of parametric down-conversion source-based quantum key distribution over 40 dB channel loss. Opt. Express 26, 25921 (2008)
Zhou, Y.-H., Yu, Z.-.W., Wang, X.-B.: Tightened estimation can improve the key rate of measurement-device-independent quantum key distribution by more than 100%. Phys. Rev. A 89, 052325 (2014)
Fung, C.-H.F., Ma, X.-F., Chau, H.F.: Practical issues in quantum-key-distribution postprocessing. Phys. Rev. A 81, 012318 (2010)
Zhang, C.-H., Luo, S.-L., Guo, G.-C., Wang, Q.: Biased three-intensity decoy-state scheme on the measurement-device-independent quantum key distribution using heralded single-photon sources. Opt. Express 26, 4219 (2018)
Wang, X.-B., Yang, L., Peng, C.-Z., Pan, J.-W.: Decoy-state quantum key distribution with both source errors and statistical fluctuations. New J. Phys. 11, 075006 (2009)
Acknowledgements
The authors gratefully appreciate Hengtong Optic-Electric Co., Ltd., for providing lower-loss fibers. We gratefully acknowledge the financial support from the National Key R&D Program of China (Nos. 2018YFA0306400, 2017YFA0304100), the National Natural Science Foundation of China (Nos. 11774180, 61590932), the Leading-edge technology Program of Jiangsu Natural Science Foundation (BK20192001), and the Postgraduate Research & Practice Innovation Program of Jiangsu Province (SJCX19_0250).
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Appendix
Appendix
In this appendix, we will give the derivation process of Eqs. (1) and (2).
For the WCS, the probability of finding an i-photon state with intensity \(\xi \)\((\xi \in \{ \mu , \nu \})\) is given by: \(P_{\xi }(i) = \frac{\xi ^{i}}{i!}e^{-\xi }\). Then, we have
For any \(i \ge 2\), when \(\mu>\nu >0\), \(\frac{\mu }{\nu }>1\), therefore, the following inequalities hold
The Proof for Eq. (1) of the main text is done.
The gains of signal and decoy states can be written as:
With Eqs. (A3) and (A4), it is easy to get
Considering the conditions in Eq. (A2), we can get the following inequality:
It is easy to reach
The proof for Eq. (2) of the main text is finished.
Rights and permissions
About this article
Cite this article
Wu, WZ., Zhu, JR., Ji, L. et al. Proof-of-principle demonstration of decoy-state quantum key distribution with biased basis choices. Quantum Inf Process 19, 341 (2020). https://doi.org/10.1007/s11128-020-02852-w
Received:
Accepted:
Published:
DOI: https://doi.org/10.1007/s11128-020-02852-w