Abstract
On the basis of entanglement swapping of Bell states, Hwang et al. proposed a probabilistic quantum key distribution (PQKD) protocol Quantum Inf. Comput. 11(7-8), 615–637 (2011). Recently, Lin et al. Quantum Inf. Comput. 14(9-10), 757–762 (2014) proposed a unitary operation attack on Hwang et al.’s PQKD. However, unlike the unitary operation attack, this work points out that a malicious participant in Hwang et al.’s PQKD protocol can manipulate the secret key. As a result, the security requirements of a PQKD protocol, i.e., fairness, cannot be satisfied in their protocol. Moreover, the same attack can also crack the fairness requirement of the existing quantum key agreement (QKA) protocols. To overcome both problems, this paper proposes a new PQKD protocol based on the order rearrangement of the transmitted photons. Furthermore, the rearrangement method can also solve the key manipulation attack in QKA protocols.
Similar content being viewed by others
Explore related subjects
Discover the latest articles, news and stories from top researchers in related subjects.Avoid common mistakes on your manuscript.
1 Introduction
Quantum key distribution (QKD), which allows a sender to distribute a pre-determined secret key to a receiver through the transmission of quantum signals, is one of the most important research topics in quantum cryptography. Since the first QKD protocol was presented by Bennett and Brassard [1] in 1984 (also known as BB84), a variety of QKD protocols have been proposed [2,3,4,5,6,7,8,9,10,11,12,13,14,15,16,17,18,19]. Although the QKD protocols provide unconditional security [20, 21], they must assume that the participants are mutually trusted [22]. That is, they always follow the protocol and one participant must accept the key decided by the other participant.
In contrast to the QKD protocols, the participants in a quantum key agreement (QKA) and a probabilistic quantum key distribution (PQKD) are assumed to be mutually untrusted. A QKA protocol [23,24,25,26,27] is one whereby two or more participants negotiate a key over quantum channels and classical channels on the basis of their exchanged messages. Unlike QKA protocols, Hwang et al. [28] proposed the first PQKD protocol using Bell states and entanglement swapping, where two mutually suspicious participants can share an unpredictable key based on quantum mechanics. The PQKD protocol has the following features:
-
1.
Unpredictability: The key distributed is an unpredictable key.
-
2.
Fairness: No one can pre-determine the key even with a single bit advantage.
-
3.
Effectiveness: The intrinsic measurement uncertainty and entanglement swapping of photons are applied to facilitate the generation as well as distribution of a random key.
Recently, Lin et al. [29] proposed a unitary operation attack on Hwang et al.’s PQKD protocol. One malicious participant can manipulate the secret key by using the unitary operation attack without being detected. However, unlike the unitary operation attack, this paper reveals a common problem in these QKA protocols [23,24,25,26,27] and the PQKD protocol [28]. The problem further enables a key manipulation attack that threatens the security of these protocols. This study takes Hwang et al.’s PQKD protocol [28] as an example to show the key manipulation problem. That is, a legitimate but malicious participant can manipulate the secret key.
In order to avoid the unitary operation attack and the key manipulation attack, this paper proposes a new PQKD protocol using the entanglement swapping of Bell states and reordering of the transmitted qubits. Therefore, the malicious participant cannot obtain the correct secret key by performing a unitary operation attack and a key manipulation attack. Finally, two untrusted participants generate a random fairness secret key by using the entanglement swapping of Bell states.
The rest of this paper is organized as follows. Section 2 introduces Bell states and the entanglement swapping of Bell states. Section 3 reviews Hwang et al.’s PQKD protocol. Section 4 discusses the key manipulation problem of Hwang et al.’s protocol. Section 5 describes the proposed PQKD protocol. Section 6 analyzes the security and the fairness of the proposed PQKD protocol. Finally, Section 7 concludes our results.
2 Background
The Einstein-Podolsky-Rosen (EPR) pair, also called the Bell state, is a two-particle quantum entangled state. It can be described by four orthogonal maximal states as follows:
The entanglement swapping is shown in Table 1. Suppose that Alice and Bob prepare Bell states |ϕ+〉, respectively. Then, they exchange the second qubit of |ϕ+〉 and perform the Bell measurement on their first qubit and the received second qubit. After that, one of the following four measurement results, {(|ϕ+〉a1b2,|ϕ+〉b1a2),(|ϕ−〉a1b2,|ϕ−〉b1a2), (|ψ+〉a1b2,|ψ+〉b1a2),(|ψ−〉a1b2,|ψ−〉b1a2)}, appears randomly. It is obvious that Alice and Bob can derive the same unitary operation, which transforms the initial state to the measurement result.
3 Review of Hwang et al.’s PQKD Protocol
Alice and Bob, two mutually untrusted communicants, wish to share a fair n-bit random key by using the entanglement swapping of Bell states. Let the four Bell states |Φ+〉, |Φ−〉, |Ψ+〉 and |Ψ−〉 represent two-bit information “00,” “01,” “10,” and “11,” respectively. Here, the classical communication channels are assumed to be authenticated, and the quantum channels are assumed to be ideal. The PQKD protocol proceeds as follows:
- Step 1.:
-
Alice generates a sequence of n Bell states in \(|{\Phi }^{+} \rangle =\frac {1}{\sqrt {2} } (|00\rangle +|11\rangle )\),S = {s1,s2,…,sn}, where \(s_{i} =\{ q_{A1}^{i} ,\text { }q_{A2}^{i} \} \),i = 1,2,…,n. She takes the second qubit to form a new sequence \(S_{B} =\{ q_{A2}^{i} \} \), and the first qubit to form the other sequence \(S_{A} =\{ q_{A1}^{i} \} \), for i = 1,2,…,n. Then, Alice arbitrarily performs a Hadamard operation H (\(=\frac {1}{\sqrt {2} } [(|0\rangle +|1\rangle )\langle 0|+(|0\rangle -|1\rangle )\langle 1|]\)) or an identity operation I (= |0〉〈0| + |1〉〈1|) on \(S_{B} =\{ q_{A2}^{i} \} \) to form a new sequence \(S_{B}^{\prime } =\{q_{A2}^{{\prime }{i}}\} \), and then sends it to Bob.
- Step 2:
-
Upon receiving \(S_{B}^{\prime } =\{q_{A2}^{\prime {i}}\} \), Bob also generates a sequence of n Bell states in \(|{\Phi }^{+} \rangle =\frac {1}{\sqrt {2} } (|00\rangle +|11\rangle )\),T ={t1,t2,…,tn}, where \(t_{i} =\{ q_{B1}^{i} , q_{B2}^{i}\} \),i= 1,2,…,n. He takes the second qubit to form a new sequence \(T_{B} =\{ q_{B2}^{i} \} \), and the first qubit to form the other sequence \(T_{A} =\{ q_{B1}^{i} \} \), for i = 1,2,…,n. He performs a permutation π on \(T_{A} =\{ q_{B1}^{i} \} \) to form a new sequence \(T^{\prime }_{A} =\{ q_{B1}^{\prime {i}}\} \) and then sends it to Alice.
- Step 3:
-
Alice randomly chooses j positions as a check set C for an eavesdropping check. Then, she performsH on \(S_{A} =\{ q_{A1}^{i} \} \), for which the corresponding \(S_{B} =\{ q_{A2}^{i} \} \) were performed with the same H in Step 1. After that, she announces the positions of C to Bob through an authenticated classical channel.
- Step 4:
-
Bob derives the 2n-bit raw key by performing a Bell measurement on \(S_{B} =\{ q_{A2}^{i} \} \) and \(T_{B} =\{ q_{B2}^{i} \} \), i.e., \(K_{BA} =\{ BM(q_{A2}^{1} ,q_{B2}^{1} ),BM(q_{A2}^{2} ,q_{B2}^{2} ),K ,BM(q_{A2}^{n} ,q_{B2}^{n} )\} \). Then, he sends π and the Bell measurement results KC of C to Alice through an authenticated classical channel. He derives the key as K = KBA – KC. Let K be the remaining bits in KBA after removing the checking bits in KC.
- Step 5:
-
Alice recovers \(T_{A} =\{ q_{B1}^{i} \} \) from \(T_{A}^{\prime } =\{ q_{B1}^{\prime {i}}\} \) on the basis of the π and derives the 2n-bit raw key as \(K_{AB} =\{ BM(q_{A1}^{1} ,q_{B1}^{1} ),BM(q_{A1}^{2} ,q_{B1}^{2} ),K ,BM(q_{A1}^{n} ,q_{B1}^{n} )\} \). It is noted that KAB = KBA. According to KC received from Bob and that measured by Alice herself, Alice can detect the presence of eavesdropping. If there is no eavesdropper, then she sets K = KAB – KC as the key shared with Bob. Otherwise, they abort the process and start a new one.
It appears that neither Alice nor Bob can manipulate the outcome of the shared key K, because the result of entanglement swapping is unpredictable. However, this paper reveals in the following section that Bob can determine one key bit completely.
4 Key Manipulation Problem
The PQKD protocol is in a mutually untrusted environment where Alice and Bob are mutually opposed to each other. Several problems could arise from the PQKD protocol if the public discussion is not carefully designed. These are explained in the following example.
Suppose that the first bit of the raw key between Alice and Bob in Step 4 is “0.” If Bob prefers the first bit of the raw key to be “0,” then he will follow the protocol. If, however, Bob prefers the first bit of the raw key to be “1,” then he can send an incorrect KC as his fake Bell measurement result C to Alice for public discussion, which will fail eventually. Hence, they will abort the process in Step 5 and start a new one until the first bit of the raw key is “1.” Accordingly, Bob could manipulate the first bit of the raw key through the public discussion, even though the unpredictability in the Bell state entanglement swapping is applied to generate and distribute the key. Thus, the PQKD protocol fails to provide “fairness” between both participants because one bit of the final shared key can be determined by the participant who first knows the raw key of the other. The same problem can also be identified in the QKA protocols described in [23,24,25,26,27].
5 The Proposed PQKD Protocol
To solve the unitary operation attack and key manipulation attack, this section introduces a new PQKD protocol. Suppose that two untrusted participants, Alice and Bob, want to distribute an unpredictable key \({K^{M}_{P}}\) by a quantum channel. Here, the classical channels are assumed to be authenticated, and the quantum channels are ideal.
- Step 1:
-
Alice prepares n Bell states randomly chosen from {|ϕ+〉,|ϕ−〉,|ψ+〉,|ψ−〉}. She takes all of the first qubits and second qubits from each Bell state to form the ordered sequences SA1 and SA2, respectively; then, Alice shuffles SA2 to obtain \(S_{A2}^{\prime }\). Alice generates n decoy photons arbitrarily chosen from {|0〉,|1〉,|+〉,|−〉}, and then randomly inserts these decoy photons into \(S_{A2}^{\prime }\) to form \(S_{A2}^{{\prime }*}\). Similarly, Bob can produce SB1 and \(S_{B2}^{{\prime }*}\) in the same way. Finally, Alice delivers \(S_{A2}^{{\prime }*}\) to Bob.
- Step 2:
-
After Bob receives the sequences sent from Alice, Alice announces the measurement positions and the bases of the decoy photons in \(S_{A2}^{{\prime }*}\). According to the measurement results of decoy photons replied from Bob, Alice can check the existence of eavesdroppers. If there is no eavesdropper, she sends an acknowledgment to Bob through an authenticated classical channel. Otherwise, they abort the process and start a new one. Similarly, Bob sends \(S_{B2}^{{\prime }*}\) to Alice and performs the eavesdropping check.
- Step 3:
-
After the eavesdropping check, Alice has two sequences SA1 and \(S_{B2}^{\prime }\), and Bob also has two sequences SB1 and \(S_{A2}^{\prime }\). Bob announces his shuffled information. According to the shuffled information sent from Bob, Alice can recover \(S_{B2}^{\prime }\) into the correct order of SB2. Then, Alice performs the Bell measurement on SA1 and SB2 to obtain 2n bits of an unpredictable key KP, where the KP is “00” if the unitary operation is I, “01” if σz, “10” if σx, and “11” if iσy.
- Step 4:
-
After Alice obtains the unpredictable key KP, she announces her shuffled information of \(S_{A2}^{\prime }\). Then, Bob also can recover the correct order of SA2 and performs the Bell measurement on SB1 and SA2 to obtain an unpredictable key KP.
According to Section 2, Alice and Bob can obtain the same unpredictable key KP. Furthermore, neither one can manipulate the unpredictable key KP.
6 Security Analysis
In this section, we discuss the security and the fairness of the proposed PQKD protocol. The security of the proposed PQKD protocol is analyzed from the eavesdropping attack, Lin et al.’s unitary operation attack [29], and the key manipulation problem.
6.1 The Eavesdropping Attack
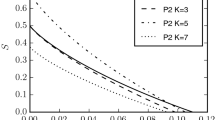
In order to avoid the eavesdropping attack, two untrusted participants use enough decoy photons, which are randomly generated from one of the four states {|0〉,|1〉,|+〉,|−〉}. Then, they randomly insert these decoy photons in their transmitted sequences. Because an eavesdropper does not know the bases and the positions of the decoy photons, an eavesdropper is detected in public discussion when he or she tries to measure and resend the quantum sequences. The probability of detecting an eavesdropper is \(\mathrm {1-}{\mathrm {(}\frac {3}{4}\mathrm {)}}^{d}\), where \(\frac {3}{4}\) is the probability that an eavesdropper can pass the eavesdropping check in each decoy photon, and d is the total number of decoy photons. Therefore, if d is large enough, the probability \(\mathrm {1-}{\mathrm {(}\frac {3}{4}\mathrm {)}}^{d}\) will be close to 1.
6.2 Lin et al.’s Unitary Operation Attack
In Lin et al.’s attack, the malicious communicant, e.g., Bob, can perform unitary operations on the qubits sent from Alice and resend these qubits to Alice to manipulate the secret key. However, in the proposed PQKD protocol, Alice shuffles her transmitted qubits SA2 to \(S_{A2}^{\prime }\) in Step 1. Then, she asks Bob to announce his order first in Step 3. Because Bob does not know the correct order of \(S_{A2}^{\prime }\) before Step 4, he cannot manipulate the secret key by performing unitary operations on \(S_{A2}^{\prime }\) and resending to Alice. Therefore, the proposed protocol does not enable this attack.
6.3 Key Manipulation Problem
In order to avoid the key manipulation problem, Alice and Bob shuffle their transmitted qubits in Step 1 and Step 2. Because the measurement results are unpredictable on two different EPR pairs, the malicious communicant cannot obtain the correct secret key by performing the Bell measurement in public discussion. Therefore, the malicious participant does not deliver the fake measurement results in public discussion. The proposed PQKD protocol is fair under the key manipulation problem.
7 Conclusions
This study showed that there is a key manipulation problem in the QKA protocols and the PQKD protocol. Moreover, in order to avoid Lin et al.’s unitary operation attack [29] and the key manipulation problem, this paper proposes a new PQKD protocol based on the entanglement swapping of Bell states and order rearrangement of the transmitted photons. It also can avoid the eavesdropping attack by using decoy photons. Because the fairness of the proposed PQKD protocol is based on the order rearrangement of the transmitted photons, the PQKD protocol might be unsecure if the bit length of the shared key is too short. Therefore, how to design a secure PQKD protocol without this problem will be an interesting topic of future research.
References
Bennett, C.H., Brassard, G.: Quantum cryptography: Public key distribution and coin tossing. In: Proceedings of IEEE international conference on computers systems and signal processing (1984)
Bennett, C.H.: Quantum cryptography using any two nonorthogonal states. Phys. Rev. Lett. 68(21), 3121–3124 (1992)
Braunstein, S.L., Pirandola, S.: Side-channel-free quantum Key distribution. Phys. Rev. Lett. 108(13), 130502 (2012)
Chen, P., Li, Y.S., Deng, F.G., Long, G.L.: Measuring-basis encrypted quantum key distribution with four-state systems. Commun. Theor. Phys. 47(1), 49–52 (2007)
Deng, F.G., Long, G.L., Wang, Y., Xiao, L.: Increasing the efficiencies of random-choice-based quantum communication protocols with delayed measurement. Chinese Phys. Lett. 21(11), 2097–2100 (2004)
Ekert, A.K.: Quantum cryptography based on Bell’s theorem. Phys. Rev. Lett. 67(6), 661–663 (1991)
Gao, G.: Quantum key distribution by comparing Bell states. Opt. Commun. 281(4), 876–879 (2008)
Hwang, T., Hwang, C.C., Tsai, C.W.: Quantum key distribution protocol using dense coding of three-qubit W state. Eur. Phys. J. D. 61(3), 785–790 (2011)
Hwang, T., Lee, K.C.: EPR Quantum key distribution protocols with potential 100% qubit efficiency. Iet Inform. Secur. 1(1), 43–45 (2007)
Hwang, T., Lee, K.C., Li, C.M.: Provably secure three-party authenticated quantum key distribution protocols. IEEE T Depend Secure 4(1), 71–80 (2007)
Li, X.H., Deng, F.G., Zhou, H.Y.: Efficient quantum key distribution over a collective noise channel. Phys. Rev. A 78(2), 022321 (2008)
Li, X.H., Zhao, B.K., Sheng, Y.B., Deng, F.G., Zhou, H.Y.: Fault tolerant quantum key distribution based on quantum dense coding with collective noise. Int. J. Quant. Infor. 7(8), 1479–1489 (2009)
Li, X.-H., Duan, X.-J., Deng, F.-G., Zhou, H.-Y.: Error-Rejecting Bennett–Brassard–Mermin Quantum key distribution protocol based on linear optics over a Collective-Noise channel. Int. J. Quantum. Inf. 08(07), 1141–1151 (2010)
Long, G.L., Liu, X.S.: Theoretically efficient high-capacity quantum-key-distribution scheme. Phys. Rev. A 65(3), 032302 (2002)
Pirandola, S., Garcia-Patron, R., Braunstein, S.L., Lloyd, S.: Direct and rever se secret-key capacities of a quantum channel. Phys. Rev. Lett. 102(5), 050503 (2009)
Shih, H.C., Lee, K.C., Hwang, T.: New efficient Three-Party quantum key distribution protocols. IEEE J. Sel. Top Quant. 15(6), 1602–1606 (2009)
Yuan, H., Song, J., Han, L.F., Hou, K., Shi, S.H.: Improving the total efficiency of quantum key distribution by comparing Bell states. Opt. Commun. 281(18), 4803–4806 (2008)
Zhang, Z.J., Man, Z.X., Shi, S.H.: An efficient multiparty quantum key distribution scheme. Int. J. Quant. Infor. 3(3), 555–560 (2005)
Zhao, B.K., Sheng, Y.B., Deng, F.G., Zhang, F.S., Zhou, H.Y.: Stable and deterministic quantum key distribution based on differential phase shift. Int. J. Quantum Inf. 7(4), 739–745 (2009)
Lo, H.K., Chau, H.F.: Unconditional security of quantum key distribution over arbitrarily long distances. Science 283(5410), 2050–2056 (1999)
Shor, P.W., Preskill, J.: Simple proof of security of the BB84 quantum key distribution protocol. Phys. Rev. Lett. 85(2), 441–444 (2000)
Ben-Or, M., Horodecki, M., Leung, D.W., Mayers, D., Oppenheim, J.: The universal composable security of quantum key distribution. Theory of Cryptography Proceedings 3378, 386–406 (2005)
Zhou, N., Zeng, G., Xiong, J.: Quantum key agreement protocol. Electron Lett. 40(18), 1149–1150 (2004)
Chong, S.K., Hwang, T.: Quantum key agreement protocol based on BB84. Opt. Commun. 283(6), 1192–1195 (2010)
Chong, S.K., Tsai, C.W., Hwang, T.: Improvement on Quantum key agreement protocol with maximally entangled states. Int. J. Theor. Phys. 50(6), 1793–1802 (2011)
Shi, R.H., Zhong, H.: Multi-party quantum key agreement with bell states and bell measurements. Quantum Inf. Process 12(2), 921–932 (2013)
Liu, B., Gao, F., Huang, W., Wen, Q.Y.: Multiparty quantum key agreement with single particles. Quantum Inf. Process 12(4), 1797–1805 (2013)
Hwang, T., Tsai, C.W., Chong, S.K.: Probabilistic quantum key distribution. Quantum Inf. Comput. 11(7-8), 615–637 (2011)
Lin, T.-H., Yang, C.-W., Hwang, T.: Unitary operation attack and the improvement on probabilistic quantum key distribution. Quantum Inf. Comput. 14(9-10), 757–762 (2014)
Acknowledgments
This research was partially supported by the Ministry of Science and Technology, Taiwan, R.O.C., under the Contract No. MOST 106-2218-E-039-002-MY3, and also was partially supported by China Medical University under the Contract No. CMU106-N-07.
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Yang, CW. New Probabilistic Quantum Key Distribution Protocol. Int J Theor Phys 57, 3651–3657 (2018). https://doi.org/10.1007/s10773-018-3878-0
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s10773-018-3878-0