Abstract
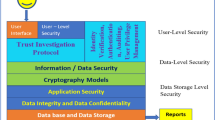
The need to access data quickly without increasing the physical memory in devices like computers and mobile made big IT firms, IT persons and individuals move to cloud computing, but the confidentiality of data is the main concern. There are various stages of data travel while stored onto the cloud and many breaches between these stages of data storage. Many advanced technologies can secure data on the cloud; machine learning technique is one of them. The machine itself will manage the security with less human involvement. This paper is focused on cloud computing and the implementation of machine learning (ML) techniques and models in the field of cloud security to protect data from threats and malware.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Mell P, Grance T (2009) The NIST definition of cloud computing. National Institute of Standards and Technology (NIST), Information Technology Laboratory. www.csrc.nist.gov
Subashini S, Kavitha V (2010) A survey on security issues in service delivery models of cloud computing. J Netw Comput Appl (Elsevier), 11 July 2010
Hajdarevic K (2017) Survey on machine learning algorithms as cloud service for CIDPS. In: 25th telecommunications forum TELFOR
Bhamare D, Salman T, Samaka M, Erbad A, Jain R (2016) Feasibility of supervised machine learning for cloud security. In: International conference on information science and security (ICISS)
Gulenko A, Wallschläger M, Schmidt F, Kao O, Liu F (2016) Evaluating machine learning algorithms for anomaly detection in cloud. In: 2016 IEEE international conference on Big Data (Big Data)
Osanaiye O, Cai H, Choo K-KR, Dehghantanha A, Xu Z, Dlodlo1 M (2016) Ensemble-based multi-filter feature selection method for DDoS detection in cloud computing. EURASIP J Wireless Commun Netw
Garg A, Maheshwari P (2016) A hybrid intrusion detection system: a review. In: 2016 10th international conference on intelligent systems and control (ISCO), Coimbatore, India
Duessel P, Gehl C, Flegel U, Dietrich S, Meier M (2017) Detecting zero-day attacks using context-aware anomaly detection at the application-layer. Springer, Heidelberg
Huang T, Zhu Y, Zhang Q, Zhu Y, Wang D, Qiu M, Liu L (2013) An LOF-based adaptive anomaly detection scheme for cloud computing. In: 37th annual computer software and applications conference workshops
Songma S, Chimphlee W, Maichalernnukul K, Sanguansat P (2012) Classification via k-means clustering and distance-based outlier detection. In: 2012 tenth international conference on ICT and knowledge engineering
Chiu C-Y, Yeh C-T, Lee Y-J (2013) Frequent pattern based user behavior anomaly detection for cloud system. In: 2013 conference on technologies and applications of artificial intelligence
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2023 The Author(s), under exclusive license to Springer Nature Singapore Pte Ltd.
About this paper
Cite this paper
Bhatnagar, D., Gupta, A. (2023). Survey on Implementation of Machine Learning in Cloud Security. In: Tuba, M., Akashe, S., Joshi, A. (eds) ICT Infrastructure and Computing. ICT4SD 2023. Lecture Notes in Networks and Systems, vol 754. Springer, Singapore. https://doi.org/10.1007/978-981-99-4932-8_4
Download citation
DOI: https://doi.org/10.1007/978-981-99-4932-8_4
Published:
Publisher Name: Springer, Singapore
Print ISBN: 978-981-99-4931-1
Online ISBN: 978-981-99-4932-8
eBook Packages: Intelligent Technologies and RoboticsIntelligent Technologies and Robotics (R0)