Abstract
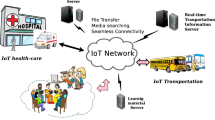
The resources in Internet of Things (IoT) are distributed among different physical geographic locations. In centralized resource discovery, the resources are registered in a centralized third-party server, and the clients can discover any resource by querying the centralized entity. In the decentralized resource discovery, the task of resource registration and discovery is distributed among many nodes in the system. Replacing a centralized entity with a distributed set of nodes requires that a system fulfils some security and performance requirements. In this paper, the centralized and decentralized resource discovery models are discussed. In addition, the properties of decentralized resource discovery are studied, and some of the fundamental and most important requirements for such models are discussed. Each of the fundamental requirements in decentralized resource discovery is analysed, and the possible approaches and their feasibility in IoT network are studied.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
B. Zhang, N. Mor, J. Kolb, D.S. Chan, K. Lutz, E. Allman, J. Wawrzynek, E. Lee, J. Kubiatowicz, The cloud is not enough: saving iot from the cloud, in 7th Workshop on Hot Topics in Cloud Computing (HotCloud 15) (2015)
M.B. Kamel, B. Crispo, P. Ligeti, A decentralized and scalable model for resource discovery in iot network, in 2019 International Conference on Wireless and Mobile Computing, Networking and Communications (WiMob) (IEEE, 2019), pp. 1–4
B. Rana, Y. Singh, P.K. Singh, A systematic survey on internet of things: energy efficiency and interoperability perspective. Trans. Emerg. Telecommun. Technol. (2020)
P. Malhotra, Y. Singh, P. Anand, D.K. Bangotra, P.K. Singh, W.-C. Hong, Internet of things: evolution, concerns and security challenges. Sensors 21(5), 1809 (2021)
K. Khalil, K. Elgazzar, M. Seliem, M. Bayoumi, Resource discovery techniques in the internet of things: a review. Intern. Things 100293 (2020)
H. Zhang, Y. Wen, H. Xie, N. Yu, A survey on distributed hash table (dht): theory, platforms, and applications (2013)
M.B. Kamel, Y. Yan, P. Ligeti, C. Reich, A decentralized resource discovery using attribute based encryption for internet of things, in 2020 4th Cyber Security in Networking Conference (CSNet) (IEEE, 2020), pp. 1–3
A. Rowstron, P. Druschel, Pastry: scalable, decentralized object location, and routing for large-scale peer-to-peer systems, in IFIP/ACM International Conference on Distributed Systems Platforms and Open Distributed Processing (Springer, 2001), pp. 329–350
I. Stoica, R. Morris, D. Karger, M.F. Kaashoek, H. Balakrishnan, Chord: a scalable peer-to-peer lookup service for internet applications. ACM SIGCOMM Comput. Commun. Rev. 31(4), 149–160 (2001)
P. Maymounkov, D. Mazieres, Kademlia: A peer-to-peer information system based on the xor metric, in International Workshop on Peer-to-Peer Systems (Springer, 2002), pp. 53–65
B.Y. Zhao, L. Huang, J. Stribling, S.C. Rhea, A.D. Joseph, J.D. Kubiatowicz, Tapestry: a resilient global-scale overlay for service deployment. IEEE J. Sel. Areas Commun. 22(1), 41–53 (2004)
W.D. Maurer, T.G. Lewis, Hash table methods. ACM Comput. Surv. (CSUR) 7(1), 5–19 (1975)
S.K. Datta, R.P.F. Da Costa, C. Bonnet, Resource discovery in internet of things: current trends and future standardization aspects, in 2nd World Forum on Internet of Things (WF-IoT) (IEEE, 2015), pp. 542–547
H. Wirtz, T. Heer, R. Hummen, K. Wehrle, Mesh-dht: a locality-based distributed look-up structure for wireless mesh networks, in 2012 IEEE International Conference on Communications (ICC) (2012), pp. 653–658
S. Ali, S. Banerjea, M. Pandey, N. Tyagi, Wireless fog-mesh: a communication and computation infrastructure for iot based smart environments,” in Mobile, Secure, and Programmable Networking (Springer International Publishing, Cham, 2019), pp. 322–338
H. Wirtz, T. Heer, M. Serror, K. Wehrle, Dht-based localized service discovery in wireless mesh networks, in 2012 IEEE 9th International Conference on Mobile Ad-Hoc and Sensor Systems (MASS 2012) (IEEE, 2012), pp. 19–28
R. Mokadem, A. Hameurlain, A.M. Tjoa, “Resource discovery service while minimizing maintenance overhead in hierarchical dht systems. Int. J. Adapt. Resil. Autonom. Syst. (IJARAS) 3(2), 1–17 (2012)
Y. Yan, M.B. Kamel, P. Ligeti, Attribute-based encryption in cloud computing environment, in 2020 International Conference on Computing, Electronics and Communications Engineering (iCCECE) (IEEE, 2020), pp. 63–68
M. Chase, Multi-authority attribute based encryption, in Theory of Cryptography Conference (Springer, 2007), pp. 515–534
M.B.M. Kamel, P. Ligeti, C. Reich, Lamred: Location aware and privacy preserving multi layer resource discovery for iot. Acta Cybern. (2021)
M. El-Hajj, A. Fadlallah, M. Chamoun, A. Serhrouchni, A survey of internet of things (iot) authentication schemes. Sensors 19(5), 1141 (2019)
J. Weise, Public key infrastructure overview, in Sun BluePrints OnLine, August (2001), pp. 1–27
N. Hong, A security framework for the internet of things based on public key infrastructure, in Advanced Materials Research, vol. 671 (Trans Tech Publications, 2013), pp. 3223–3226
D. Wing, S. Cheshire, M. Boucadair, R. Penno, P. Selkirk, Port control protocol (pcp), in Internet Eng. Task Force, Fremont, CA, USA, RFC, vol. 6887 (2013)
M.B.M. Kamel, P. Ligeti, A. Nagy, Improved approach of address propagation for f2f networks, in Proceedings of the 2nd European Conference on Electrical Engineering and Computer Science (IEEE, 2018), pp. 604–609
M.B.M. Kamel, P. Ligeti, A. Nagy, C. Reich, “Distributed address table (dat): a decentralized model for end-to-end communication in iot. J. Peer-to-Peer Netw. Appl. (2021)
E.F. Kfoury, J. Gomez, J. Crichigno, E. Bou-Harb, D. Khoury, Decentralized distribution of pcp mappings over blockchain for end-to-end secure direct communications. IEEE Access 7, 110159–110173 (2019)
S. Ratnasamy, P. Francis, M. Handley, R. Karp, S. Shenker, A scalable content-addressable network, in Proceedings of the 2001 Conference on Applications, Technologies, Architectures, and Protocols for Computer Communications (2001), pp. 161–172
F. Paganelli, D. Parlanti, A dht-based discovery service for the internet of things. J. Comput. Netw. Commun. 2012 (2012)
S. Ramabhadran, S. Ratnasamy, J.M. Hellerstein, S. Shenker, Prefix hash tree: an indexing data structure over distributed hash tables, in Proceedings of the 23rd ACM Symposium on Principles of Distributed Computing, vol. 37 (2004)
E.K. Lua, J. Crowcroft, M. Pias, R. Sharma, S. Lim, A survey and comparison of peer-to-peer overlay network schemes. IEEE Commun. Surv. Tutor. 7(2), 72–93 (2005)
M.B.M. Kamel, P. Ligeti, C. Reich, Region-based distributed hash table for fog computing infrastructure, in 13th Joint Conference on Mathematics and Informatics (2020), pp. 82–83
M. Picone, M. Amoretti, F. Zanichelli, Geokad: a p2p distributed localization protocol, in 2010 8th IEEE International Conference on Pervasive Computing and Communications Workshops (PERCOM Workshops) (IEEE, 2010), pp. 800–803
S. Cirani, L. Davoli, G. Ferrari, R. Léone, P. Medagliani, M. Picone, L. Veltri, A scalable and self-configuring architecture for service discovery in the internet of things. IEEE Intern. Things J. 1(5), 508–521 (2014)
Acknowledgements
The research was supported by Application Domain Specific Highly Reliable IT Solutions project, which has been implemented with the support provided from the National Research, Development and Innovation Fund of Hungary, financed under the Thematic Excellence Programme TKP2020-NKA-06 (National Challenges Subprogramme) funding scheme, ÚNKP-20-3 New National Excellence Program of the Ministry for Innovation and Technology from the source of National Research, Development and Innovation Fund, SH programme and by the Ministry of Science, Research and the Arts Baden-Württemberg Germany.
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2022 The Author(s), under exclusive license to Springer Nature Singapore Pte Ltd.
About this paper
Cite this paper
Kamel, M.B.M., Ligeti, P., Reich, C. (2022). On Security and Performance Requirements of Decentralized Resource Discovery in IoT. In: Singh, P.K., Singh, Y., Chhabra, J.K., Illés, Z., Verma, C. (eds) Recent Innovations in Computing. Lecture Notes in Electrical Engineering, vol 855. Springer, Singapore. https://doi.org/10.1007/978-981-16-8892-8_22
Download citation
DOI: https://doi.org/10.1007/978-981-16-8892-8_22
Published:
Publisher Name: Springer, Singapore
Print ISBN: 978-981-16-8891-1
Online ISBN: 978-981-16-8892-8
eBook Packages: Intelligent Technologies and RoboticsIntelligent Technologies and Robotics (R0)