Abstract
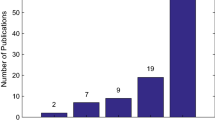
Computer software has been widely used in various industries, and many software cannot avoid receiving network attacks. The phenomena suggest that existing solutions for vulnerability detection demand improvement. This has motivated researchers to find and fix these vulnerabilities early. Deep learning is now widely used for vulnerability detection. Aiming at investigating the training efficiency of distinct neural network models, we leverage three datasets, covering 126 types of vulnerabilities. Each dataset is partitioned into three sets with a ratio of 6:2:2. Word2vec has been applied to transfer program code to vectors. Experiments results have shown that the DNN network achieved maximum efficiency.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Lin G, Xiao W, Zhang J et al (2020) Deep learning-based vulnerable function detection: a benchmark. In: Information and communications security
Li Z, Zou D, Xu S et al (2018) Vuldeepecker: A deep learning-based system for vulnerability detection. arXiv preprint arXiv:1801.01681
Lin G, Zhang J, Luo W et al (2018) Cross-project transfer representation learning for vulnerable function discovery. IEEE Trans Industr Inf 14(7):3289–3297
Harer JA, Kim LY, Russell RL et al (2018) Automated software vulnerability detection with machine learning. arXiv preprint arXiv:1803.04497
Lin G, Wen S, Han QL et al (2020) Software vulnerability detection using deep neural networks: a survey. Proc IEEE PP(99):1–24
Ghaffarian SM, Shahriari HR (2017) Software vulnerability analysis and discovery using machine-learning and data-mining techniques: a survey. Comput Surv (CSUR) 50(4):56
Zeng P, Lin G, Pan L et al (2020) Software vulnerability analysis and discovery using deep learning techniques: a survey. IEEE Access
Chen X, Li C, Wang D et al (2019) Android HIV: a study of repackaging malware for evading machine-learning detection. IEEE Trans Inf Forensics Secur 15:987–1001
Zhang J, Xiang Y, Wang Y et al (2012) Network traffic classification using correlation information. IEEE Trans Parallel Distrib Syst 24(1):104–117
Liu L, De Vel O, Han QL et al (2018) Detecting and preventing cyber insider threats: a survey. IEEE Commun Surv Tutorials 20(2):1397–1417
Kim S, Woo S, Lee H et al (2017) VUDDY: a scalable approach for vulnerable code clone discovery. In: 2017 IEEE Symposium on Security and Privacy (SP)
Li Z, Zou D, Xu S et al (2016) VulPecker: an automated vulnerability detection system based on code similarity analysis. In: Proceedings of the 32nd annual conference on computer security applications, pp 201–213
Rattan D, Bhatia R, Singh M (2013) Software clone detection: a systematic review. Inf Softw Technol 55(7):1165–1199
Peters M, Neumann M, Iyyer M et al (2018) Deep contextualized word representations
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2021 The Author(s), under exclusive license to Springer Nature Singapore Pte Ltd.
About this paper
Cite this paper
Yuan, X., Zeng, P., Tai, Y., Cheng, F. (2021). The Efficiency of Vulnerability Detection Based on Deep Learning. In: Yu, Z., Patnaik, S., Wang, J., Dey, N. (eds) Advancements in Mechatronics and Intelligent Robotics. Advances in Intelligent Systems and Computing, vol 1220. Springer, Singapore. https://doi.org/10.1007/978-981-16-1843-7_52
Download citation
DOI: https://doi.org/10.1007/978-981-16-1843-7_52
Published:
Publisher Name: Springer, Singapore
Print ISBN: 978-981-16-1842-0
Online ISBN: 978-981-16-1843-7
eBook Packages: Intelligent Technologies and RoboticsIntelligent Technologies and Robotics (R0)