Abstract
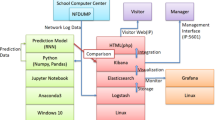
Network log data is essential to web administrator, which provides information such as, system error, cyberattack warning, mobile data gigabytes, message sending status, and so on. Managing the massive volume of log data give a challenge and an opportunity. It would be a challenge for administering large amounts of log data, and an opportunity to prevent future cyberattacks. In this paper, we aim to provide a network log data management, which can do visualization analyzing using Elasticsearch, Logstash, and Kibana (ELK Stack). In the ELK Stack technology, we can create filter, screen and analyze network log database on different purpose, and apply visualization effects on the web browser. Also, we propose a deep learning model using RNN for advanced network attack detection. From the model, we can learn the characteristics of each cyberattack by knowing network attack features and then cross-validation with the analysis information on the log system. Finally, we do the performance metric test using Grafana.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Kiran, M., Chhabra, A.: Understanding flows in high-speed scientific networks: a NetFlow data study. Future Gener. Comput. Syst. 94, 72–79 (2019)
Kozik, R.: Distributing extreme learning machines with Apache Spark for NetFlow-based malware activity detection. Pattern Recogn. Lett. 101, 14–20 (2018)
Wang, C.Y., et al.: BotCluster: a session-based P2P botnet clustering system on NetFlow. Comput. Netw. 145, 175–189 (2018)
Bin, L., et al.: A NetFlow based flow analysis and monitoring system in enterprise networks. Comput. Netw. 52(5), 1074–1092 (2008)
Carela-Español, V., et al.: Analysis of the impact of sampling on NetFlow traffic classification. Comput. Netw. 55(5), 1083–1099 (2011)
Appleyard, R., Adams, J.H.: Using the ELK stack for CASTOR application logging at RAL. In: 2015 International Symposium on Grids and Clouds, vol. 239. SISSA Medialab (2016)
Prakash, T., Kakkar, M., Patel, K.: Geo-identification of web users through logs using ELK stack. In: 2016 6th International Conference-Cloud System and Big Data Engineering (Confluence). IEEE (2016)
Xue, Q., Chuah, M.C.: New attacks on RNN based healthcare learning system and their detections. Smart Health 9, 144–157 (2018)
Liu, H., et al.: CNN and RNN based payload classification methods for attack detection. Knowl.-Based Syst. 163, 332–341 (2019)
Acknowledgment
This work was sponsored by the Ministry of Science and Technology (MOST), Taiwan, under Grant No. 107-2221-E-029-008 and 107-2218-E-029-003.
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2020 Springer Nature Singapore Pte Ltd.
About this paper
Cite this paper
Yang, CT., Jiang, WJ., Kristiani, E., Chan, YW., Liu, JC. (2020). The Implementation of a Network Log System Using RNN on Cyberattack Detection with Data Visualization. In: Hung, J., Yen, N., Chang, JW. (eds) Frontier Computing. FC 2019. Lecture Notes in Electrical Engineering, vol 551. Springer, Singapore. https://doi.org/10.1007/978-981-15-3250-4_38
Download citation
DOI: https://doi.org/10.1007/978-981-15-3250-4_38
Published:
Publisher Name: Springer, Singapore
Print ISBN: 978-981-15-3249-8
Online ISBN: 978-981-15-3250-4
eBook Packages: Intelligent Technologies and RoboticsIntelligent Technologies and Robotics (R0)