Abstract
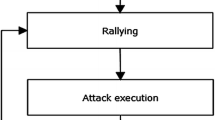
A botnet is a network of computing devices being commanded by an attacker, a daily Internet problem, causing extensive economic damage for organizations and individuals. With the avail of botnets, attackers can perform remote control on exploited machines, performing several malicious activities, since it enormously increases a botnet’s survivability by evading detection, Domain Name System (DNS) nowadays is a favourable botnet communication channel. Fortunately, many strategies have been introduced and developed to undertake the issue of botnets based on DNS resolving; this review explores the various botnet detection techniques through providing a study for detection approached based on DNS traffic analysis. Some related topics, including technological background, life cycle, evasion, and detection techniques of botnets are introduced.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Stevanovic M, Revsbech K, Pedersen J, Sharp R, Jensen C, A collaborative approach to botnet protection
Al-Ani AK, Anbar M, Manickam S, Al-Ani A (2018) DAD-match: technique to prevent DoS attack on duplicate address detection process in IPv6 link-local network. J Commun 13(6):317–324
Abu Rajab M, Zarfoss J, Monrose F, Terzis A (2006) Proceedings of the 6th ACM SIGCOMM on internet measurement—IMC’06 (2006), p 41. https://doi.org/10.1145/1177080.1177086. URL http://portal.acm.org/citation.cfm?doid=1177080.1177086
Canavan J (2005) The evolution of malicious IRC bots. In: Virus bulletin conference, pp 104–114
Khattak S, Ramay NR, Khan KR, Syed AA, Khayam SA (2014) IEEE Commun Surv Tutorials 16(2):898. https://doi.org/10.1109/SURV.2013.091213.00134
Cant’on David (2015) Botnet detection through DNS-based approaches—CERTSI. https://www.certsi.es/en/blog/botnet-detection-dns
Satam P, Alipour H, Al-Nashif Y, Hariri S (2015) J Internet Serv Inf Secur (JISIS) 5(4):85
Yadav S, Reddy AKK, Reddy AN, Ranjan S (2010) Proceedings of the 10th annual conference on internet measurement—IMC ’10, p 48. https://doi.org/10.1145/1879141.1879148
Holz T, Gorecki C, Rieck K, Freiling FC (2008) Measuring and detecting fast-flux service networks. In: NDSS
Stevanovic M, Pedersen JM, D’Alconzo A, Ruehrup S (2017) Int J Inf Secur 16(2):115. https://doi.org/10.1007/s10207-016-0331-3
Savage K, Symantec security response
Karim A, Salleh RB, Shiraz M, Shah SAA, Awan I, Anuar NB (2014) J Zhejiang Univ Sci C 15(11):943. https://doi.org/10.1631/jzus.C1300242
Morales C (2018) NETSCOUT Arbor confirms 1.7 Tbps DDoS Attack; The Terabit Attack Era is upon us https://asert.arbornetworks.com/netscout-arbor-confirms-1-7-tbps-ddos-attackterabit-attack-era-upon-us/. URL https://asert.arbornetworks.com/netscout-arbor-confirms-1-7-tbps-ddos-attack-terabit-attack-era-upon-us
Wielogorska M, O’Brien D (2017) DNS traffic analysis for botnet detection. In: 25th Irish conference on artificial intelligence and cognitive science, 7–8 Dec 2017, Dublin, Ireland
Ahluwalia A, Traore I, Ganame K, Agarwal N (2017) Lecture notes in computer science (including subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics) 10618 LNCS, 19. https://doi.org/10.1007/978-3-319-69155-8_2
Yadav S, Reddy AL (2012) Lecture notes of the institute for computer sciences, Social informatics and telecommunications engineering 96 LNICST, 446. https://doi.org/10.1007/978-3-642-31909-9_26
William Salusky, R. Danford. The Honeynet project, know your enemy: fast-flux service networks [Internet]. https://www.honeynet.org/papers/ff. URL https://www.honeynet.org/papers/ff
Stone-Gross B, Cova M, Gilbert B, Kemmerer R, Kruegel C, Vigna G (2011) IEEE Secur Priv 9(1):64. https://doi.org/10.1109/MSP.2010.144
Luo X, Wang L, Xu Z, Yang J, Sun M, Wang J (2017) ACM international conference proceeding series, Part F1280, 47. https://doi.org/10.1145/3057109.3057112
Grill M, Nikolaev I, Valeros V, Rehak M (2015) Proceedings of the 2015 IFIP/IEEE international symposium on integrated network management, IM 2015. https://doi.org/10.1109/inm.2015.7140486
Antonakakis M, Perdisci R (2012) Proceedings of the 21st USENIX security symposium, p 16. URL https://www.usenix.org/system/files/conference/usenixsecurity12/sec12-final127.pdf
Truong DT, Cheng G (2016) Secur Commun Netw 9(14):2338. https://doi.org/10.1002/sec.1495
Kolias C, Kambourakis G, Stavrou A, Voas J (2017) Computer 50(7):80. https://doi.org/10.1109/MC.2017.201
Abdullah R, Abdollah M (2013) IJCSI Int J Comput Sci Issues 10(2):208
Manasrah AM, Hasan A, Abouabdalla OA, Ramadass S (2009) Detecting botnet activities based on abnormal DNS traffic. arXiv preprint arXiv:0911.0487
Liu L, Chen S, Yan G, Zhang Z (2008) Bottracer: execution-based bot-like malware detection. In: International conference on information security. Springer, Berlin, Heidelberg, pp 97–113
Silva SS, Silva RM, Pinto RC, Salles RM (2013) Comput Netw 57(2):378. https://doi.org/10.1016/j.comnet.2012.07.021
da Pedro Marques Luz P (2014) Botnet detection using passive DNS. Ph.D. thesis
Zeidanloo HR, Shooshtari MJZ, Amoli PV, Safari M, Zamani M (2010) Proceedings—2010 3rd IEEE international conference on computer science and information technology, ICCSIT 2010, vol 2(May), p 158. https://doi.org/10.1109/iccsit.2010.5563555
Dornseif M, Gärtner FC, Holz T (2004) Vulnerability assessment using honeypots. Praxis der Informationsverarbeitung und Kommunikation 27(4):195–201
Freiling FC, Holz T, Wicherski G (2005) Lecture notes in computer science (including subseries. Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics) 3679 LNCS, p 319. https://doi.org/10.1007/11555827_19
Gaonjur P, Bokhoree C (2006) School of Business Informatics, University of Technology, Mauritius (May)
Kumar S, Sehgal RK, Chamotra S (2016) Proceedings—2016 2nd international conference on computational intelligence and communication technology, CICT 2016, pp 6–13. https://doi.org/10.1109/cict.2016.12
Oberheide J, Karir M, Mao ZM (2007) Characterizing dark dns behavior. In: International conference on detection of intrusions and malware, and vulnerability assessment. Springer, Berlin, Heidelberg, pp 140–156
Aiello M, Mongelli M, Papaleo G (2015) Int J Commun Syst 28(14):1987. https://doi.org/10.1002/dac.2836
Bethencourt J, Franklin J, Vernon MK (2005) Mapping internet sensors with probe response attacks. In: USENIX security symposium, pp 193–208
Peng S, Yu (2009) Proceedings of the 3rd Hackers’ workshop on computer and internet security (IITKHACK’09), 2(2), 2. https://doi.org/10.1145/1327452.1327492
Ramachandran A, Feamster N, Dagon D (2006) Proceedings of the 2nd conference on steps to reducing unwanted traffic on the internet, vol 2, 36, 8. https://doi.org/10.1109/tdsc.2008.35
Shin S, Xu Z, Gu G (2012) Proceedings—IEEE INFOCOM, pp 2846–2850. https://doi.org/10.1109/infcom.2012.6195713
Ma X, Zhang J, Li Z, Li J, Tao J, Guan X, Lui JC, Towsley D (2015) J Netw Comput Appl 47:72. https://doi.org/10.1016/j.jnca.2014.09.016
Alieyan K, Almomani A, Manasrah A, Kadhum MM (2017) Neural Comput Appl 28(7):1541. https://doi.org/10.1007/s00521-015-2128-0
Passerini E, Paleari R, Martignoni L, Bruschi D (2008) Fluxor: detecting and monitoring fast-flux service networks. In: International conference on detection of intrusions and malware, and vulnerability assessment. Springer, Berlin, Heidelberg, pp 186–206
Perdisci R, Corona I, Dagon D, Lee W (2009) Proceedings—Annual computer security applications conference, ACSAC, pp 311–320. https://doi.org/10.1109/acsac.2009.36
Zdrnja B, Brownlee N, Wessels D (2007) Passive monitoring of DNS anomalies. In: International conference on detection of intrusions and malware, and vulnerability assessment. Springer, Berlin, Heidelberg, pp 129–139
Weimer F (2005) Passive DNS replication. In: FIRST conference on computer security incident, p 98
Antonakakis M, Perdisci R, Dagon D, Lee W, Feamster N (2010) USENIX Security’10: proceedings of the 19th USENIX conference on security, pp 1–17. https://doi.org/10.1145/2584679. URL http://www.usenix.org/events/sec10/tech/fullpapers/Antonakakis.pdf
Kheir N, Tran F, Caron P, Deschamps N (2016) PositiveM, D.N.S. reputation, S.o. Benign, C.B.N. Cuppens-boulahia, F. Cuppens, pp 0–14
Bilge L, Kirda E, Kruegel C, Balduzzi M, Antipolis S (2011) Ndss pp 1–17. https://doi.org/10.1145/2584679
Li X, Wang J, Zhang X (2017) Future Internet 9(4), 1. https://doi.org/10.3390/fi9040055
Antonakakis M, Perdisci R, Lee W, Ii NV, Dagon D (2011) USENIX security symposium. 11, 1. DOI 2028067.2028094. URL https://dl.acm.org/citation.cfm?id=2028094
Acknowledgements
This research was supported by the Short Term Research Grant, Universiti Sains Malaysia (USM) No: 304/PNAV/6313332.
Author information
Authors and Affiliations
Corresponding authors
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2019 Springer Nature Singapore Pte Ltd.
About this paper
Cite this paper
Al-Mashhadi, S., Anbar, M., Karuppayah, S., Al-Ani, A.K. (2019). A Review of Botnet Detection Approaches Based on DNS Traffic Analysis. In: Piuri, V., Balas, V., Borah, S., Syed Ahmad, S. (eds) Intelligent and Interactive Computing. Lecture Notes in Networks and Systems, vol 67. Springer, Singapore. https://doi.org/10.1007/978-981-13-6031-2_21
Download citation
DOI: https://doi.org/10.1007/978-981-13-6031-2_21
Published:
Publisher Name: Springer, Singapore
Print ISBN: 978-981-13-6030-5
Online ISBN: 978-981-13-6031-2
eBook Packages: Intelligent Technologies and RoboticsIntelligent Technologies and Robotics (R0)