Abstract
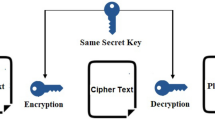
The traditional cipher techniques employ the use of limited keys for asymmetric and symmetric cryptography. Most of the encoding schemes use single key function to encrypt the critical data before transmitting it over an insecure network. Increasing the number of keys and number of encryption functions increases the strength of a symmetric technique. This paper presents a symmetric key technique that uses five keys for encryption and decryption.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Farouzan BA (2007) Cryptography and network security. McGraw-Hill Special Indian Edition 2007
Stallings W (2007) Cryptography and network security-principles and practices, 4th edn. Pearson, Upper Saddle River
Johari R, Bhatia H, Singh S, Chauhan M (2016) Triplicative cipher technique. Procedia Comput Sci 78:217–223
Singh L, Johari R (2015) CLCT: cross language cipher technique. In: International symposium on security in computing and communication. Springer International Publishing, pp. 217–227
Jain I, Johari R, Ujjwal RL (2014) CAVEAT: credit card vulnerability exhibition and authentication tool. In: Second international symposium on security in computing and communications (SSCC14), pp 391–399. Springer, Berlin
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2019 Springer Nature Singapore Pte Ltd.
About this paper
Cite this paper
Garg, N., Bhatia, H., Johari, R. (2019). Pentaplicative Cipher Technique. In: Bhattacharyya, S., Hassanien, A., Gupta, D., Khanna, A., Pan, I. (eds) International Conference on Innovative Computing and Communications. Lecture Notes in Networks and Systems, vol 55. Springer, Singapore. https://doi.org/10.1007/978-981-13-2324-9_24
Download citation
DOI: https://doi.org/10.1007/978-981-13-2324-9_24
Published:
Publisher Name: Springer, Singapore
Print ISBN: 978-981-13-2323-2
Online ISBN: 978-981-13-2324-9
eBook Packages: Intelligent Technologies and RoboticsIntelligent Technologies and Robotics (R0)