Abstract
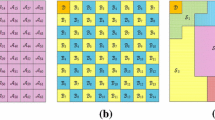
Images published on online social sites such as Facebook are increasingly prone to be misused for malicious purposes. However, existing image forensic research assumes that the investigator can confiscate every piece of evidence and hence overlooks the fact that the original image is difficult to obtain. Because Facebook applies a Discrete Cosine Transform (DCT)-based compression on uploaded images, we are able to detect the modified images which are re-uploaded to Facebook. Specifically, we propose a novel method to effectively detect the presence of double compression via the spatial domain of the image: We select small image patches from a given image, define a distance metric to measure the differences between compressed images, and propose an algorithm to infer whether the given image is double compressed without referring to the original image. To demonstrate the correctness of our algorithm, we correctly predict the number of compressions being applied to a Facebook image.
Access provided by Autonomous University of Puebla. Download to read the full chapter text
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
Ardizzone, E., Bruno, A., Mazzola, G.: Copy-Move Forgery Detection via Texture Description. In: Proceedings of the 2nd ACM Workshop on Multimedia in Forensics, Security and Intelligence (2010)
Bianchi, T., Piva, A.: Analysis of Non-Aligned Double JPEG Artifacts for the Localization of Image Forgeries. In: Proceedings of the IEEE International Workshop on Information Forensics and Security (WIFS), pp. 1–6 (2011)
Fei, P., Xi-lan, W.: Digital Image Forgery Forensics by Using Blur Estimation and Abnormal Hue Detection. In: Proceedings of the Symposium on Photonics and Optoelectronic (SOPO), pp. 1–4 (2010)
Hou, W., Ji, Z., Jin, X., Li, X.: Double JPEG Compression Detection Base on Extended First Digit Features of DCT Coefficients. International Journal of Information and Education Technology 3(5), 512–515 (2013)
Huang, F., Huang, J., Shi, Y.: Detecting Double Compression with the Same Quantization Matrix. IEEE Transactions on Information Forensics and Security 5(4), 848–856 (2010)
Khan, S., Kulkarni, A.: Robust Method for Detection of Copy-Move Forgery in Digital Images. In: Proceedings of the International Conference on Signal and Image Processing (ICSIP), pp. 69–73 (2010)
Liu, Q., Li, X., Cooper, P., Hu, X.: Shift-Recompression-Based Feature Mining for Detecting Content-Aware Scaled Forgery in JPEG Images. In: Proceedings of the 12th International Workshop on Multimedia Data Mining (MDMKDD), pp. 10–16 (2012)
Lukàš, J., Fridrich, J.: Estimation of Primary Quantization Matrix in Double Compressed JPEG Images. In: Proceedings of the Digital Forensic Research Workshop (2003)
Popescu, A.: Statistical Tools for Digital Image Forensics. Ph.D. thesis, Department of Computer Science, Dartmouth College, Hanover, PhD thesis (2005)
Qu, Z., Luo, W., Huang, J.: Identifying Shifted Double JPEG Compression Artifacts for Non-intrusive Digital Image Forensics. In: Hu, S.-M., Martin, R.R. (eds.) CVM 2012. LNCS, vol. 7633, pp. 1–8. Springer, Heidelberg (2012)
Sencar, H., Memon, N.: Overview of State-of-the-art in Digital Image Forensics. Statistical Science and Interdisciplinary Research, pp. 1–19 (2008)
Thing, V., Chen, Y., Cheh, C.: An Improved Double Compression Detection Method for JPEG Image Forensics. In: Proceedings of the IEEE International Symposium on Multimedia, pp. 290–297 (2012)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2014 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
NG, A., Pan, L., Xiang, Y. (2014). A Novel Method for Detecting Double Compressed Facebook JPEG Images. In: Batten, L., Li, G., Niu, W., Warren, M. (eds) Applications and Techniques in Information Security. ATIS 2014. Communications in Computer and Information Science, vol 490. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-662-45670-5_18
Download citation
DOI: https://doi.org/10.1007/978-3-662-45670-5_18
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-662-45669-9
Online ISBN: 978-3-662-45670-5
eBook Packages: Computer ScienceComputer Science (R0)