Abstract
Radio frequency identification (RFID) networks are an emerging type of network that is posed to play an important role in the Internet-of-Things (IoT). One of the most critical issues facing RFID networks is that of security. Unlike conventional networks, RFID networks are characterized by the use of computationally weak RFID tags. These tags come with even more stringent resource constraints than the sensors used in sensor networks. In this chapter, we study the security aspects of RFID networks and communications. We begin by introducing the main security threats, followed by a discussion of various security mechanisms used to protect RFID networks. We conclude by studying the security mechanism of an actual large scale RFID deployment.
Access provided by Autonomous University of Puebla. Download to read the full chapter text
Chapter PDF
Similar content being viewed by others
Keywords
- Security Requirement
- Unauthorized Access
- International Civil Aviation Organization
- Distance Bounding Protocol
- Financial Cryptography
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
Gershenfeld N, Krikorian R, Cohen D (2004) The Internet of Things. Scientific American 291: 76–81.
Koscher K, Juels A, Kohno T, Brajkovic V (2009) EPC RFID Tags in Security Applications: Passport Cards, Enhanced Drivers Licenses, and Beyond. In Proceedings of the 2009 ACM Conference on Computer and Communications Security (CCS’09), pp. 33–42.
Kargoth G, Moskowitz P A (2005) Disabling RFID tags with visible confirmation: clipped tags are silenced. In Proceedings of the 2005 ACM workshop on Privacy in the electronic society (WPES’05), pp. 27–30.
Moskowitz P A, Lauris A, Morris S (2007) A Privacy-Enhancing Radio Frequency Identification Tag: Implementation of the Clipped Tag. In Proceedings of the 2007 IEEE International Conference on Pervasive Computing and Communications Workshops (PerCom’07), pp. 348–351.
Juels A, Rivest R, Szydlo M (2003) The Blocker Tag: Selective Blocking of RFID Tags for Consumer Privacy. In Proceedings of the 2003 ACM Conference on Computer and Communication Security (CCS’03), pp. 103–111.
Floerkemeier C, Roland S, Marc L (2004) Scanning with a Purpose-Supporting the Fair Information Principles in RFID Protocols. International Symposium on Ubiquitous Computing Systems.
Rieback M R, Crispo B, Tanenbaum A S (2005) RFID Guardian: A Battery-Powered Mobile Device for RFID Privacy Management. Australasian Conference on Information Security and Privacy.
Juels A, Ravikanth P (2003) Squealing Euros Privacy Protection in RFIDEnabled Banknotes. Financial Cryptography and Data Security, 2742: 103–121.
Cai S, Li Y, Li T, Deng R H, Yao H (2010) Achieving High Security and Efficiency in RFID-tagged Supply Chains. International Journal of Applied Cryptography 2(1): 3–12.
Avoine G (2011) RFID Security & Privacy Lounge. http://www.avoine.net/ rfid/. Accessed 14 June, 2011.
Alomair B, Poovendran R (2010) Privacy versus Scalability in Radio Frequency Identification Systems. Computer Communication, Elsevier, 33(18): 2155–2163.
Tsudik G (2006) YA-TRAP: Yet Another Trivial RFID Authentication Protocol. International Conference on Pervasive Computing and Communication.
Chatmon C, Tri van L, Burmester M (2006) Secure Anonymous RFID Authentication Protocols. Florida State University Technical Report. http:// www.cs.fsu.edu/~burmeste/TR-060112.pdf. Accessed 9 December, 2010.
Tsudik G (2007) A Family of Dunces: Trivial RFID Identification and Authentication Protocols. In Proceedings of the 7th International Conference on Privacy Enhancing Technologies (PET’07), pp. 45–61.
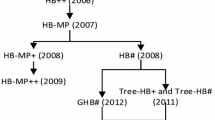
Hopper N J, Blum M (2001) “Secure Human Identification Protocols.” International Conference on Theory and Application of Cryptology and Information Security (ASIACRYPT).
Juels A, Weis S (2005) Authenticating Pervasive Devices with Human Protocols. Advances in Cryptology (CRYPTO).
Piramuthu S (2006) HB and Related Lightweight Authentication Protocols for Secure RFID Tag/Reader Authentication. Collaborative Electronic Commerce Technology and Research.
Holcom D, Burleson W, Fu K (2007). Initial SRAM state as a Fingerprint and Source of True Random Numbers for RFID Tags. Conference on RFID Security.
Melia-Seguil J, Garcia-Alfaro J, Herrera-Joancomarti J (2010) Analysis and improvement of a pseudorandom number generator for EPC Gen2 tags. International Workshop on Lightweight Cryptography for Resource-Constrained Devices.
Peris-Lopez P, Millan E S, van der Lubbe JCA, Entrena L A (2010) Cryptographically secure pseudo-random bit generator for RFID tags. International Conference for Internet Technology and Secured Transactions.
Tan C C, Sheng B, Li Q (2010) Efficient techniques for monitoring missing RFID tags. IEEE Transactions on Wireless Communication 9(6): 1882–1889.
Tan C C, Sheng B, Li Q (2008) Secure and Serverless RFID Authentication and Search Protocols. IEEE Transactions on Wireless Communication 7(4): 1400–1407.
Hancke G P, Kuhn M (2005) An RFID Distance Bounding Protocol. Conference on Security and Privacy for Emerging Areas in Communication Networks.
Avoine G, Muhammed A B, Suleyman K, Cédric L, Benjamin M (2010) A Framework for Analyzing RFID Distance Bounding Protocols. J. Comput. Secur. 19(2): 289–317.
Kim C H, Avoine G (2009) RFID Distance Bounding Protocol with Mixed Challenges to Prevent Relay Attacks. International Conference on Cryptology And Network Security.
Capkun S, El Defrawy K, Tsudik G (2010) GDB: Group Distance Bounding Protocols. arXiv.org, http://arxiv.org/abs/1011.5295. Accessed 15 January, 2011.
Bolotnyy L, Gabriel R (2009) Generalized “Yoking-Proofs” and Inter-tag Communication. In Development and Implementation of RFID Technology. I-Tech Education and Publishing.
Juels A (2004) “Yoking-Proofs” for RFID Tags. International Workshop on Pervasive Computing and Communication Security.
Burmester M, de Medeiros B, Motta R (2008) Provably Secure Grouping-Proofs for RFID Tags. Smart Card Research and Advanced Applications (CARDIS).
Garcia F, Koning G G, Muijrers R, Rossum P, Verdult R, Schreur R W, Jacobs B (2008) Dismantling MIFARE Classic. European Symposium on Research in Computer Security (ESORICS).
Kasper T, Silbermann M, Paar C (2010) All You Can Eat or Breaking a Real-World Contactless Payment System. Financial Cryptography and Data Security. 6052: 343–350.
Nohl K, Evans D, Starbug, Plotz H (2008) Reverse-Engineering a Cryptographic RFID Tag. USENIX Security Symposium.
International Civil Aviation Organization (2009). Doc 9303 Part 1 Vol 1 and 2. http://www2.icao.int/en/MRTD/Pages/Downloads.aspx. Accessed 15 January 2011. Accessed 15 January, 2011.
Chothia T, Smirnov V (2010) A Traceability Attack against e-Passports. Financial Cryptography and Data Security, 6052: 20–34.
Juels A, Molnar D, Wagner D (2005) Security and Privacy Issues in Epassports. Conference on Security and Privacy for Emerging Areas in Communication Networks.
Avoine G, Kassem K, Jean-Jacques Q (2008) ePassport: Securing International Contacts with Contactless Chips. Financial Cryptography and Data Security, 5143: 141–155.
Liu Y, Kasper T, Lemke-Rust K, Paar C (2007) E-Passport: Cracking Basic Access Control Keys. OTM confederated international conference on the move to meaningful Internet systems: CoopIS, DOA, ODBASE, GADA, and IS — Volume Part II.
Author information
Authors and Affiliations
Rights and permissions
Copyright information
© 2013 Higher Education Press, Beijing and Springer-Verlag Berlin Heidelberg
About this chapter
Cite this chapter
Tan, C.C., Wu, J. (2013). Security in RFID Networks and Communications. In: Wireless Network Security. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-36511-9_10
Download citation
DOI: https://doi.org/10.1007/978-3-642-36511-9_10
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-36510-2
Online ISBN: 978-3-642-36511-9
eBook Packages: Computer ScienceComputer Science (R0)