Abstract
Despite their advantages and ease of deployment, mobile wireless networks (MANETs) have security weaknesses due to their limited resources and mobile nature. They are vulnerable to many attacks, including the black hole attack, which has become difficult to detect accurately by traditional systems that rely on a single layer to identify malicious nodes. For example, the packet drop rate criterion at the network layer is not sufficient to identify malicious nodes, because sometimes packet drops are due to network conditions and not malicious action.
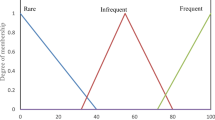
To meet these challenges, it has become necessary to design a more accurate system to detect this type of attack by exploiting information extracted from several layers of the OSI model. This paper proposes the design of a cross layer intrusion detection system to mitigate black hole attacks in mobile wireless networks. The proposed approach consists of two levels. At the first level, data extracted from multiple layers is used as input to the fuzzy logic system to determine the nature of a particular node (malicious node, normal node or suspicious node). At the second level, if a node is suspicious, Dempster-Shafer theory will be applied to verify that node.
The proposed approach, evaluated using the NS2 simulator, proves effective in detecting and isolating the malicious node.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Chlamtac, I., Conti, M., Liu, J.J.-N.: Mobile ad hoc networking: imperatives and challenges. Ad Hoc Netw. 1(1), 13–64 (2003)
De Morais Cordeiro, C., Agrawal, D.P.: Mobile ad hoc networking. Center for Distributed and Mobile Computing, pp. 1–63 (2002)
Hoebeke, J., Moerman, I., Dhoedt, B., Demeester, P.: An overview of mobile ad hoc networks: applications and challenges. J. Commun. Netw. 3(3), 60–66 (2004)
Mishra, A., Nadkarni, K.M.: Security in wireless ad hoc networks. In: The Handbook of Ad Hoc Wireless Networks, pp. 499–549. CRC Press, Boca Raton (2003)
Li, Y., Wei., J.: Guidelines on selecting intrusion detection methods in MANET. In: Proceedings of the Information Systems Educators Conference (2004)
Wu, B., Chen, J., Wu, J., Cardei, M.: A survey of attacks and countermeasures in mobile ad hoc networks. Department of Computer Science and Engineering, Florida Atlantic University (2007)
John Felix, C.F., Das, A., Seet, B.C., Lee, B.S.: Cross layer versus single layer approaches for intrusion detection in MANET. In: IEEE International Conference on Networks, Adelaide, pp. 194–199 (2007)
Liu, Y., Li, Y., Man, H.: A distributed cross-layer intrusion detection system for ad hoc networks. Ann. Telecommun. 61, 357–378 (2006). https://doi.org/10.1007/BF03219912
Parker, J., Patwardhan, A., Joshi, A.: Cross-layer analysis for detecting wireless misbehavior. In: 3rd IEEE Consumer Communications and Networking Conference, CCNC 2006, vol. 1. IEEE (2006)
Joseph, J.F.C., Das, A., Lee, B.S., Seet, B.C.: CARRADS: cross layer based adaptive real-time routing attack detection system for MANETS. Comput. Netw. 54, 1126–1141 (2010)
Suresh Babu, K., Chandra Sekharaiah, K.: CLDASR: cross layer based detection and authentication in secure routing in MANET. IRACST Int. J. Comput. Netw. Wirel. Commun. (IJCNWC) 4(2) (2014). ISSN: 2250-3501
Poongothai, T., Duraiswamy, K.: Cross layer intrusion detection system of mobile ad hoc networks using feature selection approach. WSEAS Trans. Commun. 13, 71–79 (2014). Art. #8. ISSN/E-ISSN: 1109-2742/2224-2864
Sharmasth Vali, Y., Rangaswamy, T.R.: An efficient cross-layer based intrusion detection system for mobile ad hoc networks. J. Theor. Appl. Inf. Technol. 95(1), 47 (2017)
Ns-2: The Network Simulator (2010). http://isi.edu/nsnam/ns/
Shrestha, R., et al.: A novel cross layer intrusion detection system in MANET. In: 2010 24th IEEE International Conference on Advanced Information Networking and Applications. IEEE (2010)
Sharma, S., Mishra, R.: A cross layer approach for intrusion detection in MANETs. Int. J. Comput. Appl. 93(9), 34–41 (2014)
Shurman, M.M., et al.: An enhanced cross-layer approach based on fuzzy-logic for securing wireless ad-hoc networks from black hole attacks (2017)
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2023 The Author(s), under exclusive license to Springer Nature Switzerland AG
About this paper
Cite this paper
Mekadem, L., Bourenane, M. (2023). Design of a Cross Layer Intrusion Detection System for Mobile Ad Hoc Networks to Mitigate Black Hole Attack. In: Abraham, A., Hanne, T., Gandhi, N., Manghirmalani Mishra, P., Bajaj, A., Siarry, P. (eds) Proceedings of the 14th International Conference on Soft Computing and Pattern Recognition (SoCPaR 2022). SoCPaR 2022. Lecture Notes in Networks and Systems, vol 648. Springer, Cham. https://doi.org/10.1007/978-3-031-27524-1_10
Download citation
DOI: https://doi.org/10.1007/978-3-031-27524-1_10
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-031-27523-4
Online ISBN: 978-3-031-27524-1
eBook Packages: Intelligent Technologies and RoboticsIntelligent Technologies and Robotics (R0)