Abstract
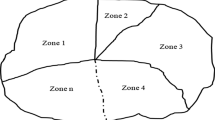
The risk assessment process is one of the most important tasks that must be performed on critical infrastructure systems to detect security vulnerabilities and risks. The risk assessment task is used to evaluate the likelihood and the impact of the potential threats on the critical assets of any system by determining the threats, the unwanted incidents, and the mitigation techniques to reduce these risks. The advanced metering infrastructure (AMI) system is considered one of the critical infrastructure systems and part of the smart grid system. AMI collects electricity consumption data from the customer’s residence to the electricity data center through bidirectional communication channels to be analyzed. This paper conducts a risk assessment process on the AMI system using the CORAS risk assessment model and CORAS risk assessment tool v1.4 to identify possible risks. The study applies the eight steps of the CORAS model to the AMI system from determining the critical assets in the AMI system to determining the mitigation techniques that can be applied to overcome the existing security vulnerabilities. In the end, this study provides a better understanding of the AMI security risks toward identifying adequate security perimeters for AMI systems.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Peppanen, J., Reno, M.J., Thakkar, M., Grijalva, S., Harley, R.G.: Leveraging AMI data for distribution system model calibration and situational awareness. IEEE Trans. Smart Grid 6(4), 2050–2059 (2015)
Rashed Mohassel, R., Fung, A., Mohammadi, F., Raahemifar, K.: A survey on advanced metering infrastructure. Int. J. Electric. Power Energy Syst. 63, 473–484 (2014)
Faisal, M.A., Aung, Z., Williams, J.R., Sanchez, A.: Data-stream-based intrusion detection system for advanced metering infrastructure in smart grid: a feasibility study. IEEE Syst. J. 9(1), 31–44 (2015)
Awad, A.I., Furnell, S., Paprzycki, M., Sharma, S.K.: Security in Cyber-Physical Systems: Foundations and Applications. Springer (2021)
Shokry, M., Awad, A.I., Abd-Ellah, M.K., Khalaf, A.A.: Systematic survey of advanced metering infrastructure security: vulnerabilities, attacks, countermeasures, and future vision. Futur. Gener. Comput. Syst. 136, 358–377 (2022)
Wangen, G.: Information security risk assessment: a method comparison. Computer 50(4), 52–61 (2017)
Faris, S., Ghazouani, M., Medromi, H., Sayouti, A.: Information security risk assessment-A practical approach with a mathematical formulation of risk. Int. J. Comput. Appl. 103(8), 36–42 (2014)
Ali, B., Awad, A.I.: Cyber and physical security vulnerability assessment for IoT-based smart homes. Sensors 18(3), 817 (2018)
Hashim, N.A., Abidin, Z.Z., Zakaria, N.A., Ahmad, R., Puvanasvaran, A.: Risk assessment method for insider threats in cyber security: a review. Int. J. Adv. Comput. Sci. Appl. 9(11) (2018)
McHenry, M.P.: Technical and governance considerations for advanced metering infrastructure/smart meters: Technology, security, uncertainty, costs, benefits, and risks. Energy Policy 59, 834–842 (2013)
Line, M.B., Johansen, G., et al.: Assessing information security risks of AMI: what makes it so difficult? In: 2015 International Conference on Information Systems Security and Privacy (ICISSP), pp. 56–63 (2015)
Habash, R.W., Groza, V., Krewski, D., Paoli, G.: A risk assessment framework for the smart grid. In: 2013 IEEE Electrical Power & Energy Conference, pp. 1–6 (2013)
Haider, M.H., Saleem, S.B., Rafaqat, J., Sabahat, N.: Threat modeling of wireless attacks on advanced metering infrastructure. In: 2019 13th International Conference on Mathematics, Actuarial Science, Computer Science and Statistics (MACS), pp. 1–6 (2019)
Pedramnia, K., Rahmani, M.: Survey of DoS attacks on LTE infrastructure used in AMI system and countermeasures. In: 2018 Smart Grid Conference (SGC), pp. 1–6 (2018)
Ghasempour, A.: Optimized advanced metering infrastructure architecture of smart grid based on total cost, energy, and delay. In: 2016 IEEE Power Energy Society Innovative Smart Grid Technologies Conference (ISGT), pp. 1–6 (2016)
Erdogan, G., Refsdal, A.: A method for developing qualitative security risk assessment algorithms. In: International Conference on Risks and Security of Internet and Systems, pp. 244–259. Springer (2017)
Gritzalis, D., Stergiopoulos, G., Vasilellis, E., Anagnostopoulou, A.: Readiness exercises: are risk assessment methodologies ready for the cloud? In: Advances in Core Computer Science-Based Technologies, pp. 109–128. Springer (2021)
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2023 The Author(s), under exclusive license to Springer Nature Switzerland AG
About this paper
Cite this paper
Shokry, M., Awad, A.I., Abd-Ellah, M.K., Khalaf, A.A.M. (2023). CORAS Model for Security Risk Assessment in Advanced Metering Infrastructure Systems. In: Hassanien, A.E., Snášel, V., Tang, M., Sung, TW., Chang, KC. (eds) Proceedings of the 8th International Conference on Advanced Intelligent Systems and Informatics 2022. AISI 2022. Lecture Notes on Data Engineering and Communications Technologies, vol 152. Springer, Cham. https://doi.org/10.1007/978-3-031-20601-6_39
Download citation
DOI: https://doi.org/10.1007/978-3-031-20601-6_39
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-031-20600-9
Online ISBN: 978-3-031-20601-6
eBook Packages: Intelligent Technologies and RoboticsIntelligent Technologies and Robotics (R0)