Abstract
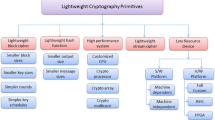
The Internet of Things (IoT) is the collection of everyday smart devices which connect to the Cloud, often through Fog nodes, to transmit and receive information. These everyday devices are distinct from traditional computers because they typically have notable constraints on their RAM, flash memory, and computational power. Due to these constraints, we believe that many of the proposed encryption schemes are too heavyweight to be employed in the IoT. In this paper we present a lightweight, flexible encryption scheme that relies on the one-way information loss property of a secure hash function. Our scheme imposes minimal computational and storage requirements, and imposes no non-negligible burdens on the encrypting device, except for the hash itself. We find that the encryption algorithm is particularly lightweight, and holds up strongly in terms of its speed and memory efficiency.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Neshenko, N., Bou-Harb, E., Crichigno, J., Kaddoum, G., Ghani, N.: Demystifying IoT security: an exhaustive survey on IoT vulnerabilities and a first empirical look on internet-scale IoT exploitations. IEEE Commun. Surv. Tutor. 21(3), 2702–2733 (2019)
Alaba, F.A., Othman, M., Hashem, I.A.T., Alotaibi, F.: Internet of Things security: a survey. J. Netw. Comput. Appl. 88, 10–28 (2017)
Mosenia, A., Jha, N.K.: A comprehensive study of security of Internet-of-Things. IEEE Trans. Emerg. Top. Comput. 5(4), 586–602 (2017)
Buchanan, W.J., Li, S., Asif, R.: Lightweight cryptography methods. J. Cyber Secur. Technol. 1(3–4), 187–201 (2017)
Latif, M.A., Ahmad, M.B., Khan, M.K.: A review on key management and lightweight cryptography for IoT. In: Global Conference on Wireless and Optical Technologies (GCWOT), pp. 1–7 (2020)
O’Mahony, D., Peirce, M., Tewari, H.: Electronic Payment Systems for E-Commerce, 2nd edn., p. 345. Artech House Publishers, Boston/London (2001)
Adeel, A., et al.: A multi-attack resilient lightweight IoT authentication scheme. Trans. Emerg. Telecommun. Technol. (2019). https://doi.org/10.1002/ett.3676
Yao, X., Chen, Z., Tian, Y.: A lightweight attribute-based encryption scheme for the Internet of Things. Future Gener. Comput. Syst. 49, 104–112 (2014)
Abdmeziem, M.R., Tandjaoui, D.: An end-to-end secure key management protocol for e-health applications. Comput. Electr. Eng. 44, 184–197 (2015)
Balasch, J., et al.: Compact implementation and performance evaluation of hash functions in ATtiny devices. In: Mangard, S. (ed.) CARDIS 2012. LNCS, vol. 7771, pp. 158–172. Springer, Heidelberg (2013). https://doi.org/10.1007/978-3-642-37288-9_11
Peyravian, M., et al.: Hash-based encryption system. Comput. Secur. 18(4), 345–350 (1999). https://doi.org/10.1016/s0167-4048(99)80080-7
Vinayaga Sundaram, B., Ramnath, M., Prasanth, M., Varsha Sundaram, J.: Encryption and hash based security in Internet of Things. In: 2015 3rd International Conference on Signal Processing, Communication and Networking (ICSCN), pp. 1–6 (2015). https://doi.org/10.1109/ICSCN.2015.7219926
Alrawais, A., Alhothaily, A., Hu, C., Cheng, X.: Fog computing for the internet of things: security and privacy issues. IEEE Internet Comput. 21(2), 34–42 (2017)
Aumasson, J.-P., Neves, S., Wilcox-O’Hearn, Z., Winnerlein, C.: BLAKE2: simpler, smaller, fast as MD5. In: Jacobson, M., Locasto, M., Mohassel, P., Safavi-Naini, R. (eds.) ACNS 2013. LNCS, vol. 7954, pp. 119–135. Springer, Heidelberg (2013). https://doi.org/10.1007/978-3-642-38980-1_8
Minematsu, K., Lucks, S., Morita, H., Iwata, T.: Attacks and security proofs of EAX-Prime. In: Moriai, S. (ed.) FSE 2013. LNCS, vol. 8424, pp. 327–347. Springer, Heidelberg (2014). https://doi.org/10.1007/978-3-662-43933-3_17
The Arduino Team, “Memory”, Arduino Website. https://www.arduino.cc/en/Tutorial/Foundations/Memory
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2023 The Author(s), under exclusive license to Springer Nature Switzerland AG
About this paper
Cite this paper
Chun, M., Weber, S., Tewari, H. (2023). A Lightweight Encryption Scheme for IoT Devices in the Fog. In: Arai, K. (eds) Proceedings of the Future Technologies Conference (FTC) 2022, Volume 2. FTC 2022 2022. Lecture Notes in Networks and Systems, vol 560. Springer, Cham. https://doi.org/10.1007/978-3-031-18458-1_11
Download citation
DOI: https://doi.org/10.1007/978-3-031-18458-1_11
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-031-18457-4
Online ISBN: 978-3-031-18458-1
eBook Packages: Intelligent Technologies and RoboticsIntelligent Technologies and Robotics (R0)