Abstract
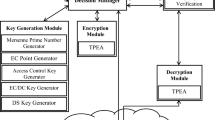
Cloud computing currently plays an increasingly important role in the information technology industry given its enhanced performance, wide accessibility, low cost, and many other benefits. Cloud computing provides a large storage space for data and ensures rapid processing of data to different users over the Internet. Cloud data security is a major ongoing challenge, which acts as a limiting factor for the extensive deployment of cloud computing. Thus, the problem selected for this work is enhancing data storage security in cloud computing with multiple methods to provide enhanced trusted, secure, and reliable cloud data storage services. In this paper, the framework for data security is mainly to protect data by combining double authentication for appropriate data classification and encryption and digital signature verification to analyze the integrity of the data during the transmission and retrieving processes. This analysis is performed through a certain message authentication code to ensure that the data are delivered without any alterations during transmission. An important contribution of this proposal is the different techniques and specialized procedures that can efficiently protect the data throughout the process, that is, from the owner to the cloud and then to the delivery to the end user. High-level security is achieved by double authentication as one by the user/owner and the other by the cloud. High-level security can enhance the performance of storing data in the cloud, particularly for certain important issues, such as data leakage, tampering of data, and preventing unauthorized access even from the cloud service provider.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Suciu, G., Suciu, V., Martian, A., Craciunescu, R., Vulpe, A., Marcu, I., Halunga, S., Fratu, O.: Big data, internet of things and cloud convergence–an architecture for secure e-health applications. J. Med. Syst. 39(11), 141 (2015)
Liu, Y., Xu, X.: Industry 4.0 and cloud manufacturing: a comparative analysis. J. Manuf. Sci. Eng. 139(3), 034701 (2017)
Guerrero-Ibanez, J.A., Zeadally, S., Contreras-Castillo, J.: Integration challenges of intelligent transportation systems with connected vehicle, cloud computing, and internet of things technologies. IEEE Wirel. Commun. 22(6), 122–128 (2015)
Fang, S., Da Xu, L., Zhu, Y., Ahati, J., Pei, H., Yan, J., Liu, Z.: An integrated system for regional environmental monitoring and management based on internet of things. IEEE Trans. Industr. Inf. 10(2), 1596–1605 (2014)
Botta, A., De Donato, W., Persico, V., Pescapé, A.: Integration of cloud computing and internet of things: a survey. Future Gener. Comput. Syst. 56, 684–700 (2016)
Ahmed, M., Hossain, M.A.: Cloud computing and security issues in the cloud. Int. J. Network Secur. Appl. 6(1), 25 (2014)
Khanezaei, N., Hanapi, Z.M.: A framework based on RSA and AES encryption algorithms for cloud computing services. In: 2014 IEEE Conference on Systems, Process and Control (ICSPC), pp. 58–62. IEEE, December 2014
Wang, H., Wu, S., Chen, M., Wang, W.: Security protection between users and the mobile media cloud. IEEE Commun. Mag. 52(3), 73–79 (2014)
Li, J., Chen, X., Li, M., Li, J., Lee, P.P., Lou, W.: Secure deduplication with efficient and reliable convergent key management. IEEE Trans. Parallel Distrib. Syst. 25(6), 1615–1625 (2014)
Talli, G., Porto, S., Carey, D., Brandonisio, N., Ossieur, P., Townsend, P., Bonk, R., Pfeiffer, T., Slyne, F., McGettrick, S., Blümm, C.: Technologies and architectures to enable SDN in converged 5G/optical access networks. In: 2017 International Conference on Optical Network Design and Modeling (ONDM), pp. 1–6. IEEE, May 2017
Dharani, P., Berlin, M.A.: Survey on secret sharing scheme with deduplication in cloud computing. In: 2015 IEEE 9th International Conference on Intelligent Systems and Control (ISCO), pp. 1–5. IEEE, January 2015
Shingare, M.M., Birajdar, P., Bibrale, H.: Hybrid cloud approach for secure authorized deduplication. Int. J. Eng. Sci. 7, 12766 (2017)
Eide, O.W.: Elliptic Curve Cryptography-Implementation and Performance Testing of Curve Representations. Master’s thesis (2017)
Rabah, K.: Implementing Elliptic Curve Digital Signature Algorithm (ECDSA) Schemes. Mara Res. J. Comput. Sci. Secur. 1(1), 29–50 (2017). ISSN 2518-8453
Gupta, D.S., Biswas, G.P.: A secure cloud storage using ECC-based homomorphic encryption. Int. J. Inf. Secur. Priv. (IJISP) 11(3), 54–62 (2017)
Wulf, J., Winkler, T.J., Brenner, W.: Measuring IT service management capability: Scale development and empirical validation (2015)
Khalilian, A., Ibrahim, O.: The state of data quality arts in (technical) service reporting. J. Theor. Appl. Inf. technol. 95(16) (2017)
Ab Rahman, N.H., Cahyani, N.D.W., Choo, K.K.R.: Cloud incident handling and forensic-by-design: cloud storage as a case study. Concurr. Comput. Pract. Exp. 29(14) (2017)
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2019 Springer Nature Switzerland AG
About this paper
Cite this paper
Jawad, M.S. (2019). Cloud Data Security Solution Based on Data Access Classification, Advanced Encryption Standard and Message Authentication Code. In: Arai, K., Bhatia, R., Kapoor, S. (eds) Proceedings of the Future Technologies Conference (FTC) 2018. FTC 2018. Advances in Intelligent Systems and Computing, vol 881. Springer, Cham. https://doi.org/10.1007/978-3-030-02683-7_12
Download citation
DOI: https://doi.org/10.1007/978-3-030-02683-7_12
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-030-02682-0
Online ISBN: 978-3-030-02683-7
eBook Packages: Intelligent Technologies and RoboticsIntelligent Technologies and Robotics (R0)